Key Takeaways
- Fake investment platforms mimic legitimate financial institutions to steal sensitive data and funds.
- These scams rely on trust signals, realistic offers, and multi-stage fraud to deceive victims.
- Detecting them requires understanding both psychological manipulation and technical infrastructure
What Are Fake Investment Platforms?
Fake investment platforms are fraudulent websites designed to impersonate legitimate financial institutions, such as banks, wealth managers, or investment firms. Their goal is not to provide real financial services, but to collect sensitive user data, credentials, and ultimately money.
These platforms represent a growing segment of phishing activity, where attackers move beyond simple login pages and instead build full corporate-style environments to gain trust at scale.
The New Face of Phishing
Online financial fraud has evolved into highly sophisticated, full-scale impersonation operations. Today, attackers are creating entire fake financial companies designed to convince victims they are interacting with legitimate investment firms.
Instead of impersonating retail brands, these scams present themselves as wealth management firms, treasury advisors, or private investment platforms. The websites are polished, professional, and filled with corporate language meant to establish credibility.
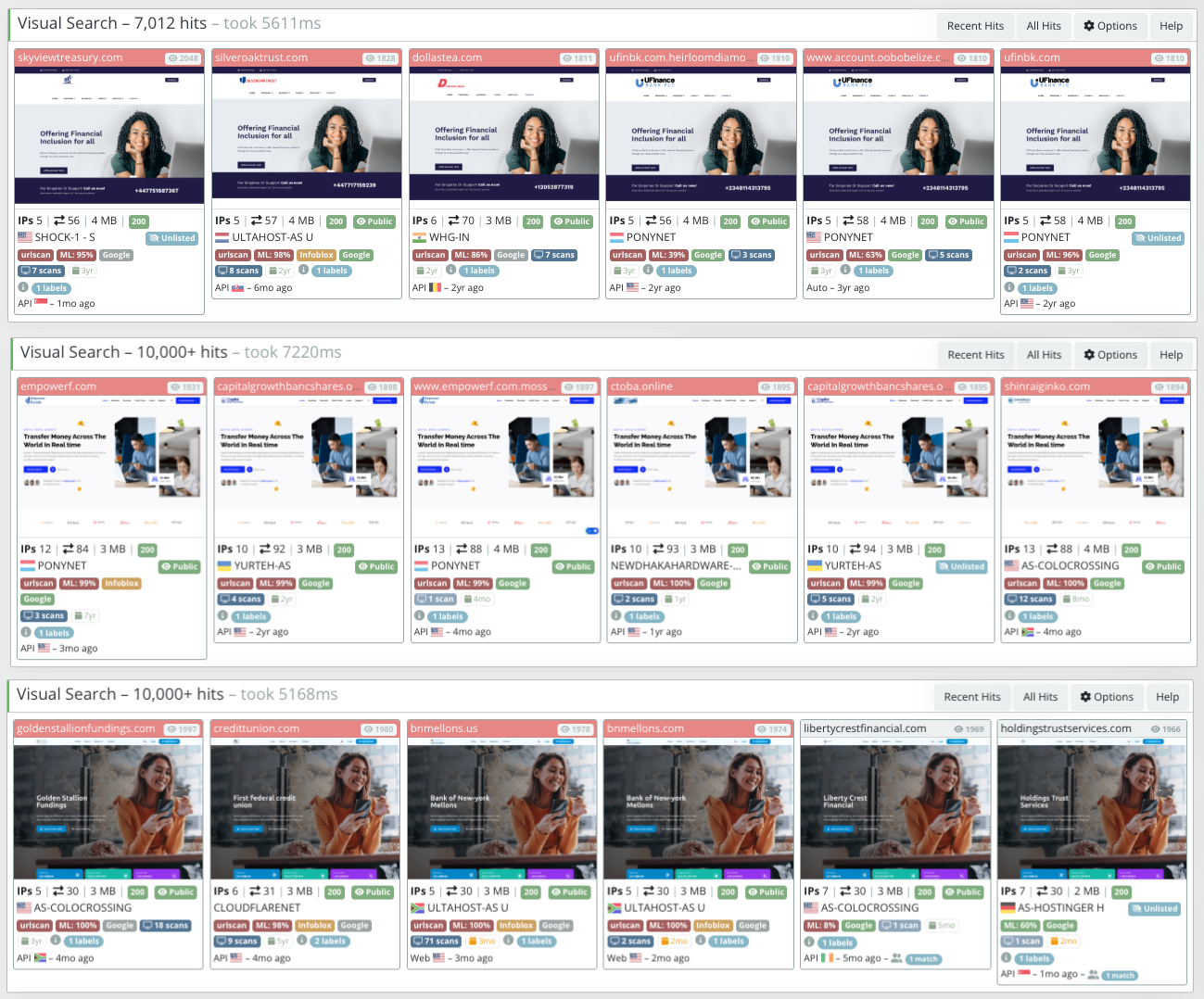
Recent analysis on urlscan.io revealed tens of thousand of suspicious financial-themed websites including:
empowerf.com
primefrontierfin.com
skyviewtreasury.com
At first glance, these sites appear legitimate. They feature corporate-style landing pages, professional branding, and financial terminology typically associated with wealth management firms. But beneath the surface, several indicators suggest these platforms are designed not to provide financial services, but to collect sensitive user information.
Rather than stealing credit card details through fake checkout pages — as seen in scam shop campaigns — these sites aim to harvest investor data and build trust before initiating financial fraud.
Part One: Investor Fraud Narrative – The Illusion of Legitimacy
Imagine you’re searching for a new banking partner. Perhaps you’ve seen an ad on social media, or a friend mentioned competitive rates. You type in the URL — let’s say primefrontierfin.com — and you’re greeted by this:
“Prime Frontier Finance – Your Digital Banking Partner. We do banking differently. We believe that people come first, and that everyone deserves a great experience every step of the way.”

The site features:
- A clean, modern interface with dark mode toggle
- Professional stock photography of smiling professionals
- Clear calls to action: “Open Account Today” and “Login to Banking”
- Detailed rate information: 3.75% APY on savings, 4.00% APR on credit cards
- Customer testimonials with full names and photos
- A complete footer with FDIC insurance claims, privacy policy, and sitemap
- 24/7 phone support with a US number
- A physical address in Washington, DC
This looks legitimate. It feels legitimate. But it’s all an elaborate stage set.
The Psychology of Deception
These sites employ sophisticated psychological triggers:
These sites employ sophisticated psychological triggers:
1. Authority and Trust Signals
Every fake banking site includes what security researchers call trust artillery: elements designed to short-circuit our skepticism. PrimeFrontierFin prominently displays “FDIC Insured” and “256-bit SSL” in its footer. SkyviewTreasury features client logos and a gallery of office photos. EmpowerF claims “18.5M+ active users” and displays technology partner badges.
These signals work because they’re what we’ve been trained to look for. When we see FDIC insurance, we mentally check the “legitimate” box and move on without actually verifying it with the FDIC’s database.
For a deeper breakdown of how attackers create fake login environments, see our blog post about fake login pages .
2. The Goldilocks Effect
Note the rates on PrimeFrontierFin: 3.75% APY on savings. That’s high enough to be attractive in 2026’s rate environment, but not so astronomical as to seem too good to be true. Scammers have learned that unbelievable promises get reported; believable promises get clicked.
3. Social Proof Fabrication
“Sarah Morris” says she’s “impressed with the customer service and speed of payout.” “John Davis” calls it “excellent service.” These testimonials are entirely fabricated, but they appear alongside professional headshots (likely stolen from stock photo sites or LinkedIn) that pass the glance test.
4. The Familiarity Trap
EmpowerF’s tagline — “Dedicated to innovating, simplifying, and humanizing digital banking” — echoes the language of actual fintech disruptors like Chime, Varo, and SoFi. The scammers aren’t copying one bank; they’re blending the visual and linguistic patterns of many legitimate institutions to create something that feels generically trustworthy.
The Bait: What They’re Offering
Each site offers variations on the same core products:
Notice the pattern: concrete offerings, plausible numbers, and just enough specificity to seem real. EmpowerF’s “18.5M+ active users” claim is particularly clever — it’s large enough to imply established success, but generic enough to be nearly impossible to disprove without deep research.
The Hook: Where the Scam Actually Happens
On a legitimate banking site, when you click Open Account or Login, you’re routed to a secure back-end. On these fake sites, those buttons lead to credential-harvesting forms.
What happens next follows a predictable pattern:
Phase 1: Credential Harvesting
Victim enters login credentials. Site displays a fake error or redirects elsewhere.
Phase 2: Account Takeover
Attackers reuse credentials across real banking platforms.
Phase 3: Identity Theft
Victims submit full personal data, enabling long-term fraud.
Phase 4: Money Movement
Funds deposited into fake accounts are irrecoverable.
Infrastructure Patterns Behind Fake Financial Platforms
Infrastructure analysis of suspicious financial websites shows that attackers increasingly follow a structured deployment model similar to other large-scale phishing operations.
Instead of simply launching a phishing page, scammers build full corporate-style websites that serve as entry points for financial fraud and identity harvesting.
A typical deployment pipeline looks like this:
Domain Registration
New Financial-Themed Domain
(e.g., empowerf.com)
↓
Hosting & Website Deployment
Corporate Investment Website Template
Professional Branding / Financial Language
↓
Trust-Building Content
Services Pages
About Us / Advisory Claims
Stock Corporate Imagery
↓
Investor Engagement Points
Contact Forms
Consultation Requests
Email / Phone Collection
↓
Lead Harvesting
Personal Information
Contact Details
Potential Financial Data
↓
Follow-Up Social Engineering
Fake Financial Advisors
Investment Opportunities
Portfolio Management Offers
↓
Financial Fraud
Wire Transfer Requests
Advance Fee Scams
Identity Theft
This model allows attackers to transition from passive phishing into active financial scams.
Once victims submit their information, attackers can initiate direct contact while posing as financial advisors or investment representatives. Because the interaction originates from a seemingly legitimate website, victims may feel confident engaging in further discussions about investment opportunities.
The result is a multi-stage fraud process where the website acts as the first step in establishing credibility before more aggressive financial manipulation occurs.
For a broader view on how these threats are detected and disrupted, see our digital threat protection article .
Why These Scams Are Hard to Detect
Attackers don’t rely on obvious red flags. Instead, they build realistic environments that mimic legitimate financial institutions.
They combine:
- real-looking domains
- believable offers
- delayed fraud execution
- multi-channel engagement
This makes fake investment platforms significantly harder to identify than traditional phishing pages.
For general guidance on identifying financial fraud patterns, refer to SEC investor alerts .
For broader cybersecurity awareness practices, see FTC scam alerts .
Part Two: Infrastructure Investigation – The Anatomy of a Fake Banking Network
If the user-facing side of these scams is about psychology, the backend is about engineering. These three sites — PrimeFrontierFin, SkyviewTreasury, and EmpowerF — reveal a sophisticated, repeatable deployment pipeline that allows scammers to launch dozens of fake banks simultaneously.
The deployment pipeline includes:
- Domain acquisition
- Hosting distribution
- Templated construction
- Mass replication
This industrialized approach enables attackers to scale fraud operations globally while avoiding detection.
Analysis of these three sites reveals a repeatable, automated process:
Step 1: Domain Acquisition
Scammers register domains through low-cost registrars that ask few questions. PrimeFrontierFin used Namecheap; the others’ registrars aren’t visible in scans, but patterns suggest similar budget providers. Domains are typically registered 2-4 weeks before the scam launches.
Step 2: Hosting Procurement
Each site uses a different hosting provider — Namecheap, Shock Hosting, FranTech — all known for inexpensive, no-questions-asked VPS plans. By spreading across providers, scammers avoid easy takedowns: when one host receives abuse complaints and pulls a site, the others remain operational.
Step 3: Templated Construction
All three sites use the same core technologies:
- Bootstrap for responsive design (all sites)
- jQuery for interactivity (Skyview, EmpowerF)
- CDNs (jsDelivr, Google Fonts, jQuery CDN) for assets
- Live chat (Smartsupp on PrimeFrontierFin and EmpowerF)
But look closer: PrimeFrontierFin loads Font Awesome Pro from a specific GitHub repository (aquawolf04/font-awesome-pro). This isn’t a standard CDN link — it’s someone’s personal fork, potentially modified to include tracking or malicious code.
Step 4: Replication
This is where the industrial scale becomes undeniable. The scammers don’t build one site at a time; they deploy hundreds or thousands of identical templates across disposable domains, creating a visual network that URLScan’s systems can detect en masse.
How to Protect Against Fake Investment Platforms
- Verify financial institutions through official registries
- Avoid clicking on investment ads from unknown sources
- Never reuse banking credentials across platforms
- Be skeptical of platforms without a verifiable presence
Final Thoughts
Fake investment platforms represent a shift from simple phishing to full-scale impersonation ecosystems. They don’t just steal credentials. They build trust, then exploit it.
If you want to detect and take down malicious domains, fake financial platforms, and impersonation campaigns before they impact your users, explore PhishFort solutions for digital threat protection .



