The rise of digital asset theft has birthed a secondary, equally predatory industry: the crypto asset recovery scam. For victims who have already lost funds to a hack or a fraudulent exchange, the promise of getting their money back is a powerful lure. However, the reality of the blockchain is that most “recovery” offers are simply a second stage of the initial attack. Understanding the importance of crypto asset recovery is vital for anyone navigating this landscape.
The cryptocurrency space continues to attract not only innovators and investors but also sophisticated scammers. Each year, crypto users lose millions of dollars to so-called “tech support” or “recovery” scams, where fraudsters impersonate legitimate blockchain or wallet support teams. These attacks typically begin with unsolicited contact — via Twitter/X direct messages, Discord servers, fake emails, or even poisoned search results — warning victims of urgent issues like “stuck transactions,” “wallet syncing problems,” “migration errors,” or “funds at risk.” The need for crypto asset recovery solutions has never been more pressing.
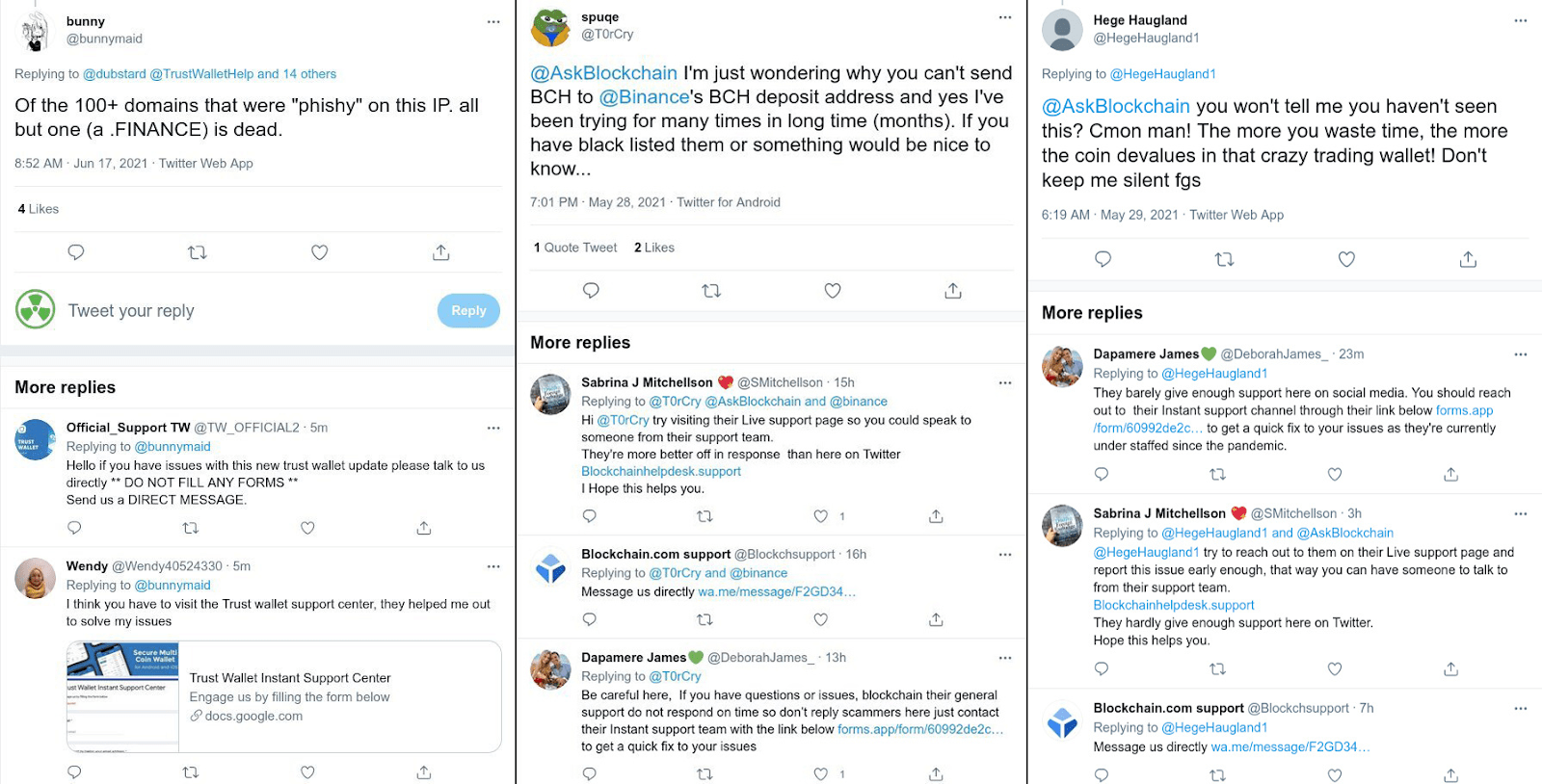
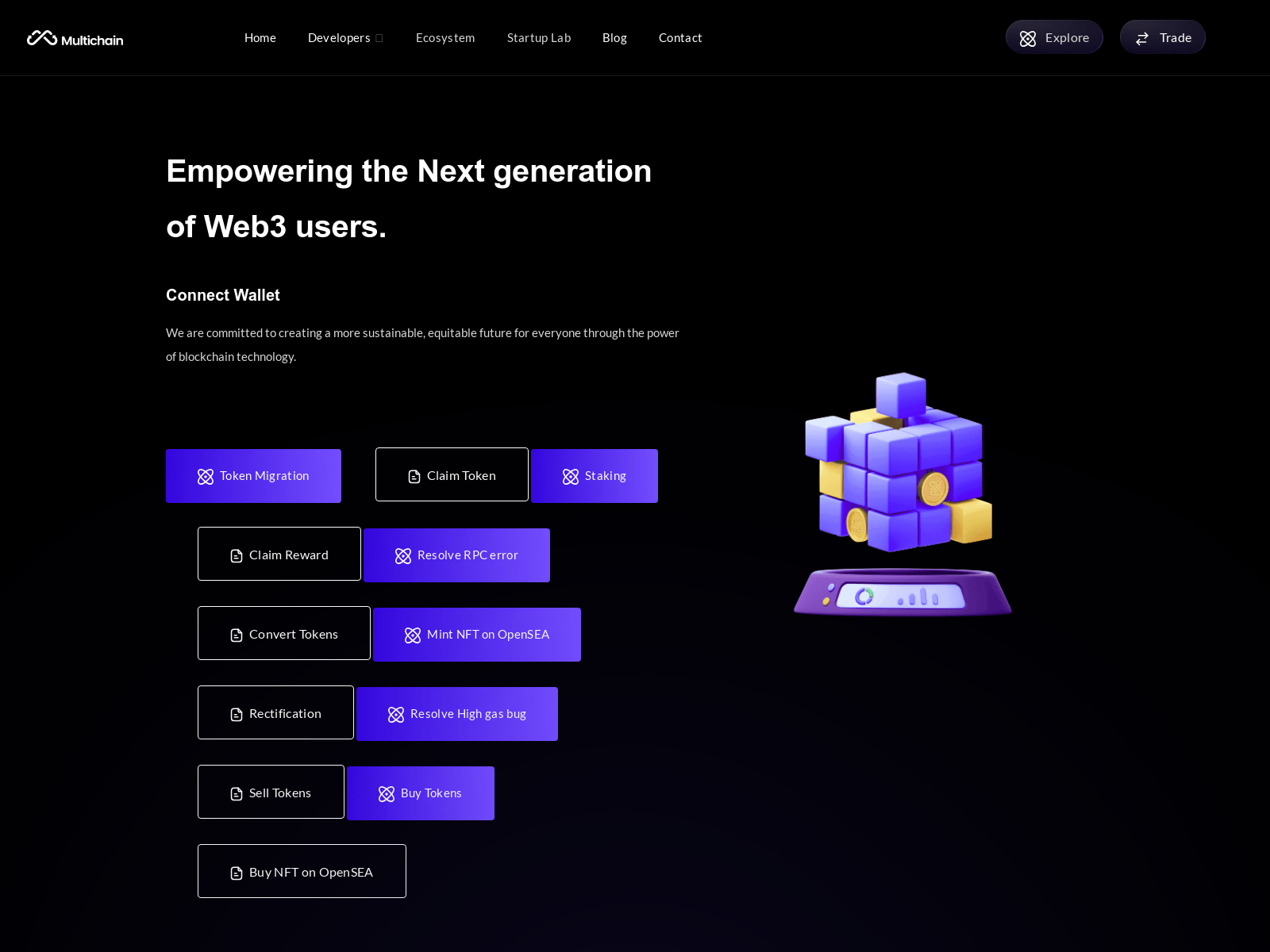
Panicked users are then directed to fraudulent websites that promise quick fixes, only to result in drained wallets. What makes these campaigns particularly insidious is their generic nature. Unlike targeted attacks aimed at a single exchange (e.g., Binance or Coinbase) or wallet brand, these scams cast a wide net across the entire crypto ecosystem. They prey on anyone holding digital assets by offering broad “solutions” such as blockchain rectification, node setup, wallet recovery, or multi-chain syncing — none of which require legitimate technical intervention from real support teams. Protecting your assets through legitimate crypto asset recovery services is essential.
At Phishfort, our mission is to provide visibility into these blind spots. To illustrate this persistent threat, we analyzed several suspected phishing pages, and these are the most common patterns that emerge from the attacks.
For anyone affected by crypto asset recovery scams, it is crucial to seek professional assistance to navigate the complex landscape of digital asset recovery.
Recognizing the signs of a scam can greatly aid in the process of crypto asset recovery. Awareness is the first step toward securing your assets.
Victims who understand the importance of crypto asset recovery are more likely to act swiftly and effectively to mitigate their losses.
Many organizations specialize in crypto asset recovery and can guide you through the necessary steps to reclaim your funds.
Common Patterns & Red Flags: The Social Engineering Core
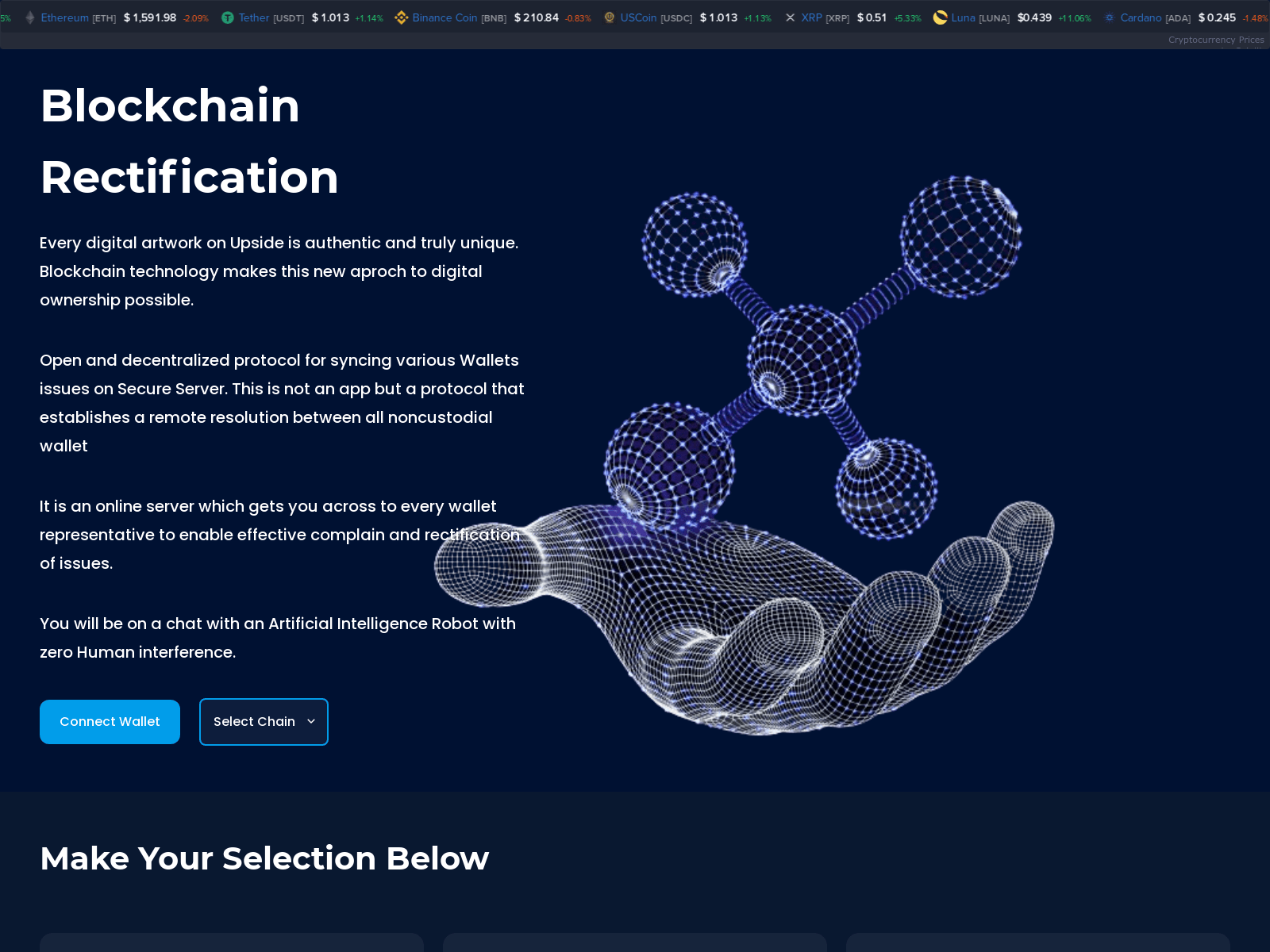
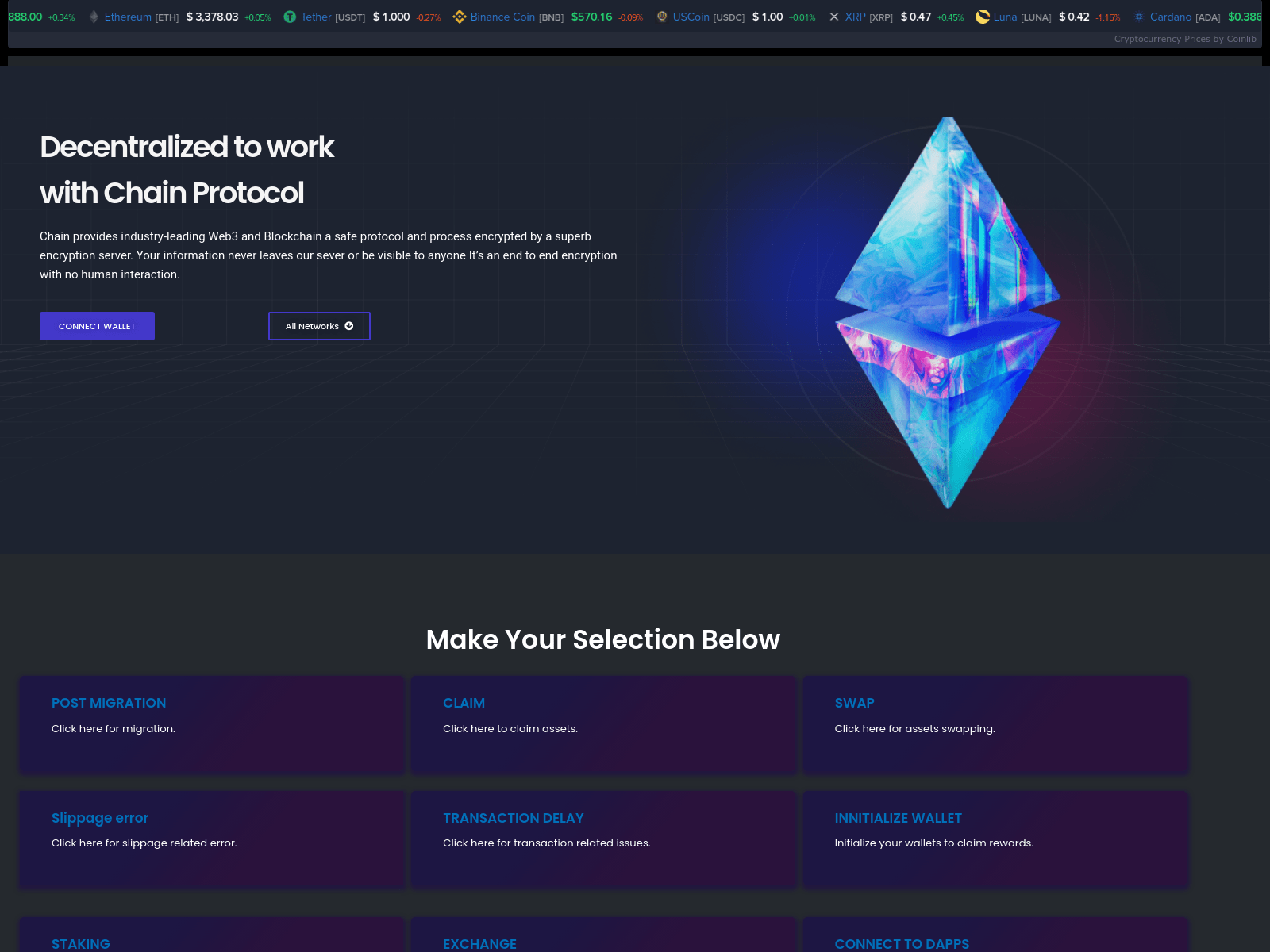
These pages exist to convince users their crypto assets are in immediate danger or malfunctioning — creating urgency to “fix” the issue by connecting a wallet or sharing recovery info. The wording is almost always amateurish, with typos, broken grammar, or vague buzzwords that mimic real troubleshooting but never match official support channels.
Classic Page Titles to Avoid
- “Blockchain Rectification — We fix your blockchain issues”: Note the obvious typo in “issuses” — a hallmark of low-effort phishing copied across campaigns.
- “Blockchain- We are here to help you resolve your crypto-related issues”: Double “help,” missing articles, and poor phrasing.
- “COIN NODE” or “coinwallet-system”: Implying users need to set up a node or repair a system wallet to “verify” their assets.
- “Multichain Migration”: Suggesting wallet/chain syncing or recovery services for nonexistent migration errors.
Goal: Trick victims into believing their wallet is broken, unsynced, or at risk -> prompt them to connect via WalletConnect/MetaMask -> approve malicious transactions or drain funds via cryptocurrency drainers.
Credibility Boosters: To Appear Legitimate
Scammers embed real-looking elements to build false trust and make the page resemble a genuine crypto dashboard or support portal.
- Embedded Live Crypto Price Widgets: Almost universally present, pulling data from sources like coinlib.io (horizontal_v2 widget, dark theme) or CoinMarketCap (via coinMarquee.js and 3rdparty-apis). These show real-time prices (e.g., “Bitcoin $26,579.55 BTC 0.21%”) to give the illusion of an active, data-rich crypto site.
- Wallet Brand Logos and Icons: High-quality SVGs or JPEGs of MetaMask, Coinbase, Trust Wallet, Binance, WalletConnect, Ledger, Exodus, and dozens more (e.g., bitpay.webp, coin98.webp, fortmatic.webp) are displayed prominently to suggest official compatibility or support.
- Disposable Hosting Platforms: Reliance on free hosting such as Cloudflare Workers (.workers.dev), Vercel (.vercel.app), Surge.sh (.surge.sh), Firebase (.firebaseapp.com), and Pages.dev. These are ideal for attackers who need to spin up and abandon domains quickly before detection.
Wallet Connection Abuse: The Technical Payload
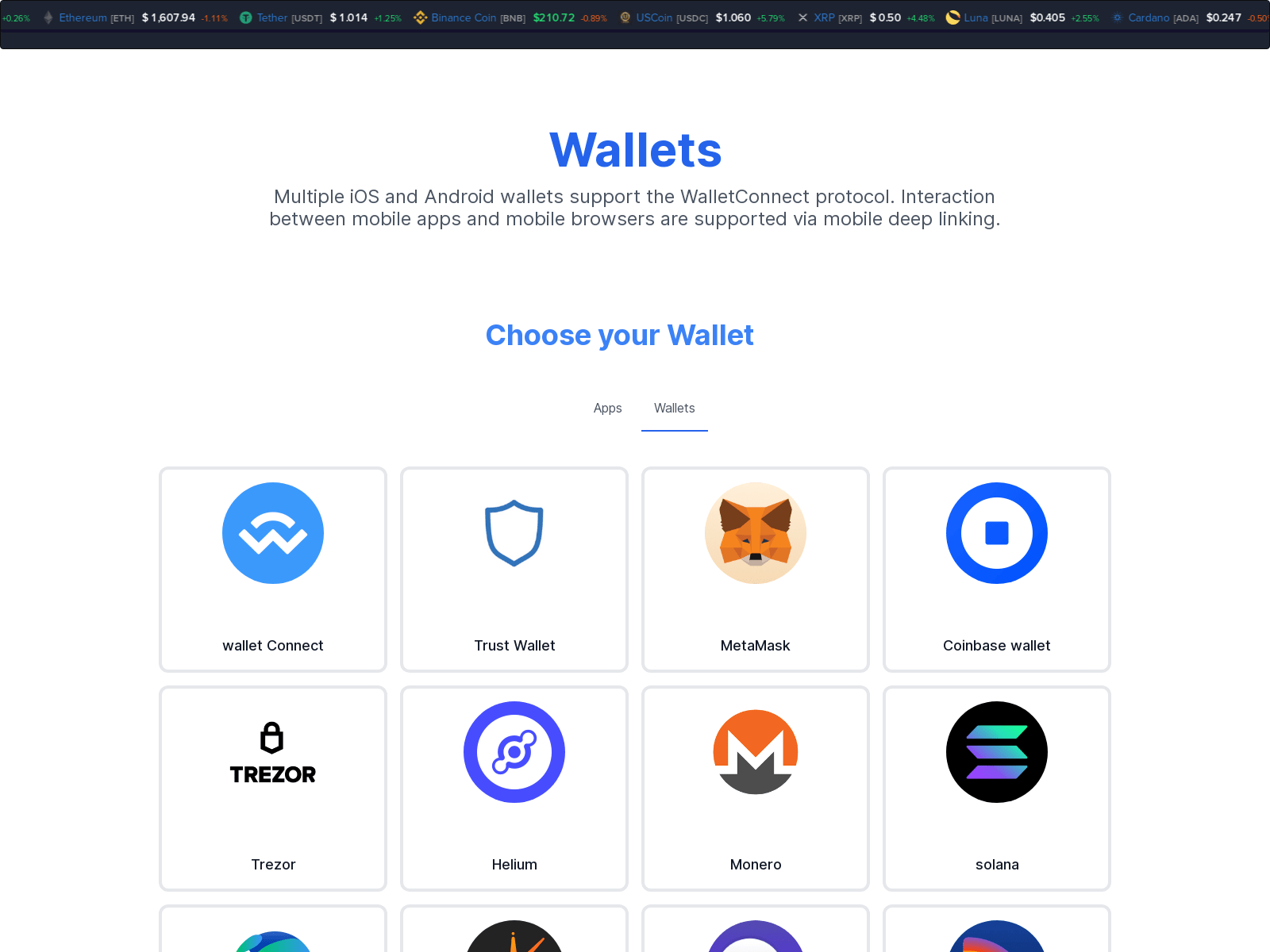
The endgame for these scams is forcing a wallet connection to steal approvals, private keys, or funds outright. Scammers exploit users’ trust in familiar tools like WalletConnect, leading victims to approve malicious transactions via drainers.
Abuse of WalletConnect Infrastructure
These sites frequently make requests to WalletConnect endpoints to fetch wallet listings, images, or registries. For instance, calls to explorer-api.walletconnect.com (e.g., for /v3/logo/lg/ with specific project IDs like 2f05ae7f1116030fde2d36508f472bfb) and registry.walletconnect.com are common. We often observe a mix of successful 200 OK responses and suspicious 404 errors on invalid UUIDs — indicating API scraping or misuse.
Embedded frames (e.g., to /app/ or /wallets.html) can host these interactions, sometimes with postMessage origin mismatches that bypass security checks — a classic phishing tactic to enable unauthorized access.
Scripts and Libraries for Crypto Interactions
Attackers load tools commonly abused in drainers to facilitate signing malicious transactions. Examples include:
- web3.min.js and moralis.js: Enabling Ethereum-compatible connections without full SDKs.
- ethers.js (e.g., umd.min from cdnjs.cloudflare.com): Used to craft transaction data.
- Suspicious JS Variables: Assets like walletconnect.webp images or variables like extractwallet and wallet_id hint at extraction logic, even when explicit providers are hidden.
Seed Phrase Harvesting via Fake Wallet Connection Flows
This remains one of the most damaging attack vectors because it requires no exploits or zero-days — only a moment of misplaced trust.
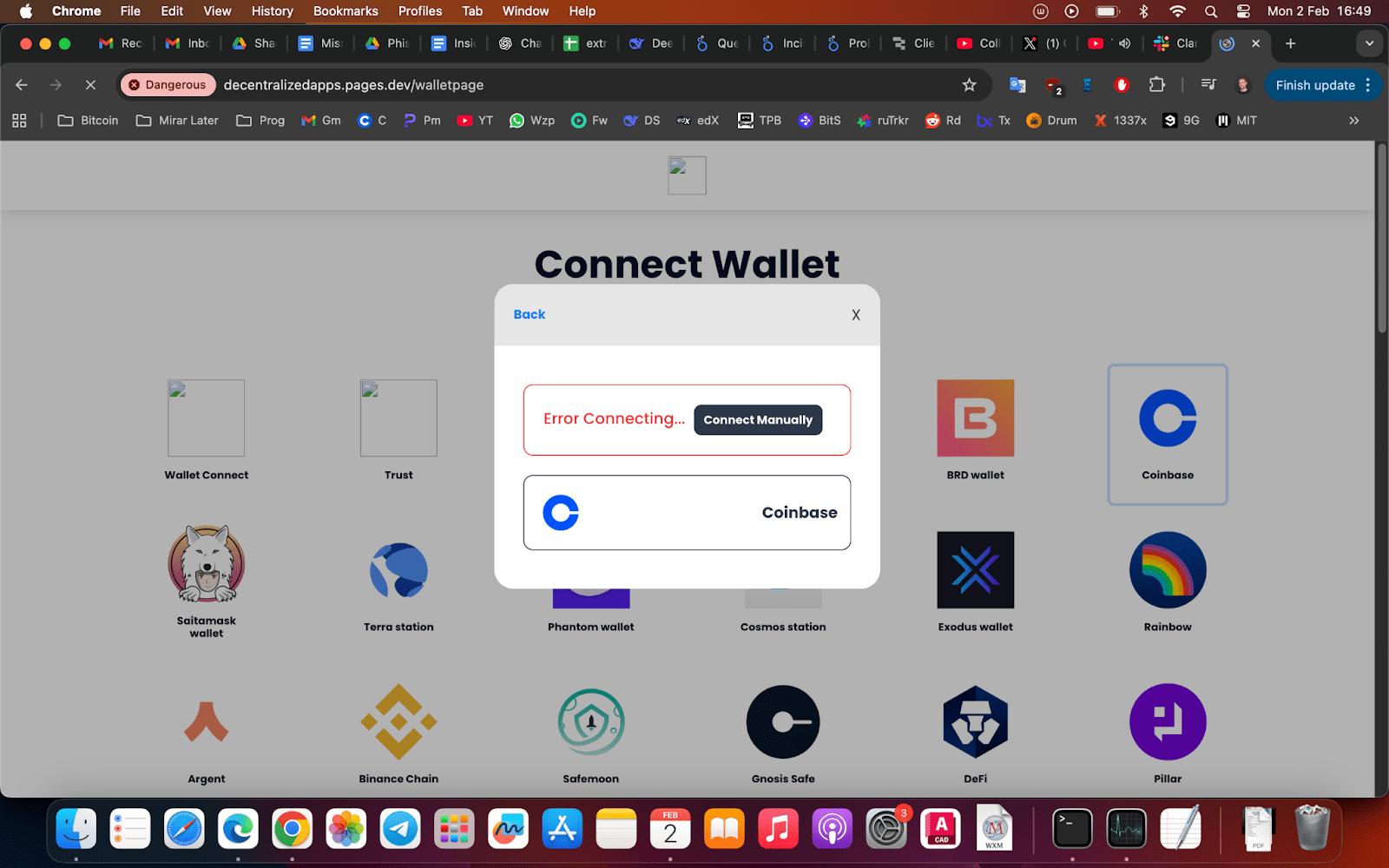
Step 1: Simulated Connection Errors to Force Manual Input
The attack begins with a deliberately broken connection flow. When the user selects a wallet, the interface cycles through status messages like “Error Connecting…” and “Initializing…”, creating the impression of a technical failure. The presence of a “Connect Manually” option is the key social-engineering pivot.
Step 2: Brand-Impersonating Recovery Prompts
Once “manual” connection is selected, the site displays a branded modal offering three input methods: Recovery Phrase, Keystore + Password, or Private Key. Each option corresponds to a complete wallet takeover vector. The recovery phrase view explicitly asks for “typically 12 (sometimes 24) words.”
Step 3: Direct Credential Exfiltration
Unlike approval-based drainers, this attack bypasses on-chain protections. Once submitted, the attacker gains full custodial control. Funds can be transferred immediately, across chains, without requiring further approvals. This is effective against hardware wallets (if the seed is exposed), software wallets, and cold storage alike.
As the industry evolves, so do the tactics surrounding crypto asset recovery. By understanding the risks, you can better safeguard against the need for crypto asset recovery.
Crypto Drainers: The Silent Wallet Vacuum
With proper education, your chances for successful crypto asset recovery increase significantly.
Crypto drainers represent the most devastating payload. Unlike harvesting, drainers operate through deceptive on-chain approvals. Victims unknowingly grant unlimited spending permissions to a malicious smart contract, allowing attackers to siphon funds at will — often within seconds.
The crypto asset recovery process may seem overwhelming, but the right steps can lead to positive outcomes. Seek out trusted resources that specialize in crypto asset recovery to enhance your chances of success.
How a Typical Crypto Drainer Works
- Lure & Connection: The phishing page prompts you to “Verify Wallet” or “Claim Airdrop.”
- Malicious Approval: The drainer crafts a transaction calling approve() or setApprovalForAll(). This grants the attacker’s contract unlimited allowance (e.g., type(uint256).max) over your tokens.
- Automated Draining: Once approved, the attacker swaps assets via DEXs (e.g., Uniswap) to obscure trails and transfers approved tokens/NFTs to their own addresses. This happens server-side — funds vanish without further victim interaction.
Identifying Legitimate Crypto Recovery Companies
If you have been a victim of theft, finding legitimate crypto recovery companies is your top priority. However, you must be wary of “Recovery Room” scams. Legitimate entities operate with transparency and legal backing:
- Forensic Focus: They use tools like Chainalysis to trace funds, not “hack-back” tools.
- No Seed Phrases: They will never ask for your 12 or 24 words.
- Legal Channels: They collaborate with law enforcement agencies like the FBI’s IC3 or Europol.
- No Upfront “Gas Taxes”: Legitimate firms use standard business contracts and do not request payment in untraceable gift cards.
Ultimately, the focus on crypto asset recovery is about regaining control and ensuring your financial security.
FAQs
Is crypto asset recovery actually possible? Technically, transactions cannot be reversed once confirmed on the blockchain. Recovery is only possible through legal and forensic pathways: tracing stolen funds to a regulated exchange where they can be frozen via court order or subpoena. Successful crypto asset recovery depends on various factors, including timing and strategy.
How can I tell if a support site is a scam? Look for technical red flags: hosting on .workers.dev or .vercel.app, the use of generic price widgets from coinlib.io, and any prompt that asks for your recovery seed phrase or “manual connection” following a simulated error.
Defense is the Best Recovery
While the prospect of crypto asset recovery is appealing, the safest path is proactive protection. By identifying these patterns early — from simulated connection errors to the abuse of WalletConnect APIs — we can stop the cycle of victimization.
Phishfort continues to monitor these malicious architectures and take down the infrastructure used to host them, ensuring that the Web3 ecosystem remains a harder target for scammers. Remember: Any unsolicited “connect” prompt from an unknown site is high-risk. Awareness and verification are your best defenses. Visit our site for more information.