In an era where cybercriminals can mirror a global brand in minutes, brand protection services have transitioned from a luxury to a fundamental business necessity. These services provide the technical framework required to identify, analyze, and neutralize external threats that exist outside your traditional network perimeter—specifically targeting your reputation, intellectual property, and customer trust.
Key Takeaways
- Visual Deception is Evolving: Attackers now use high-quality video and deepfake formatting to bypass human skepticism.
- Infrastructure is Shared: Modern scam clusters often hide on the same technical infrastructure, allowing for bulk detection.
- Automated Evasion: Threat actors use Unicode and living-off-the-land tactics (abusing legitimate platforms like GitHub or Meta) to stay invisible.
- Rapid Takedowns are Critical: The value of brand protection is measured by the speed at which a fraudulent asset is removed before it scales.
What are Brand Protection Services?
Brand protection services are specialized cybersecurity solutions that monitor the digital landscape to detect unauthorized use of a brand’s identity. Unlike internal security, these services focus on the external attack surface: finding fake websites, fraudulent social media profiles, and impersonation apps that aim to defraud your customers.
Using advanced phishing detection and visual pattern clustering, these services can spot a scam before it ever reaches a victim’s inbox or social feed.
How Does Paid Advertisement Exploitation Work?
Threat actors utilize legitimate advertising platforms, primarily Facebook and Instagram, to broadcast fraudulent offers. These campaigns are often highly targeted by geography and demographics to maximize their reach among specific potential victims.
To succeed, they use two primary methods of deception:
- Creative Deception: Attackers use high-quality brand logos, stolen promotional videos, and deepfake-style formatting to mirror official brand aesthetics perfectly.
- Filter Evasion: To avoid detection by automated brand-protection tools, scammers use Unicode or Cyrillic characters that look identical to the Latin alphabet (e.g., using a Cyrillic “е” in the brand name).
What Role Does Fabricated Social Proof Play in Scams?
A critical component of modern scams is the use of fake engagement to instill immediate trust in the target. If a user sees an ad with thousands of likes and positive comments, their natural defenses lower.
Scammers deploy aged or compromised profiles that post comments claiming to have successfully received the advertised prize. This artificial engagement makes a fraudulent ad appear viral and legitimate to a casual observer, even if the underlying offer is mathematically impossible.
Why are High-Value Flash Sales Used for Data Harvesting?

Attackers frequently promote luxury items or high-demand electronics (like Dyson vacuum cleaners) at impossible price points—such as 50€ instead of 1000€. These are rarely about stealing the small purchase price; they are designed for PII (Personally Identifiable Information) disclosure.
These fake sales harvest:
- Credit card details (full PAN/CVV).
- DNI/National ID numbers.
- Full contact information for secondary phishing attacks.
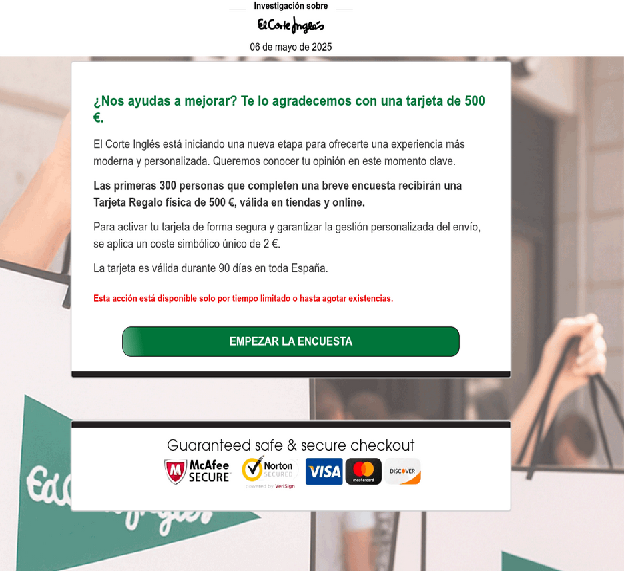
How Do Event-Driven Scams Use Pressure Tactics?
Scammers synchronize their activities with the retail calendar to exploit heightened consumer activity. This includes both legitimate holidays like Black Friday and fabricated milestones like an anniversary giveaway.
| Tactic | Description | Psychological Trigger |
|---|---|---|
| Countdown Timers | “Offer expires in 05:00” | Urgency/Panic |
| Limited Availability | “Only for the first 300 users” | FOMO (Fear of Missing Out) |
| Event Alignment | “Store Opening Celebration” | Rationalization of high discounts |
What are the Technical Red Flags of Deceptive Landing Pages?
Once a user clicks an ad, they are routed through redirects to hide the final destination from security crawlers. Professional brand protection services look for specific technical anomalies that reveal the scam:
- Non-Standard Domains: Use of TLDs like .world, .click, .xyz, or .vip which are easy to register in bulk.
- Cloaking and Geofencing: Scam pages show different content to security bots than they do to real users, or they block traffic from certain IP ranges to avoid detection.
- Living off the Land: Scams abusing legitimate service providers like ZenDesk, GitHub, or Instagram to host fraudulent payloads.
How to Implement an Adaptive Brand Defense Strategy?
An effective defense requires an adaptive automation loop that is retrained weekly to stay ahead of shifting tactics. This involves documenting all findings in a central incident log to facilitate rapid response and takedown procedures.
By combining visual pattern clustering with granular targeting filters, brands can identify emerging scam clusters in real-time. This collaborative feedback loop ensures that detection accuracy improves with every new attack pattern identified.
Frequently Asked Questions (FAQs)
What is the most common sign of a brand impersonation ad?
The most common signs are prices that are too good to be true, the use of urgency (timers), and a URL that uses a non-standard TLD or misspelled brand name (e.g., brand-deals.xyz).
How do attackers evade automated brand protection filters?
They often use homoglyphs (Unicode characters that look like Latin letters) or host their content on legitimate platforms like Google Docs or GitHub to live off the land and avoid being flagged as malicious.
Why is PII harvesting more dangerous than a simple fake sale?
While losing 50€ is bad, having your National ID and credit card details stolen allows attackers to perform identity theft, open fraudulent accounts, and sell your data on the dark web.
Conclusion & Next Steps
Digital impersonation has evolved into a sophisticated, automated industry. Protecting your brand requires more than just reactive monitoring; it requires a proactive, technical approach to identifying the infrastructure of fraud. By understanding the tactics of visual deception, social proof manipulation, and technical cloaking, your organization can stay one step ahead of threat actors.
Our commitment to protecting brand integrity involves a continuous strategy covering every vector outlined in this guide.
Ready to neutralize brand threats at scale? Explore our specialized security solutions today .



