Last week, a fake Ledger app managed to bypass Apple’s App Store review process and was made publicly available to users. The malicious application, designed to impersonate Ledger Live, leveraged a subtle homoglyph attack to appear legitimate at first glance. It was ultimately identified and escalated by a PhishFort analyst, who pushed the case directly to Apple’s anti-fraud teams, leading to the app’s removal. But the real concern isn’t just that it was taken down — it’s that it made it through in the first place.
We are conditioned to trust the official app stores. We are told by major tech giants that their walled gardens are safe, curated, and protected by rigorous, manual security reviews. But when it comes to high-stakes applications — particularly cryptocurrency wallets — this blind trust actively costs users hundreds of thousands of dollars.
The harsh reality is that scam apps routinely slip through the cracks of these highly boasted security perimeters. If you are still opening an app store and typing “Ledger” into the search bar, you are playing roulette with your finances.
Here are the facts.
A History of Costly Oversights
The 2023 Incident: The “Official” Scam
Three years ago, a fake Ledger Live application appeared on a major desktop app store. To the trained eye, it was laughably fake — the developer was literally listed as “OFFICIAL DEV.” Yet, this painfully obvious scam bypassed the platform’s security checks and was published to the public.
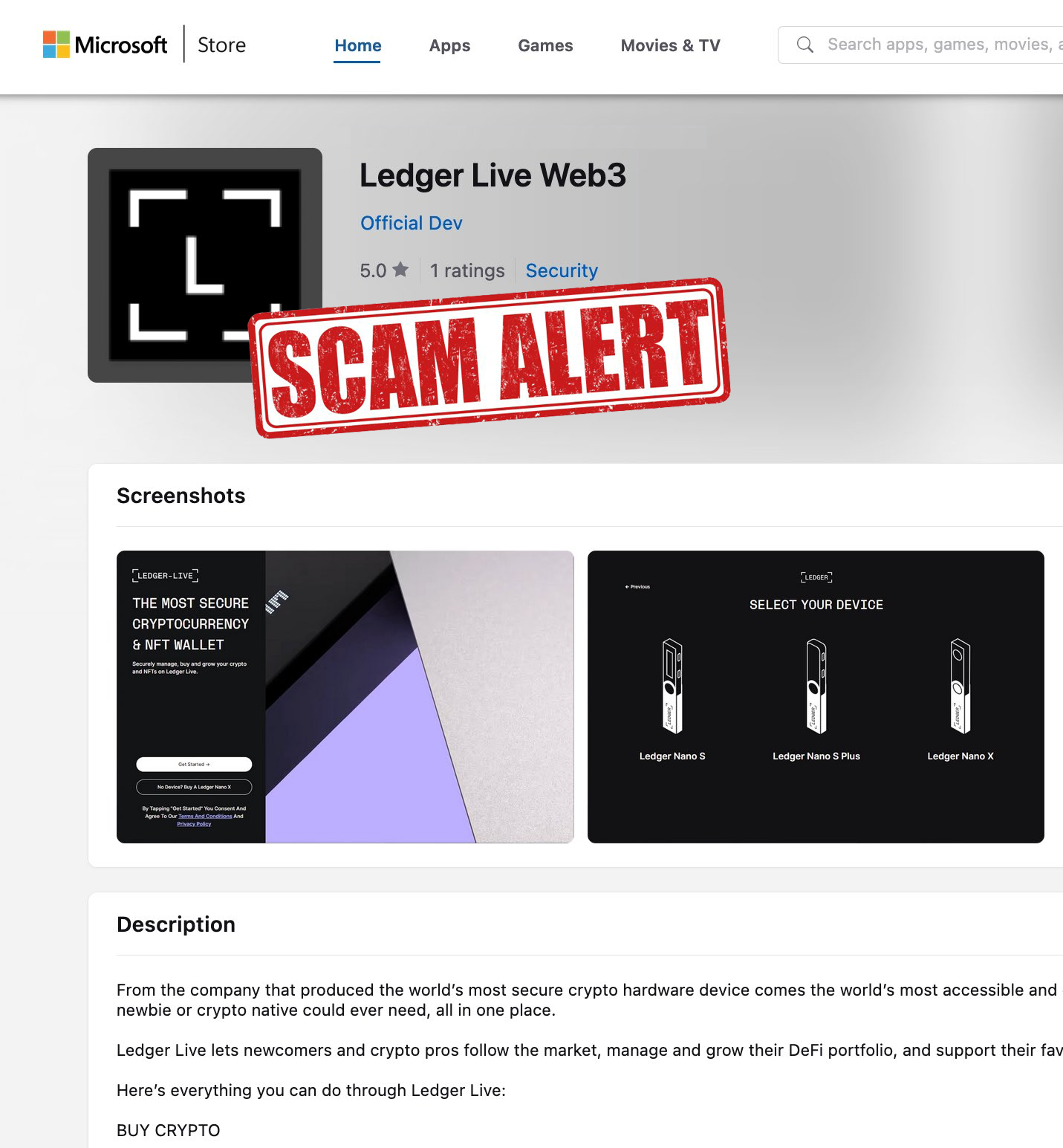
The result? Over 16.8 BTC (valued at roughly $588,000 at the time) was siphoned into the scammer’s wallet (address: bc1qg05gw43elzqxqnll8vs8x47ukkhudwyncxy64q).
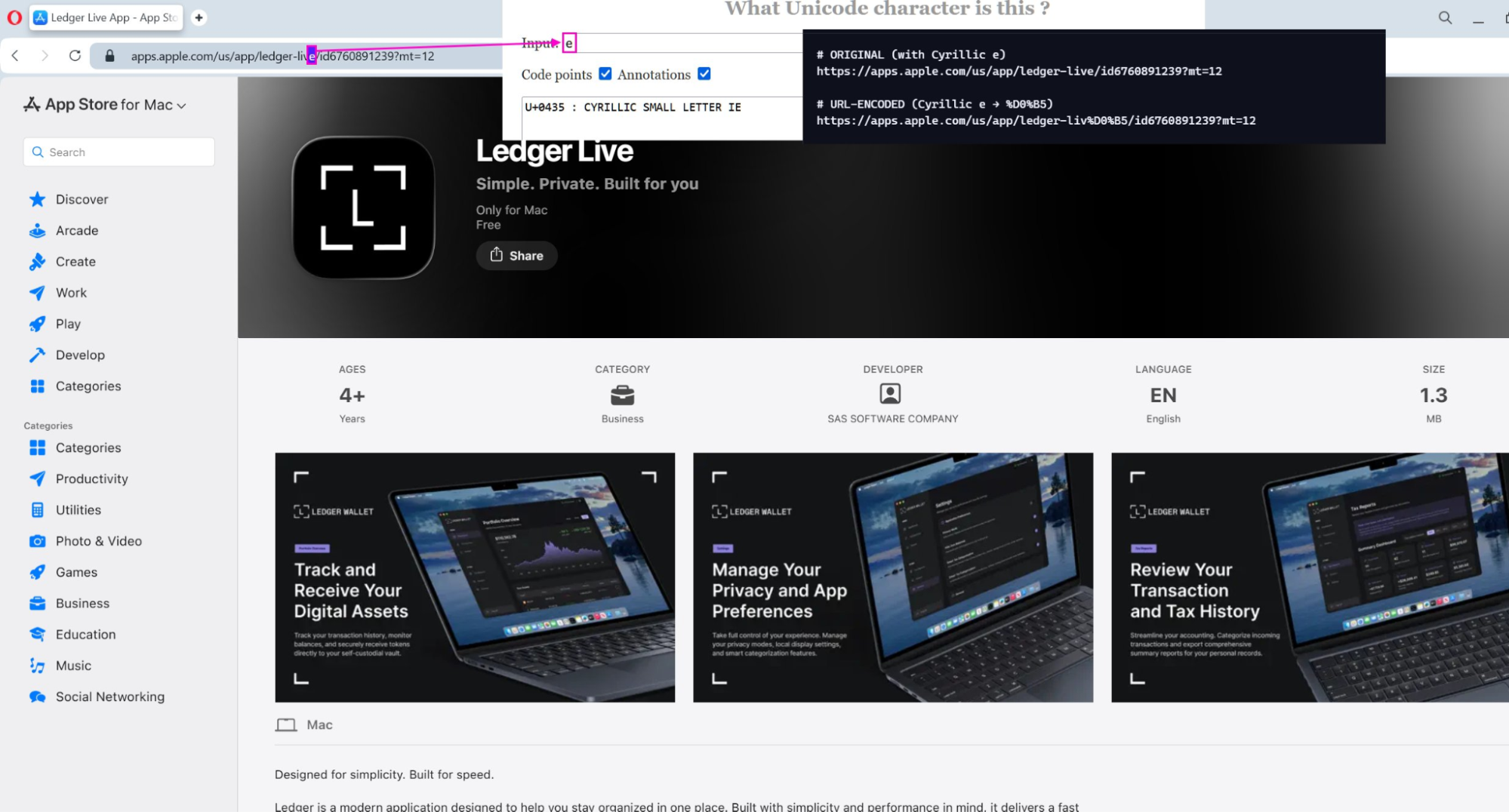
The 2026 Incident: The Cyrillic Trojan Horse Fast forward to April 2026, and the gatekeepers have failed again, this time on a major mobile platform renowned for its strict app review process. A user recently lost 5.9 BTC — their entire retirement fund, representing ten years of savings — in an instant after downloading a malicious Ledger app. What initially appeared to be an isolated incident has since revealed a much broader campaign: losses are now estimated to exceed $9.5 million, impacting over 50 victims across Bitcoin, Ethereum, Solana, Tron, and XRP.
This time, the scammers used a more sophisticated technique known as a homoglyph attack. The app’s URL looked identical to the real one, but it swapped the standard English “e” for a Cyrillic “e”.
- Real:
.../ledger-live/... - Fake:
.../ledger-liv%D0%B5/...(The%D0%B5is the URL encoding for the Cyrillic small letter IE)
To the human eye, the listing looks legitimate. To the computer, it is a completely different destination. But the question remains: How does a manual security review process at a multi-trillion-dollar tech company miss a homoglyph attack designed to steal cryptocurrency?
The Systemic Failure of App Store Gatekeepers
It is entirely unacceptable that platforms boasting secure environments and mandatory app audits routinely serve as the delivery mechanisms for financial ruin. When an app developer named OFFICIAL DEV passes a security clearance, or when a basic character-spoofing attack bypasses a supposedly thorough code review, the system is fundamentally broken.
The tech giants hosting these storefronts rely heavily on automated screening tools that are consistently outpaced by bad actors. Their manual reviews, when they actually occur, often focus more on ensuring the app doesn’t bypass their own payment processors than on protecting the user from sophisticated phishing tactics.
The consequences aren’t just a glitchy app; they are the total, irreversible loss of users’ life savings.
The Golden Rule: Never Search the Store
You cannot rely on app store gatekeepers to protect your wealth. You must take your security into your own hands.
Always get your app links directly from the official vendor’s website.
- Do not open your mobile or desktop app store and search for the app by name.
- Do open your browser, navigate to the verified official website (e.g.
trezor.io, orledger.com), and find their official download pages on the platform you need, be it Apple iOS, MacOS, Microsoft Windows, Google Android or other(s). - Click the direct link provided on the vendor’s site to be redirected to the correct, verified and vetted app store listing.
- Ignore Microsoft store, because the apps there are often obsolete, so if you install Notepad++ as an example from there you get an older and less secure version, than if you would get from the official vendors’ website.
It takes an extra thirty seconds to verify the official website and follow their direct link. That thirty seconds is the only thing standing between your financial security and a devastating, irreversible loss. Be careful out there, because the platforms hosting these apps certainly aren’t.



