Key Takeaways
- LiteLLM breach analysis reveals that middleware is the new “crown jewel” for attackers targeting AI infrastructure.
- Identity has become the primary attack surface, with over 60% of breaches involving stolen credentials or session tokens.
- AI-driven attacks are increasing by 300%, requiring automated, continuous monitoring of brand and model assets.
- Successful AI supply chain security requires a shift from static assessments to continuous asset discovery and threat intelligence.
What Does a LiteLLM Breach Analysis Reveal About AI Security?
A LiteLLM breach analysis reveals that as organizations move toward 2026, the cybersecurity threat landscape is expanding far beyond traditional network boundaries. Digital risk protection has become a critical discipline for identifying and mitigating threats that originate outside the corporate perimeter, particularly when dealing with AI middleware.
The LiteLLM incident highlights that external, identity-driven, and AI-enabled threats will dominate the cyber agenda. Security teams must rethink how digital risk is monitored, moving away from simple firewall protections to a model that secures the entire AI orchestration layer.
How Did the LiteLLM Vulnerability Impact AI Supply Chain Security?
The LiteLLM vulnerability impacted AI supply chain security by exposing how automation enables attackers to launch thousands of exploits, such as fraudulent ads and impersonation accounts, within hours. These attacks target customers and partners rather than just internal infrastructure, exploiting trust instead of software bugs.
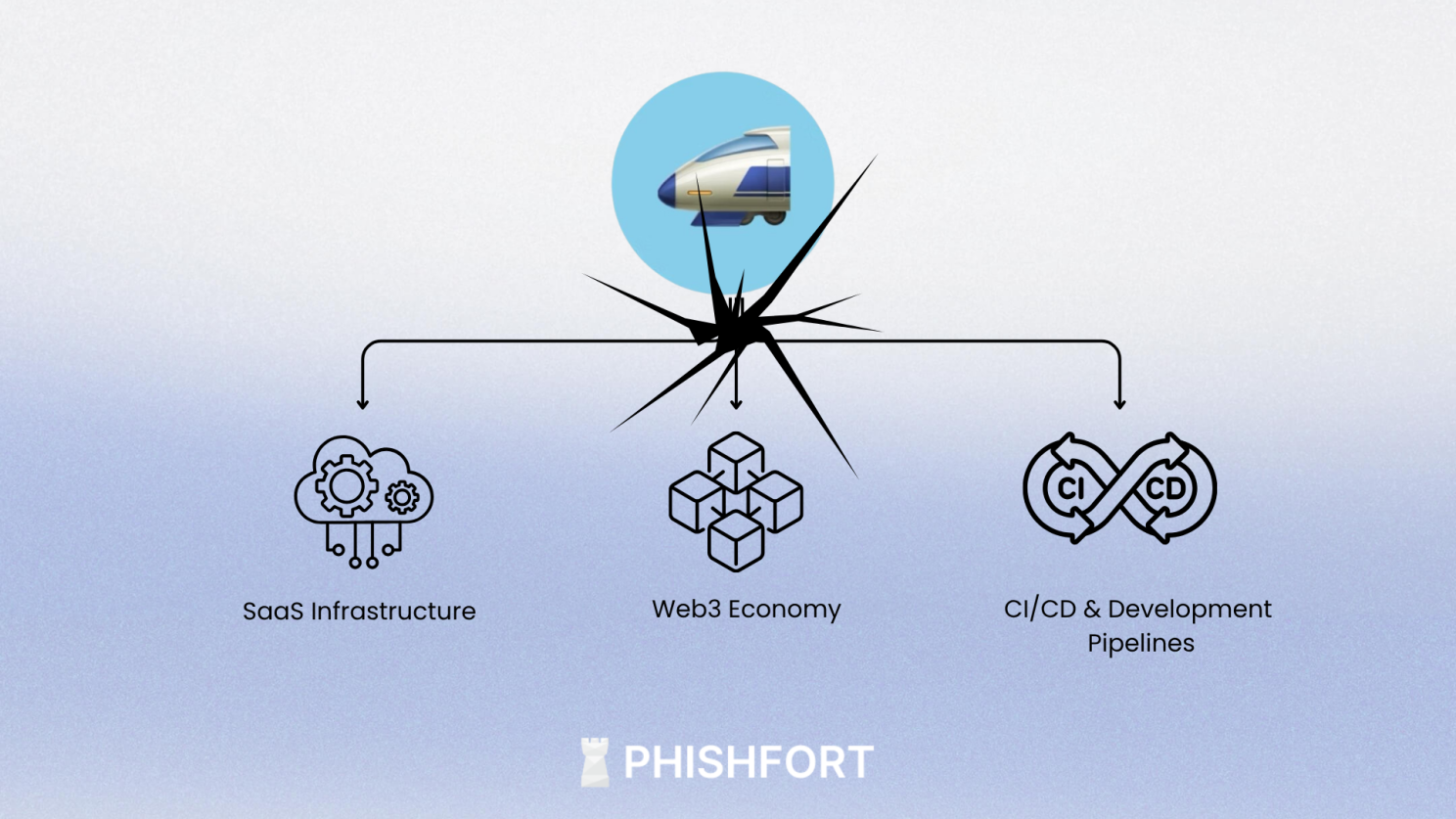
By 2026, the distinction between External Attack Surface Management (EASM) and digital risk protection is narrowing. Organizations now recognize that discovering internet-facing assets—including the API keys and endpoints managed by tools like LiteLLM—is foundational to detecting brand abuse and fraud.
Why is Identity the New Perimeter in LLM Security Risks?
Identity is the new perimeter because stolen credentials and session tokens enable fraud and lateral movement without the need to exploit technical vulnerabilities. In the context of LLM security risks, an attacker who gains access to an orchestration tool like LiteLLM essentially inherits the identity and permissions of the entire organization’s AI stack.
- Credential Exposure: Monitoring leaked credentials is now a core part of digital risk protection.
- Token Misuse: Session tokens are increasingly targeted to bypass traditional perimeter defenses.
- Executive Impersonation: Attackers use AI-generated content to impersonate leadership, often using stolen identities to authorize malicious transactions.
What Are the Most Dangerous AI-Driven Threats in 2026?
The most dangerous AI-driven threats in 2026 involve generative AI being used to automate phishing campaigns and create highly convincing deepfake content. This “arms race” means that digital risk protection must evolve to detect subtle, AI-generated impersonation attempts that look exactly like legitimate communications.
Attackers are increasingly using:
- Automated Phishing Domains: Launching thousands of sites in minutes.
- Fake Mobile Apps: These applications impersonate trusted brands to harvest payment data or distribute malware.
- Deepfake Social Engineering: Impersonating individuals to exploit digital trust.
How Can Organizations Protect Their AI Infrastructure from Supply Chain Attacks?
Organizations can protect their AI infrastructure by transitioning Zero Trust principles into a daily operational standard. This involves continuous verification and least-privilege access for every component in the AI supply chain, ensuring that a single compromise in a tool like LiteLLM cannot lead to a total system failure.
Key actions include:
- Continuous Asset Discovery: Combining threat intelligence with rapid response workflows.
- Cryptographic Hygiene: Reviewing public-facing assets and encryption methods for long-term resilience.
- Supply Chain Visibility: Implementing clear governance around AI usage to reduce data leakage.
Why is Continuous Monitoring Essential for Digital Risk Protection?
Continuous monitoring is essential because threat actors frequently re-upload malicious apps and sites under new names or developer accounts. As digital ecosystems expand globally, these threats appear across regions and languages, making static assessments obsolete.
Digital risk protection platforms, such as PhishFort, extend visibility to mobile and AI ecosystems, detecting threats early in their lifecycle. Automated analysis combined with human verification reduces false positives and accelerates the removal of malicious assets before they cause real harm.
Frequently Asked Questions
What was the main cause of the LiteLLM breach?
The incident was primarily driven by identity-based vulnerabilities where administrative credentials or session tokens were exploited to bypass traditional perimeter defenses.
How do fake mobile apps impact AI security?
Fake mobile apps impersonate brands to steal the credentials used to access enterprise AI systems, acting as a gateway for broader supply chain attacks.
What is the most effective way to stop app store impersonation?
The most effective method is continuous monitoring using a digital risk protection platform that identifies suspicious listings and coordinates rapid takedown requests.
Conclusion & Next Steps
By 2026, AI supply chain security is no longer a niche capability; it is a foundational component of a modern cybersecurity strategy. Organizations that invest early in external visibility and identity resilience will be best positioned to reduce fraud and reputational damage in an increasingly hostile digital ecosystem.
If your organization is conducting a LiteLLM breach analysis or preparing for the evolving threat landscape, now is the time to strengthen your external defenses.
To learn how to reduce external cyber risk and protect your brand, customers, and AI assets, contact our team today.



