Why Phishing Domain Takedown Matters for Fintech in 2026
Key Takeaways
- Phishing threats evolve faster than traditional takedown processes can respond.
- Multi-channel attacks increase complexity and require centralized visibility.
- Continuous monitoring is essential to detect threats before they reach users.
- Automated enforcement improves response time and reduces operational overhead.
Phishing attacks targeting fintech users have evolved into high-speed, high-scale operations. Attackers now deploy thousands of fake domains and apps within hours. These assets impersonate login portals, payment flows, and customer support channels.
As a result, phishing domain takedown has shifted from a reactive task to a core security function. Financial brands face direct consequences when phishing succeeds. Customer trust erodes quickly, and fraud losses escalate.
According to organizations like the Anti-Phishing Working Group, phishing campaigns increasingly target financial platforms due to their immediate monetization potential. This trend reinforces the need for rapid disruption, not just detection.
Moreover, regulators now expect fintech companies to reduce customer exposure actively. Therefore, phishing mitigation for customers is no longer optional — it is measurable and auditable.
Why In-House Phishing Domain Takedown Fails
Most fintech teams attempt internal takedown workflows before considering external services. However, this approach consistently breaks down under real-world conditions.
Limited Visibility Across Domain Ecosystems
Internal tools rarely provide comprehensive visibility into newly registered domains, subdomains, and cloned apps. Attackers exploit this blind spot by launching campaigns faster than teams can detect them.
Legal and Registrar Complexity
Each domain registrar operates under different policies. Submitting abuse complaints requires precise evidence and formatting. Even then, response times vary significantly.
Guidance from the National Cyber Security Centre highlights how takedown success depends heavily on jurisdiction and provider cooperation. However, real-world execution is far more nuanced than standard guidance suggests.
Insights from PhishFort’s research — particularly “The Nuance of Takedowns” by Chad Los Schumacher — show that outcomes often depend on subtle factors such as hosting abuse patterns, registrar responsiveness, and whether a domain is maliciously registered or hosted on a compromised site. For example, strategies differ significantly when handling attacker-owned infrastructure versus legitimate websites that have been hijacked.
Additional deep dives like domain-related takedown workflows, compromised site strategies, and end-to-end domain takedown execution further illustrate why templated approaches fail in similar environments. Instead, effective phishing domain takedown requires adaptive playbooks, provider-specific escalation paths, and continuous optimization based on attacker behavior.
Resource Constraints in Fintech Security Operations
Security teams already manage fraud, compliance, and infrastructure risks. Adding manual takedown workflows creates bottlenecks and delays.
Fragmented Tooling and Lack of Automation
Without unified systems, teams rely on spreadsheets, emails, and disconnected tools. This fragmentation slows response times and increases error rates.
Delays That Increase Customer Exposure
Even a 24-hour delay can expose thousands of customers to phishing. In fintech, timing directly impacts fraud outcomes.
How Attackers Evade Brand Protection and Abuse Monitoring
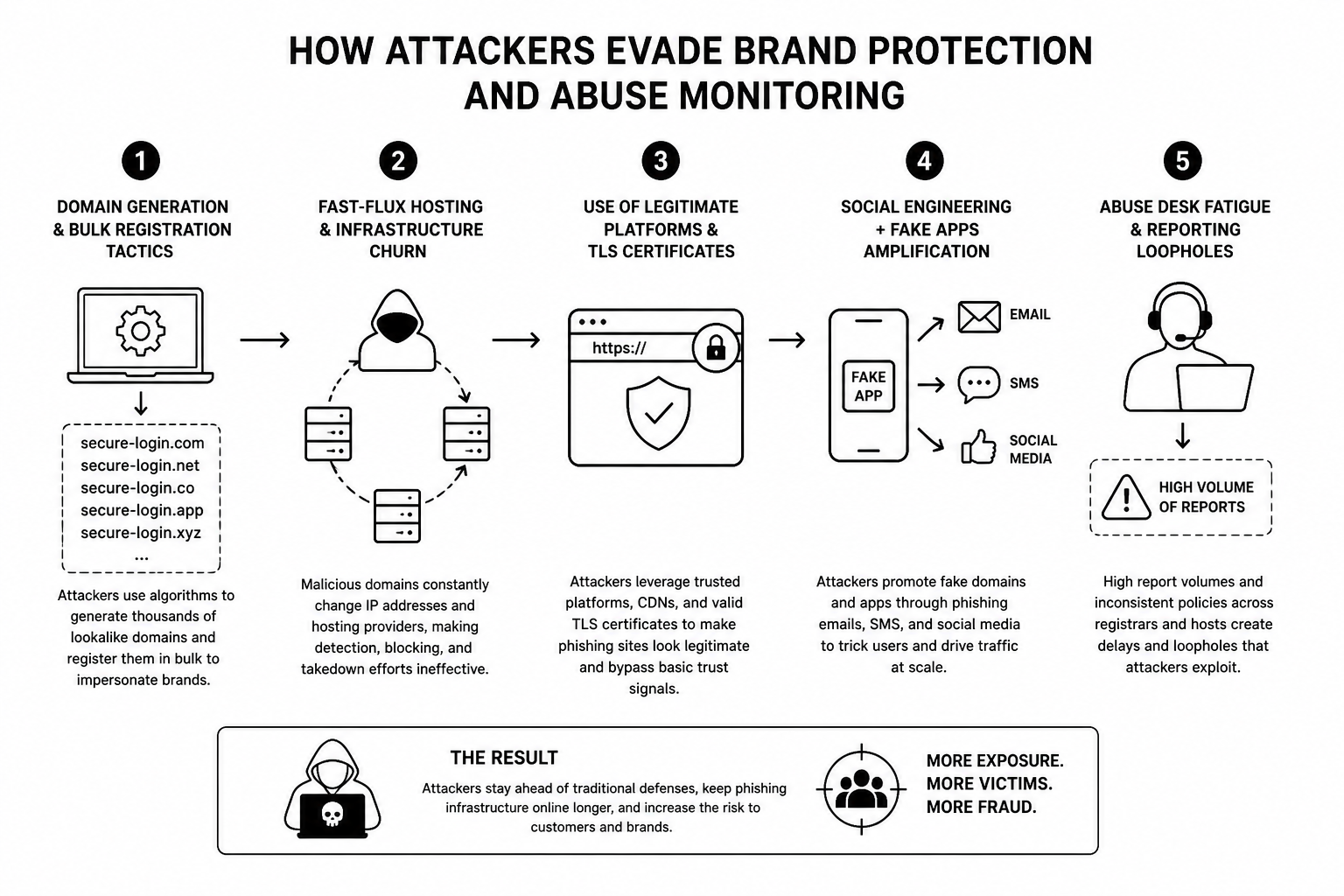
Attackers continuously refine their evasion tactics. Understanding these methods is essential for designing effective defenses.
Domain Generation and Bulk Registration
Attackers use automation to register hundreds of lookalike domains. Slight variations in spelling or structure bypass simple detection rules.
Fast-Flux Hosting and Infrastructure Churn
Malicious domains frequently change IP addresses and hosting providers. This tactic prevents consistent blocking and delays takedowns.
Abuse of Legitimate Platforms
Phishing sites often use trusted infrastructure, including cloud hosting and valid TLS certificates. This makes them appear legitimate to both users and systems.
Fake Apps and Multi-Channel Amplification
Attackers extend campaigns beyond domains. They distribute fake apps and use SMS or social media to drive traffic.
Abuse Desk Fatigue and Reporting Loopholes
High volumes of abuse reports overwhelm providers. Attackers exploit inconsistent enforcement and slow response cycles.
How Phishing Domain Takedown Services Actually Work
Phishing domain takedown services address the gaps left by in-house approaches. They operate as integrated systems rather than isolated processes.
Continuous Monitoring
These services scan domains, apps, and infrastructure in real time. They detect suspicious assets shortly after registration or deployment.
Threat Enrichment and Prioritization
Detected domains are analyzed using intelligence signals. Risk scoring helps teams focus on high-impact threats.
Automated Abuse Reporting
Instead of manual submissions, services generate and send abuse complaints automatically. This ensures speed and consistency.
Registrar and Hosting Escalation
Established relationships with providers improve response rates. Escalation paths accelerate takedown approvals.
Feedback Loops
Each takedown improves detection models. Over time, systems become more accurate and proactive.
From Detection to Disruption: The End-to-End Workflow
A structured workflow is essential for reducing phishing exposure effectively.
Step 1: Discovery
Monitoring systems identify suspicious domains and assets early.
Step 2: Validation
Security engines confirm phishing behavior using content and infrastructure signals.
Step 3: Prioritization
Domains are ranked based on potential customer impact.
Step 4: Abuse Submission
Automated systems submit evidence-backed reports to registrars and hosts.
Step 5: Takedown and Monitoring
Domains are suspended, and systems track reappearance attempts.
This workflow transforms detection into disruption, which is the ultimate goal.
Measuring Real Customer-Risk Reduction (Not Vanity Metrics)
Many organizations track the number of domains taken down. However, this metric alone does not reflect real impact.
Mean Time to Takedown (MTTT)
This measures how quickly threats are neutralized after detection.
Exposure Window Reduction
Shorter exposure times directly reduce the number of affected customers.
Phishing Click and Conversion Rates
Lower interaction rates indicate successful disruption.
Repeat Attack Suppression
Effective takedowns reduce the likelihood of attackers reusing infrastructure.
Customer Incident Volume
Fewer support tickets and fraud reports signal meaningful improvement.
Focusing on these metrics aligns takedown efforts with business outcomes.
What to Look for in Domain Takedown Services
Choosing the right provider requires careful evaluation.
Broad Coverage
Look for support across registrars, hosting providers, and app ecosystems.
Automation and APIs
Automation ensures speed and scalability. APIs enable integration with existing systems.
Intelligence Depth
Advanced enrichment improves prioritization and detection accuracy.
Fintech-Aligned Reporting
Reports should map directly to fraud and customer-risk metrics.
Integration with Security Operations
Seamless integration enhances efficiency and reduces manual work.
Building a Fintech-Ready Phishing Mitigation Strategy
A modern phishing mitigation strategy must go beyond detection and response. It needs to proactively reduce customer exposure, align with fraud prevention goals, and support regulatory compliance.
This is where specialized providers like PhishFort play a critical role. Instead of forcing fintech teams to build internal takedown operations, PhishFort delivers a scalable external defense layer designed for both traditional financial institutions and crypto-native platforms.
Combine Brand Protection with Customer-Centric Defense
Phishing mitigation is not just about removing domains. It is about protecting real users from credential theft, fake onboarding flows, impersonation scams, and wallet-draining attacks.
PhishFort continuously detects and dismantles phishing sites, fake apps, and brand impersonation campaigns before they scale. This ensures customers interact only with legitimate services across both financial and Web3 environments.
Align Takedown Workflows with Fraud and Compliance Teams
Fintech organizations operate under strict regulatory frameworks such as GDPR, PSD2, PCI DSS, and SOC 2. Therefore, phishing mitigation must support both fraud reduction and compliance reporting.
PhishFort provides compliance-ready documentation and measurable outcomes, helping teams reduce reportable incidents and demonstrate risk mitigation to regulators, auditors, and insurers.
Leverage Real-Time Intelligence with Human Validation
Automation alone is not enough. False positives and missed threats can undermine effectiveness.
PhishFort combines LLM-based detection with expert analyst validation, ensuring that suspicious domains, apps, and social accounts are accurately identified and rapidly taken down. This hybrid model improves both speed and precision.
Protect Revenue and Customer Trust at Scale
Phishing attacks do more than steal credentials — they divert transactions, damage brand reputation, and erode customer confidence.
By eliminating malicious infrastructure in real time, PhishFort helps ensure:
- Legitimate transactions remain secure
- Customer trust is preserved
- Revenue streams are protected from fraud disruption
Continuously Optimize Using Measurable Risk Reduction
A strong strategy is data-driven. PhishFort enables fintech teams to track:
- Mean time to takedown (MTTT)
- Threats neutralized before customer exposure
- Reduction in phishing-related incidents
- Financial risk avoided
These metrics are essential for board-level reporting, cyber insurance, and long-term security planning.
Take Action: Strengthen Your Phishing Defense
Fintech threats vary across traditional finance and Web3 ecosystems. Choose the solution tailored to your environment:
👉 For banks, fintech apps, and payment platforms.
👉 For crypto, exchanges, and Web3 platforms.
- Detect phishing infrastructure in real time
- Remove fake domains and apps before customers are impacted
- Achieve measurable reductions in fraud and exposure
- Stay compliant with evolving financial regulations



