Chrome extension phishing is a deceptive cyber-attack where a seemingly legitimate browser add-on is weaponized to steal sensitive data, harvest credentials, or inject malicious code into your browsing session. These attacks often occur through supply chain takeovers, where hackers purchase popular, trusted extensions from original developers and push malicious updates to thousands of unsuspecting users automatically.
Key Takeaways
- The Buy-and-Infect Strategy: Cybercriminals often buy popular extensions to gain immediate access to an established user base.
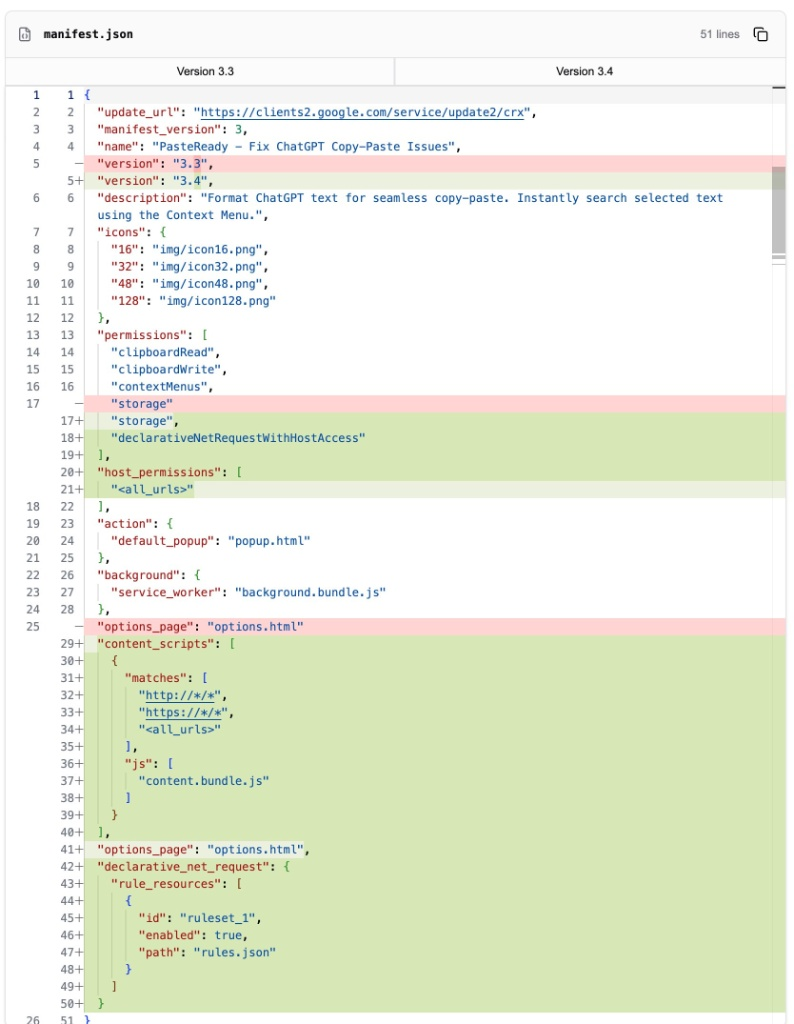
- Permission Inflation: Malicious extensions exploit the manifest.json file to gain high-risk permissions like
<all_urls>. - Stealth Execution: Modern phishing extensions use stagers to fetch malware from remote servers after the initial store review.
- Zero-Trust Browsing: Protecting yourself requires auditing extensions and restricting site access to on-click only.
What is Chrome Extension Phishing?
Chrome extension phishing is a specialized form of social engineering and technical exploitation where a browser add-on acts as a Trojan Horse to intercept user data. Unlike traditional phishing emails that lead to a fake website, this method lives directly inside your browser.
Because extensions sit between you and the web, they can read everything you type—including passwords, private keys, and credit card numbers. By 2026, these attacks have become more sophisticated, often targeting Web3 and DeFi users by swapping out wallet addresses during transactions.
How Do Malicious Browser Extensions Bypass Store Security?
Malicious browser extensions bypass store security by using delayed execution and external payload fetching. Most extension stores, including the Chrome Web Store and Microsoft Edge Add-ons, use automated static analysis to scan code for known malware patterns during the submission process.
To circumvent this, attackers write stagers. These are tiny, innocuous blocks of code that pass all security checks because they don’t contain a malicious payload. Once the extension is installed on your machine and the initial review phase is over, the stager reaches out to a remote Command-and-Control (C2) server to download the actual phishing scripts.
What are the Technical Signs of a Hijacked Extension?
The primary technical signs of a hijacked extension are unauthorized modifications to the manifest.json file and suspicious network requests to unknown domains. The manifest file is the blueprint of an extension; when a tool is bought and infected, the new owners will often escalate permissions to gain total control over your browsing data.
| Permission / Indicator | Risk Level | Description |
| <all_urls> | Critical | Allows the extension to read and change data on every website you visit. |
| declarativeNetRequest | High | Can be used to strip security headers (like CSP) from servers. |
| Remote JS Injection | Critical | Scripts fetched from external APIs to execute in your active tabs. |
| Background Workers | Medium | Persistent processes that run even when the extension isn't in use. |
Why is the Browser Extension Supply Chain So Vulnerable?
The browser extension supply chain is vulnerable because it relies on the transfer of trust between independent developers and anonymous corporate buyers. Many popular extensions are maintained by single developers as side projects. When these developers experience burnout, they are often approached by fake marketing firms offering significant sums of money for the extension.
Once the ownership transfer is complete, the trust you placed in the original developer is inherited by the attacker. Because browsers update extensions automatically in the background, the malicious code is delivered directly to your device without a single warning pop-up.
How Can You Detect Phishing in Your Browser Extensions?
You can detect phishing by performing a manual audit of your installed extensions and monitoring for “Permission Creep.” If a simple calculator or dark-mode extension suddenly requests permission to “Read and change all your data on all websites,” it is a major red flag that the extension has likely changed hands or been compromised.
| Detection Method | What to Look For |
| Audit Log Check | Unexpected updates or changes in the "Developer" contact info. |
| Network Monitoring | Extensions communicating with suspicious or non-standard APIs. |
| Permission Review | Extensions asking for more access than their core function requires. |
What are 7 Best Practices for Browser Extension Security?
The best practices for browser extension security include adopting the principle of least privilege and performing regular technical hygiene on your browser profile.
- Ruthless Auditing: Visit
chrome://extensions/monthly and delete anything you haven’t used in 30 days. - Restrict Site Access: Right-click an extension icon, go to “This can read and change site data,” and select “When you click the extension.”
- Check Developer Reputation: Research the current owner. If a project was recently sold to an unknown entity, uninstall it.
- Use Official Tools Only: Only download extensions from verified developers or official company accounts.
- Monitor for Alerts: Pay attention to browser warnings that an extension is “No longer supported” or “Removed from store.”
- Use Dedicated Profiles: Keep a “clean” browser profile for banking and sensitive work with zero extensions installed.
- Install Protection Layers: Use security-focused extensions like PhishFort’s Nighthawk that are specifically designed to block malicious domains.
Can Organizations Prevent Chrome Extension Phishing at Scale?
Organizations can prevent Chrome extension phishing at scale by implementing Enterprise Browser Management and Allow-Listing policies. Relying on individual employees to vet their own extensions is a recipe for a data breach.
Security teams should use Group Policy Objects (GPO) or MDM solutions to enforce a Block All policy, allowing only a vetted list of essential extensions. Furthermore, Digital Risk Protection Services (DRPS) can monitor the web for clone extensions that impersonate corporate tools to target employees.
Frequently Asked Questions (FAQs)
Can a browser extension steal my passwords?
Yes, if an extension has the “Read and change all your data on the websites you visit” permission, it can capture every keystroke you enter into login forms, including passwords and 2FA codes.
Why did my extension suddenly ask for new permissions?
This usually happens when an extension has been updated. While some updates add legitimate features, a sudden jump to high-risk permissions is a common sign of a supply chain attack or a hijacked extension.
Is it safe to use free browser extensions?
Many free extensions are safe, but they are the primary targets for buy-and-infect attacks. If a free extension lacks a clear monetization strategy, the product being sold might eventually become your data.
How do I report a malicious Chrome extension?
You can report an extension directly through the Chrome Web Store by clicking Report Abuse on the extension’s store page. Providing details about suspicious behavior helps Google remove the threat faster.
Conclusion & Next Steps
Chrome extension phishing represents a critical blind spot in modern cybersecurity. These tools, which we use to enhance our digital lives, can easily be turned into powerful surveillance devices. By practicing the principle of least privilege — restricting site access and auditing your tools — you can close the door on supply chain attackers.
Protecting your brand and your users from these deceptive threats requires proactive monitoring and rapid response. Don’t wait for a data breach to audit your digital perimeter.
Would you like to see how we can safeguard your community from impersonation and phishing? Explore our Brand Protection Solutions today.



