“The Rising Cost of Trusting Your Feed” Edition: How do Businesses Protect Paid Ads From Scams
We like to think we’re too smart to be scammed. But in 2026, scammers aren’t just sending clunky emails; they are buying their way onto your screen through Paid Ads and high-budget impersonations.
The biggest danger isn’t just a “dodgy link” — it’s the fact that major ad providers and social platforms often prioritize ad revenue over user safety, allowing sophisticated “drainers” to appear right next to legitimate news.
It is the growing reality that ad providers and social platforms often prioritize automation and advertising scale, allowing sophisticated phishing and impersonation campaigns to appear next to legitimate content.
For businesses, this creates a major challenge. Even legitimate brands can have their identity abused through:
- fake sponsored ads
- cloned websites
- malicious mobile apps
- Impersonation campaigns targeting customers directly, among others.
This is why protecting paid ads from scams has become a crucial part of brand protection and digital threat monitoring.
The Rise of Malvertising and Paid-Ad Phishing Campaigns
Modern phishing campaigns increasingly rely on malvertising.
Attackers purchase ads on major platforms to promote:
- fake token launches
- fraudulent giveaways
- fake refund portals
- malicious gambling platforms
This allows scams to bypass traditional skepticism. Many users assume that if a platform accepts payment for an ad, the advertiser has been verified.
That assumption is wrong.
To help protect both our company network and your personal assets, we’ve put together a few examples that more clearly illustrate what these scenarios can look like. Now, let’s consider three entirely fictional users who accepted things at face value and paid a costly price:
Case 1: John and the “Apple iToken” fake presale (The Deepfake Trap)
![Screenshot of fake website itoken[.]one being promoted via Twitter/X via adverts](/img/1778184568207-unnamed-4-.png)
Screenshot of fake website itoken[.]one being promoted via Twitter/X via adverts
The Scenario: John is scrolling X (Twitter) over his morning coffee. A Promoted Ad pops up: “Apple enters the Crypto space! iToken Presale Live Now.” It features a professional video of the Apple CEO and a sleek website. John thinks, “If it’s a paid ad on a major platform, it must be vetted.” He clicks, connects his wallet to check eligibility, and signs a transaction.
The Reality: Poof. John’s wallet is drained instantly.
The Lesson: Apple does NOT have a token. If you are a user reading this: Ad providers often allow anyone with a credit card to run ads, and they don’t verify if the “Apple” running the ad is actually Apple. Never trust an ad just because it’s “Promoted.”
The critical lesson is not about Apple specifically. It is about trust transference.
Attackers exploit the credibility of major brands while relying on ad platforms that often do not verify whether the advertiser is actually affiliated with the brand being impersonated.
Case 2: Jack and the “Gas Fee Refund” (The Phishing Bait)
![Screenshot of fake website ethgas[.]help promoted in the Twitter/X social media via ads](/img/1778184873466-unnamed-5-.png)
Screenshot of fake website ethgas[.]help promoted in the Twitter/X social media via ads
The Scenario: Jack sees a “Suggested Post” claiming that Ethereum users are eligible for a Gas Fee Refund due to a network error. He’s spent a lot on gas lately, so he clicks the link. The site looks identical to a major block explorer. He connects his wallet and signs an “approval” to “claim” his refund.
The Reality: There is no “refund department.” By signing, Jack didn’t receive money; he gave a malicious smart contract permission to “spend” every asset in his wallet.
The Lesson: “Refunds” and “Airdrops” are the most common phishing lures. If you didn’t go looking for it on an official, bookmarked site, it is a scam.
This attack works because the transaction does not look dangerous to the average user. However, in practice, the approval acts as unrestricted spending permission.
For related phishing tactics, see our article “Fake Domain Exposed: 7 Critical Risks Brands Can’t Ignore”
Case 3: Jasper and the “MrBeast” Casino (The Advance-Fee Fraud)
![Screenshot of fake website mrbeast[.]icu being promoted in social media like Discord.](/img/1778185378201-unnamed-6-.png)
Screenshot of fake website mrbeast[.]icu being promoted in social media like Discord.
The Scenario: Jasper is on Discord and sees a “Verified” bot posting about a MrBeast Crypto Casino giveaway. It promises a $5,400 bonus. He signs up at a professional-looking site (like beastcasino.net). His dashboard immediately shows a $5,400 balance! But to withdraw it, the site says he must first deposit $100 to “verify his wallet.”
Just because a website is named MR Beast (e.g. beastqualify[.]com or mrbeast[.]icu ) does not mean it is real.
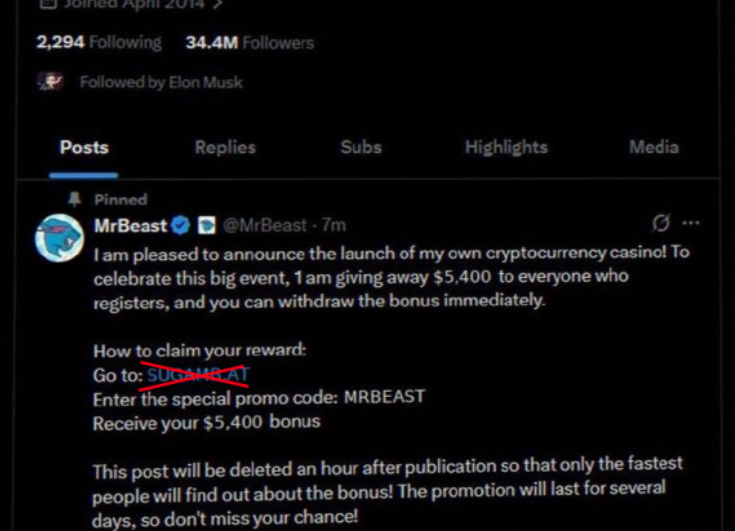
Fabricated tweet which does not exist with link to scam site. Fake followers and metrics
The Reality: This is “Pig Butchering” logic. The $5,400 is just a fake number on a screen. Once Jasper sends his real $100, the scammers vanish.
The Lesson: Celebrities like MrBeast are not giving away thousands of dollars via random crypto sites. If you have to pay money to “unlock” a prize, the prize doesn’t exist.
As we all can see, celebrity impersonation remains highly effective. Attackers create fake promotions involving public figures such as MrBeast and direct users toward gambling or giveaway platforms.
Why These Advertising Scams Continue to Succeed
These campaigns succeed because they exploit platform trust and user psychology simultaneously.
Attackers combine:
- urgency
- social proof
- financial incentives
- brand impersonation
This creates an environment where users stop verifying and start reacting emotionally.
In many cases, the phishing infrastructure itself is technically sophisticated and hosted on reputable services to avoid detection.
How Businesses Actually Reduce Exposure to Paid Ad Scams
Most companies cannot prevent scammers from buying ads that impersonate their brand.
That is the uncomfortable reality.
Attackers move too fast, create disposable infrastructure, and exploit automated advertising ecosystems before platforms react.
What businesses can do is reduce the time between detection and disruption.
That usually means focusing on four concrete areas:
- detecting fake domains as soon as they are registered
- identifying phishing pages before ads begin scaling
- monitoring social platforms and ad ecosystems for impersonation
- accelerating takedown requests before campaigns reach large audiences
This matters because most phishing ad campaigns follow the same pattern:
→ launch cheap test ads
→ identify high-converting creatives
→ scale aggressively
→ rotate infrastructure once detected
By the time users start reporting the scam publicly, the attackers are often already running the next domain.
This is why real-time visibility is critical.
Solutions like digital threat protection https://phishfort.com/digital-threat-protection/ help organizations identify malicious infrastructure tied to impersonation campaigns, including:
- fake domains impersonating brands
- malicious landing pages promoted through ads
- phishing infrastructure targeting wallet users
- fake mobile apps and cloned websites
The goal is not just to remove a single fake ad.
It is to identify the infrastructure behind the campaign before it scales further across advertising networks and social platforms.
BONUS: The 2026 Reality Check for users (Don’t Take the Bait)
- Ads are NOT Endorsements: Scammers use “malvertising” to bypass filters. Just because you see an ad on Google, X, or Facebook doesn’t mean it’s safe.
- The “Sign” is the Kill-Switch: Connecting your wallet is like showing your ID. Signing a transaction is like handing over your house keys. Never sign on a site you reached via an ad or a DM.
- Verify the Domain: Scammers create “clone” networks. A site created yesterday (check the WHO IS data) isn’t a trillion-dollar tech company.
Bottom Line: Ad platforms are currently a “pay-to-play” playground for fraudsters. Stay cynical, verify every link, and remember: if a deal looks like a shortcut to wealth, it’s actually a shortcut to an empty wallet.
Don’t be like the imaginary users from our bad examples, John, Jack, or Jasper.
Stay alert and do not trust everything you see online, especially when it comes to cryptocurrencies, gifts, promotions and rewards.