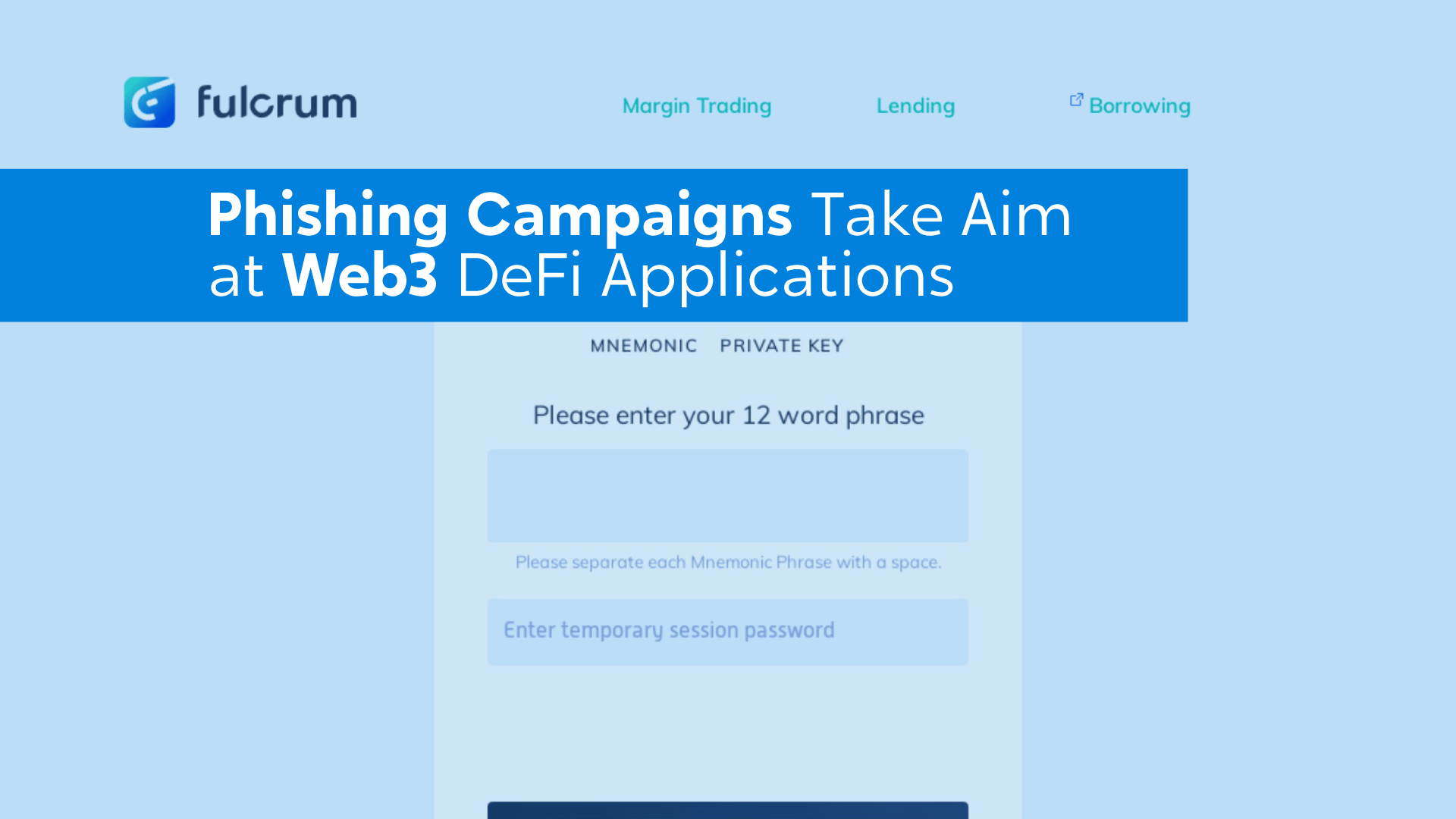
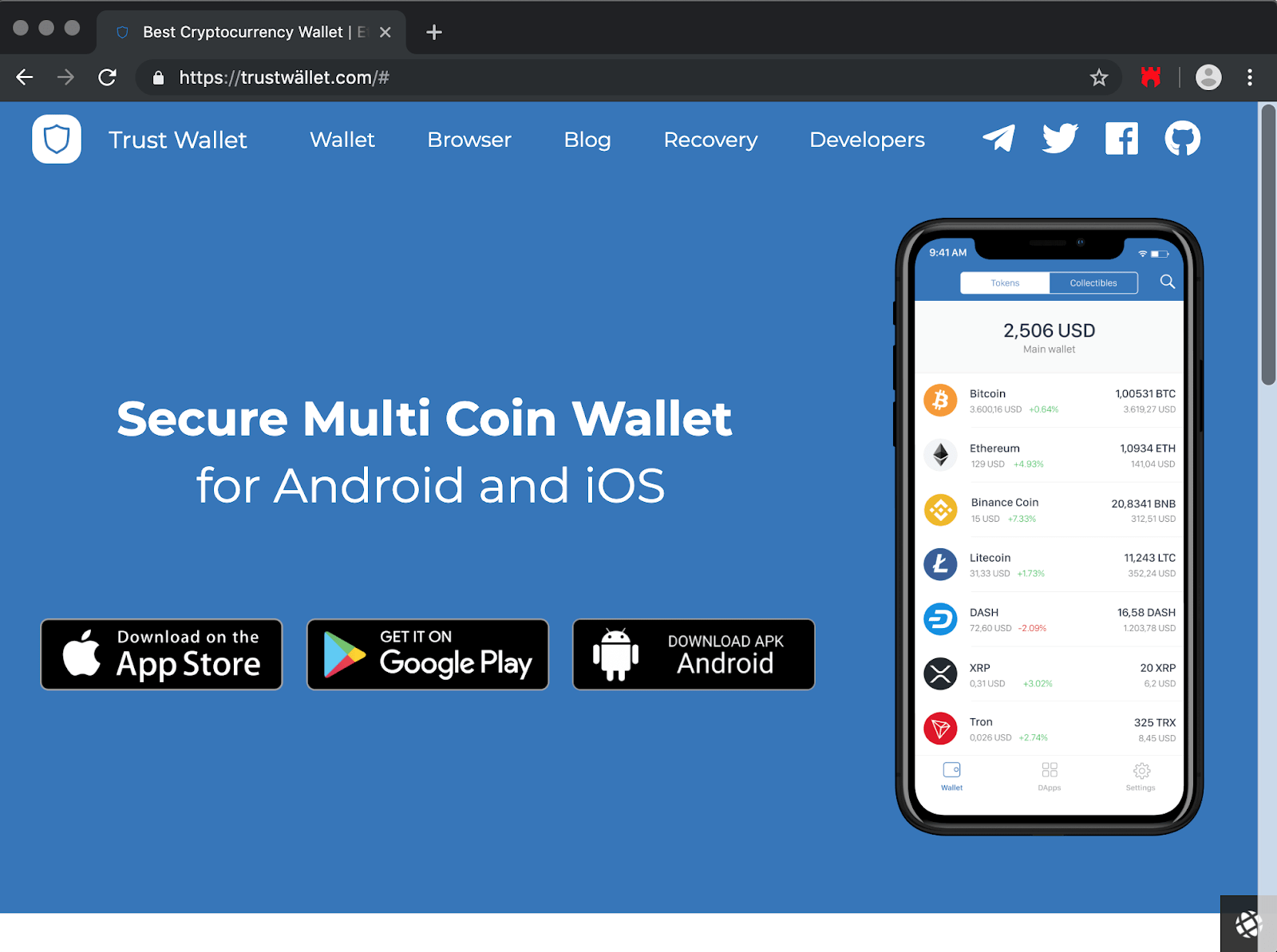
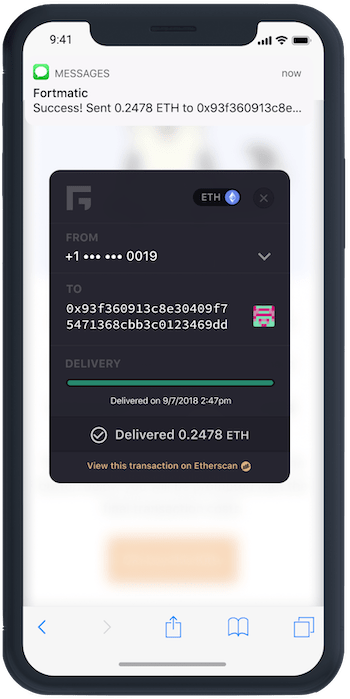
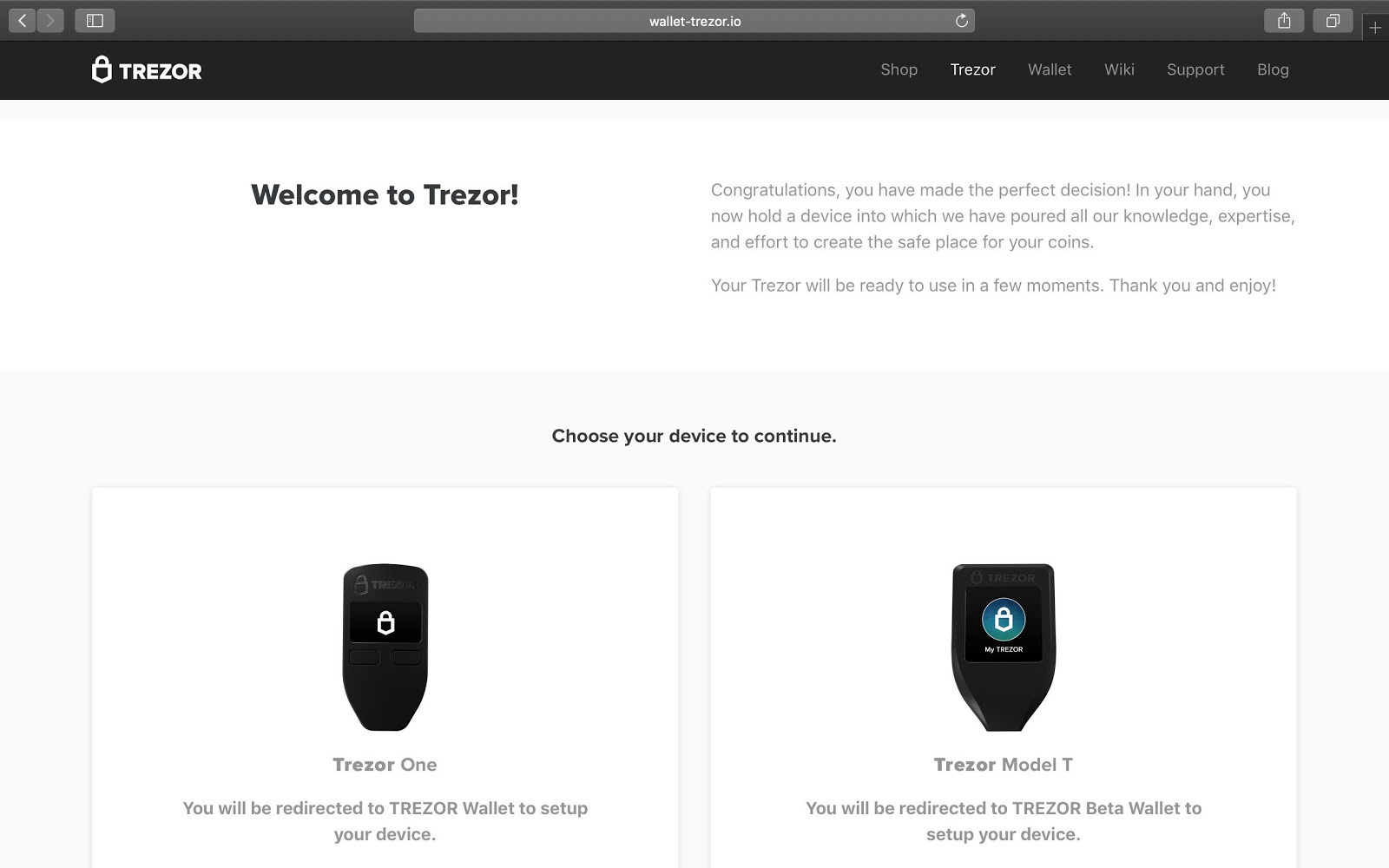
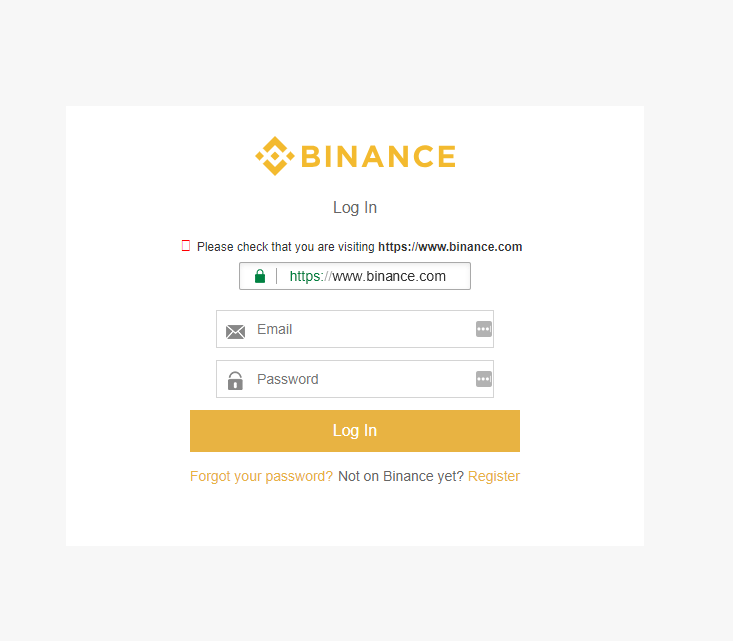
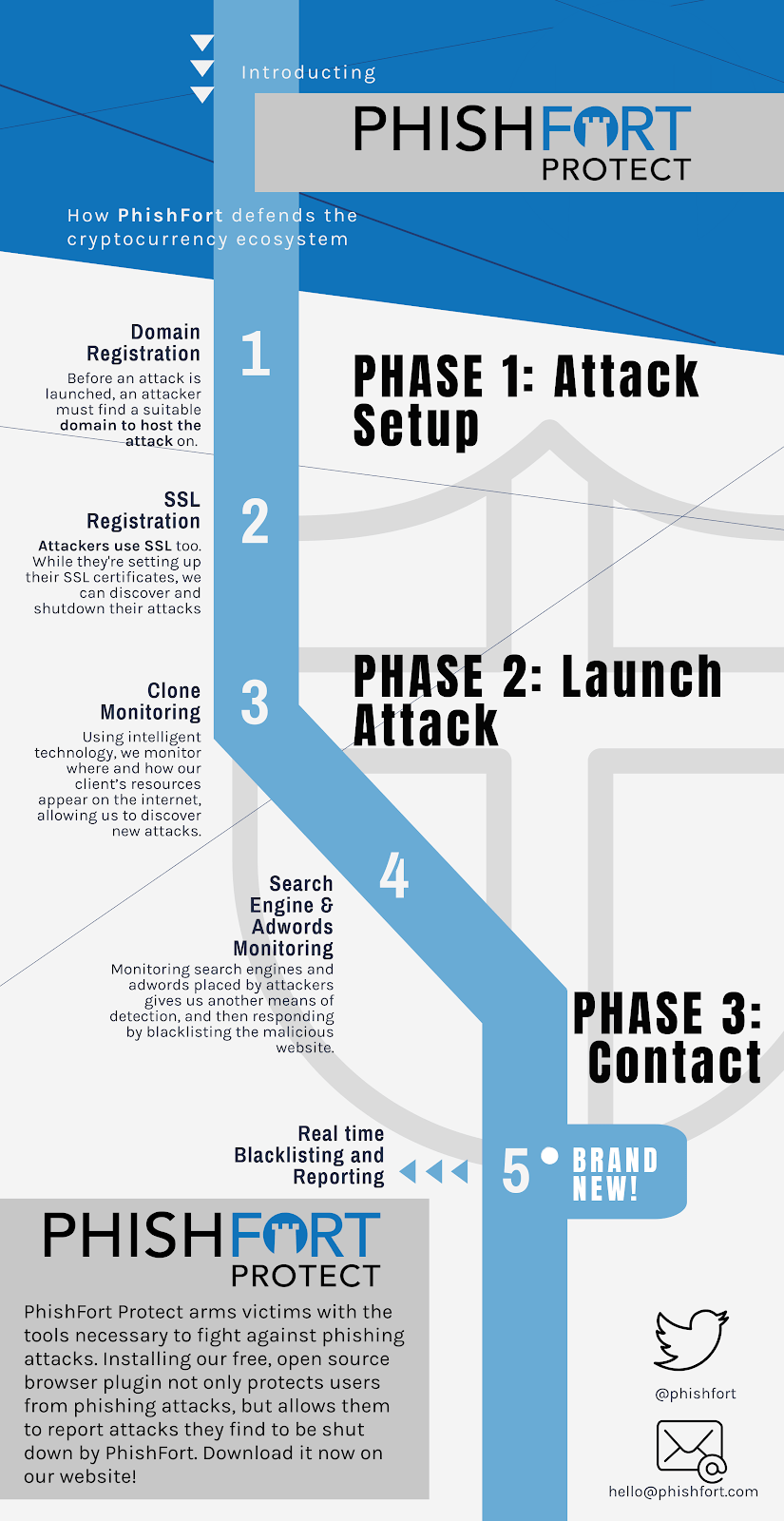
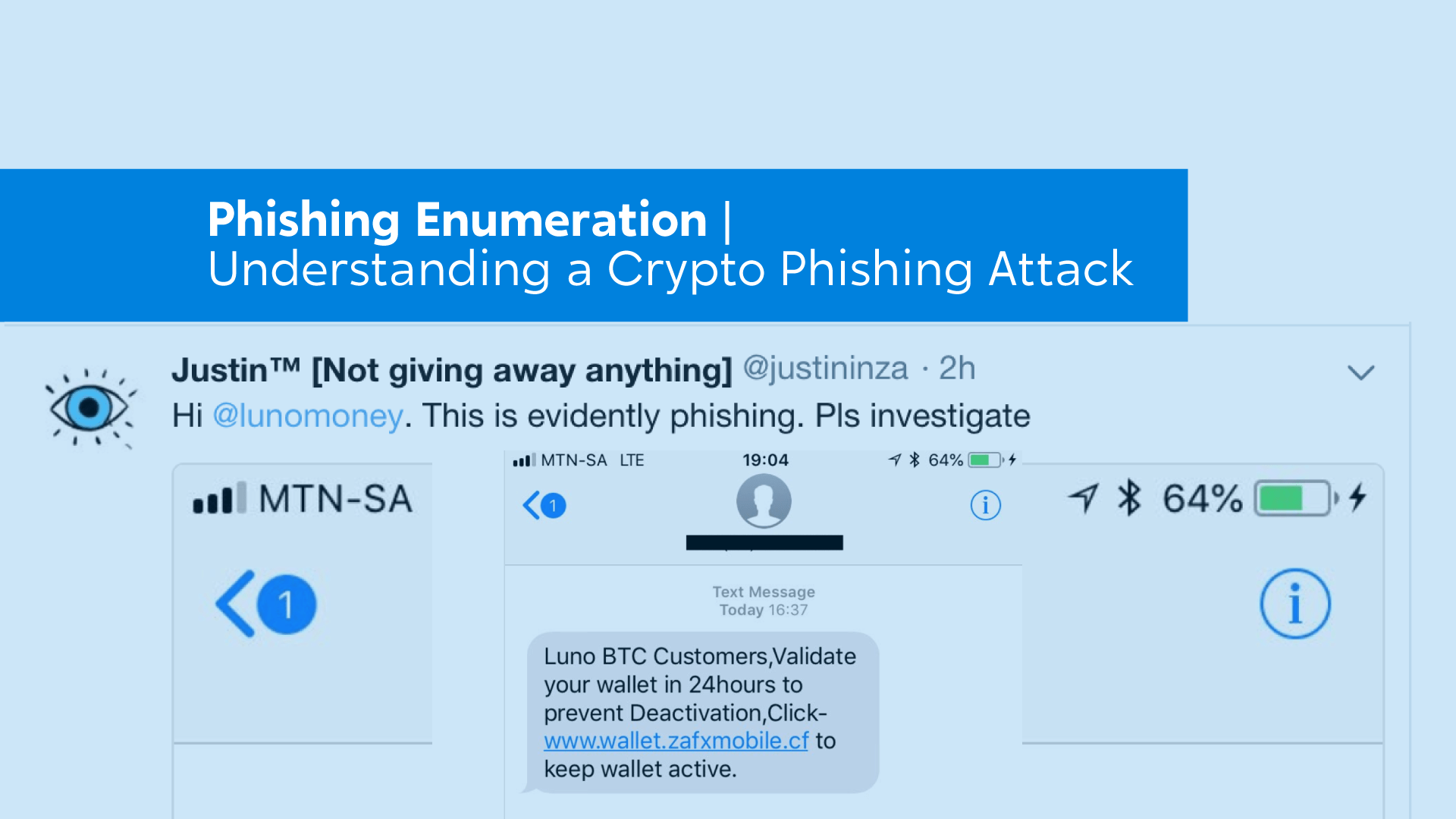
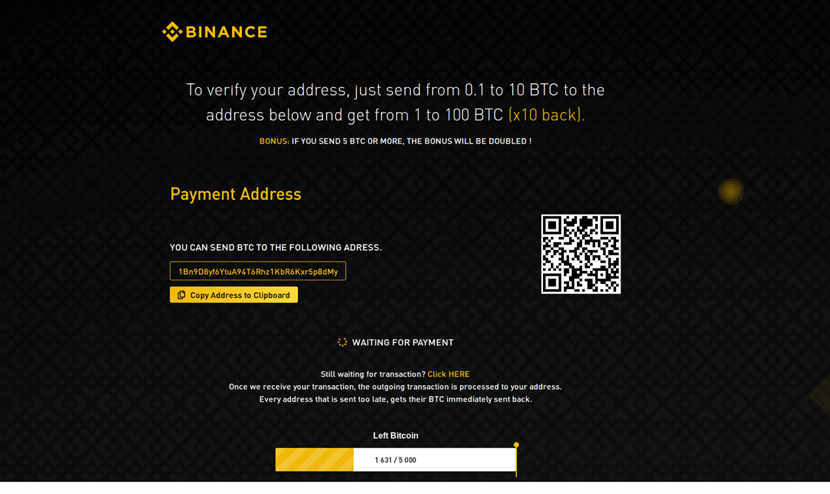
The New Face of Phishing: Fake Investment Platforms
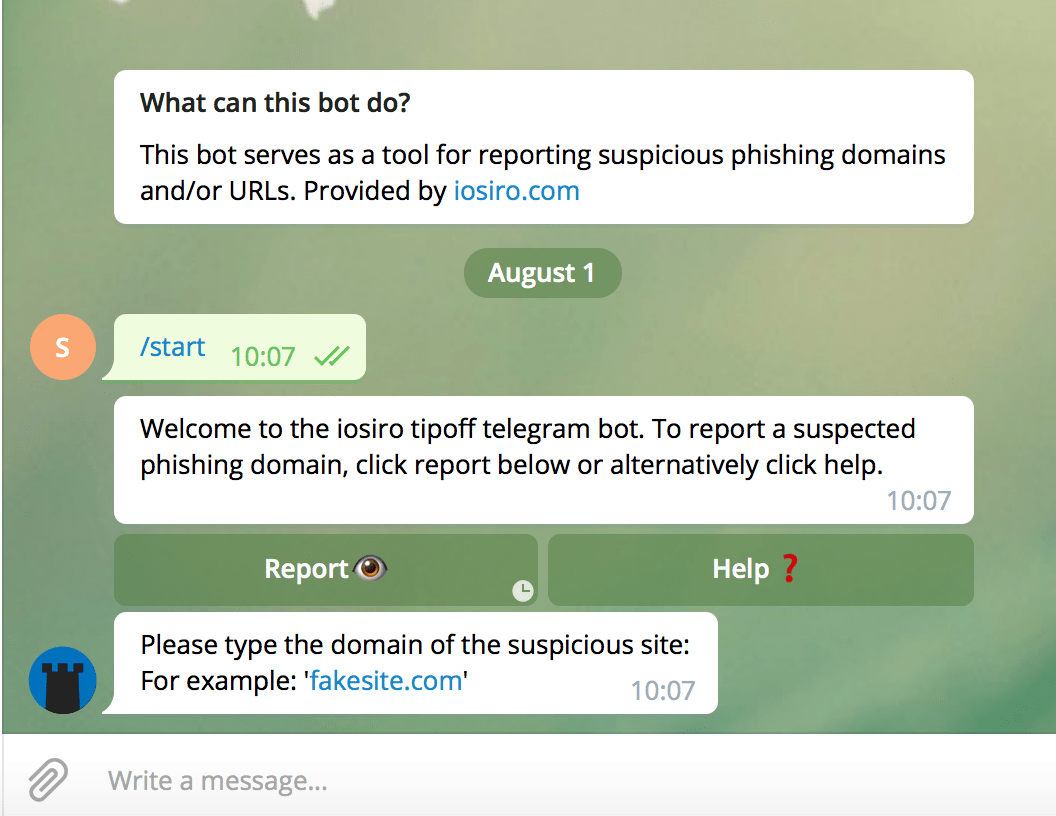
Fake investment platforms are a new form of phishing where attackers impersonate financial firms to steal data and funds. Learn how they work and how to detect them.
Read more: The New Face of Phishing: Fake Investment Platforms