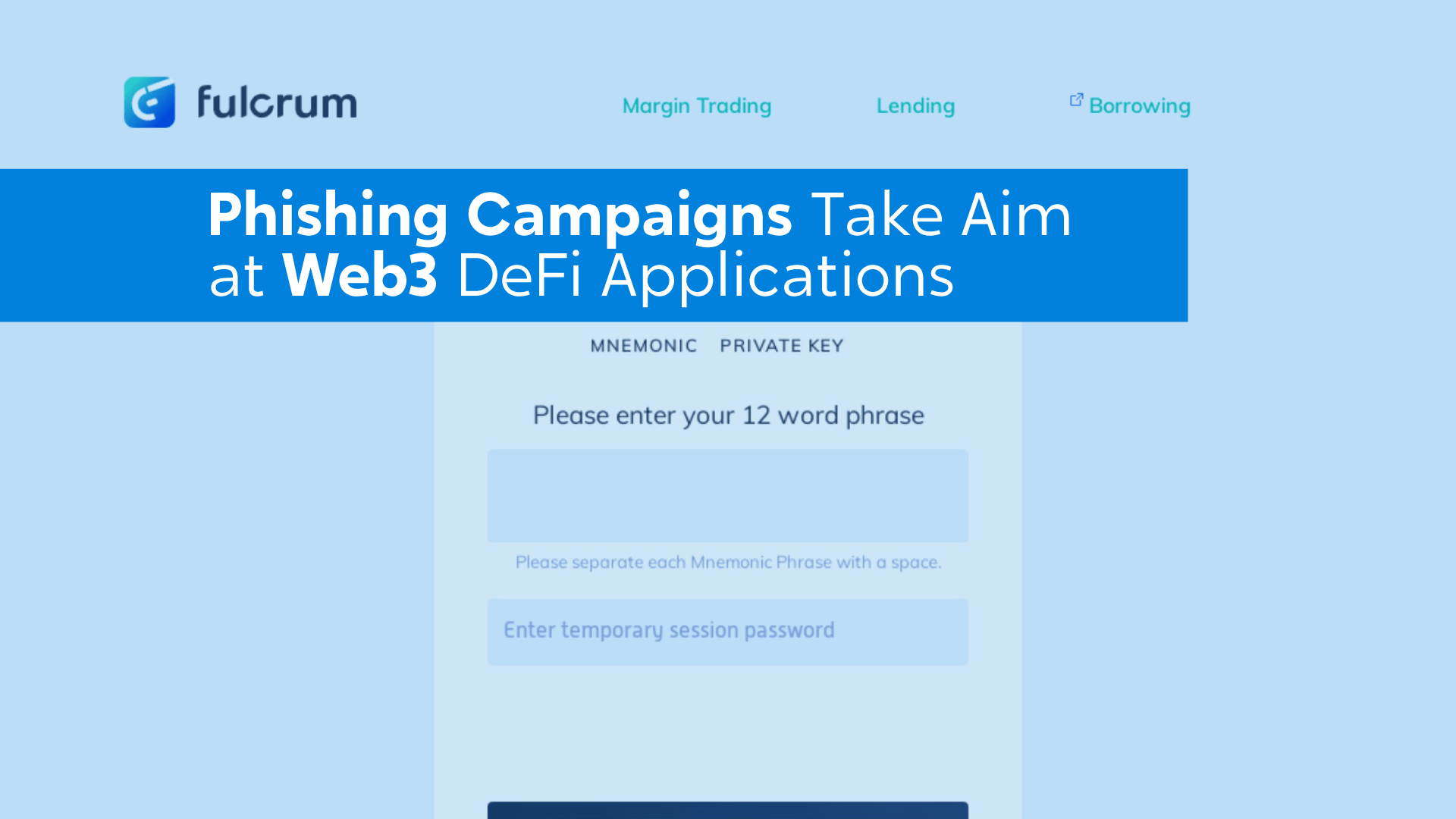
Living Off the Land Attack: How Trusted Platforms Are Fueling Phishing
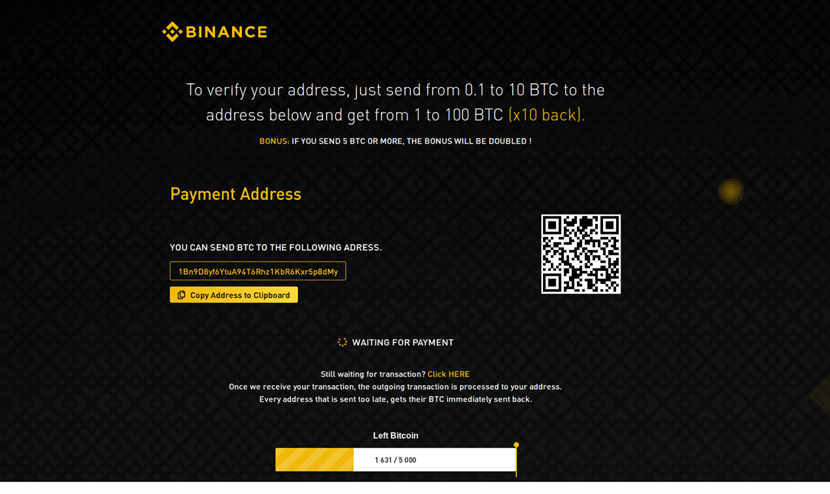
Living off the land attacks use trusted platforms like Google Sites and Vercel to host phishing scams. Learn how they work and how to stay safe.
Read more: Living Off the Land Attack: How Trusted Platforms Are Fueling Phishing