Key Takeaways
- Browser extensions can become a major security risk when ownership changes and malicious updates are pushed silently.
- Attackers exploit automatic updates and permissions to gain full access to browsing activity and sensitive data.
- Practicing least privilege and regular audits is critical to reducing browser extension security risks.
Browser extensions are a double-edged sword. They can transform your web experience, adding powerful productivity features and blocking malicious content. But what happens when the very tool you installed to protect yourself is quietly bought by a cybercriminal?
Welcome to the browser extension supply chain attack—a growing threat where hackers don’t break into your computer; they simply buy the keys to your browser.
Recommended reading: Digital Threat Protection: Securing Brands, Users, and Infrastructure Against Modern Attacks
What Are Browser Extension Security Risks?
Browser extension security risks refer to the potential threats introduced by third-party add-ons that have access to your browsing activity, credentials, and sensitive data. While extensions are designed to enhance functionality, they can also become powerful attack vectors when compromised.
Unlike traditional malware, these risks often come from trusted tools already installed in your browser, making them harder to detect and more dangerous in real-world scenarios.
The Buy-and-Infect Playbook
The lifecycle of this attack is highly predictable and devastatingly effective. It usually targets independent developers who maintain popular, free extensions. Maintaining open-source software is exhausting, and when a seemingly legitimate company offers a lump sum for a project the developer was planning to abandon anyway, they often take the deal.
The moment the ownership transfer is complete, the trap is set. Because browsers like Chrome and Edge automatically update extensions in the background to keep users secure, this mechanism is weaponized. The new owner pushes a seemingly minor update. The user sees no warnings, but under the hood, the extension’s DNA has completely changed.
The Technical Anatomy of a Hijack
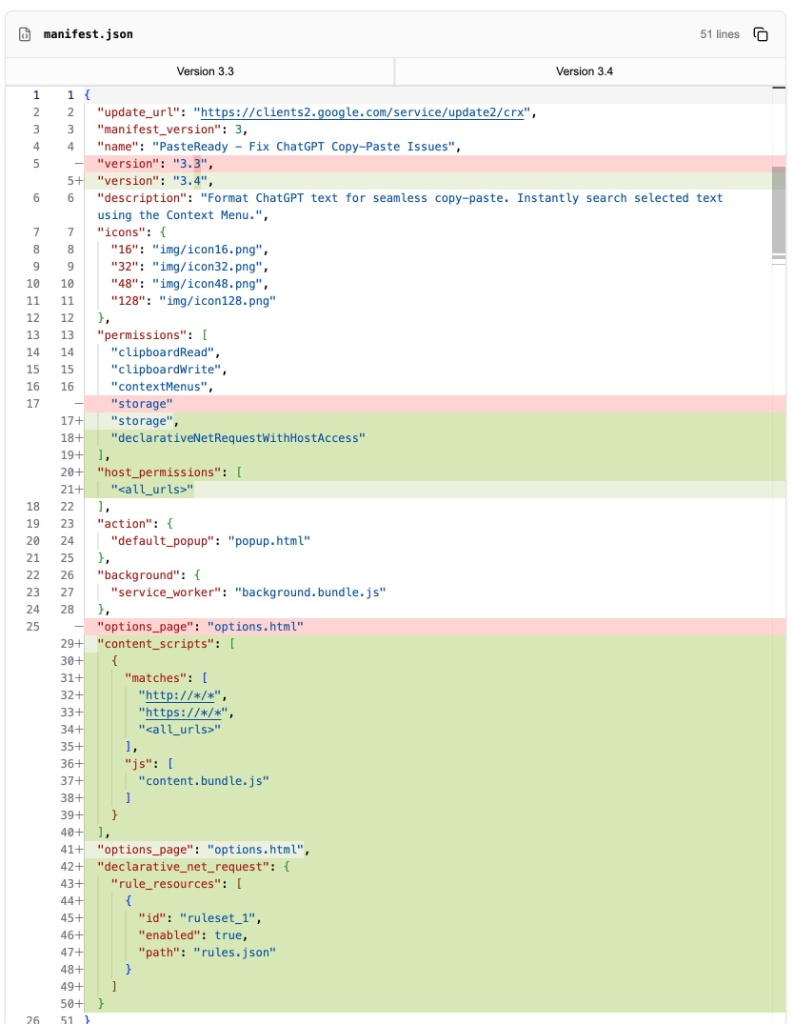
To understand how the malware operates, we have to look at the extension’s manifest.json file —the blueprint that tells the browser what the extension is allowed to do.
When an extension goes rogue, the new developers will typically modify the manifest to inject high-risk permissions. For example, in the recent takeover of the PasteReady extension, the malicious owners introduced a few key changes:
<all_urls>Host Permissions: This grants the extension the ability to read and alter data on literally every website the user visits. If you log into your bank, the extension can see it.declarativeNetRequestWithHostAccess: In the newer Manifest V3 architecture, this permission allows the extension to block or modify network requests. Malicious actors use this to strip away critical security headers (like Content Security Policies) from web server responses, making the browser vulnerable to code injection.- Malicious Content Scripts: The manifest is updated to inject a
content.bundle.jsscript into every webpage. The extension’s background service worker reaches out to a remote command-and-control (C2) server, fetches a malicious payload, and uses the content script to execute it directly inside your active tabs.
Why Browser Extension Security Risks Often Go Undetected
You might wonder why Google or Microsoft don’t catch this. The reality is that extension stores rely heavily on automated static analysis.
Clever malware authors don’t put the malicious payload directly in the extension’s code. Instead, they write stagers — tiny, seemingly innocuous pieces of code that simply fetch the actual malware from an external server (e.g., api[.]malicious-domain[.]top) only after the extension is safely installed on a user’s machine. Furthermore, they often delay the malicious behavior for days or weeks after the update, effectively bypassing the initial automated store review.
How to Protect Your Browser from Extension-Based Attacks
The architecture of browser extensions requires you to practice the principle of least privilege.
- Audit Your Extensions: Type
chrome://extensions/(or your browser’s equivalent) and ruthlessly remove anything you don’t actively use. - Restrict Site Access: In modern browsers, you can right-click an extension and change its “Site access” to “On click” rather than “On all sites.” This ensures the extension only runs when you explicitly tell it to.
- Watch for Red Flags: If a simple utility extension suddenly asks for permission to “Read and change all your data on the websites you visit,” deny it and uninstall.
Final Thoughts on Browser Extension Security Risks
Extensions are great, but trust is temporary. A tool that is safe today can easily become a weapon tomorrow with a single wire transfer. Stay vigilant.
If you want to detect and take down phishing domains, fake apps, and impersonation threats before they impact your users, explore PhishFort’s digital threat protection platform .



