If you are researching LNK files malware, you have likely encountered a shortcut on your computer or USB drive that doesn’t lead to your files — and you are right to be concerned. LNK files malware is a deceptive cybersecurity threat that uses standard Windows shortcut files as a carrier for malicious scripts. Instead of opening a document or application, these files execute hidden command-line instructions, often triggering PowerShell or CMD to download secondary payloads, steal credentials, or create backdoors. Because they rely on the user’s trust in a familiar icon, they remain one of the most effective social engineering vectors in 2026.
According to Microsoft’s Security Intelligence , these shortcuts are designed to bypass standard security filters by masquerading as trusted system files, making them difficult for basic antivirus tools to flag without behavioral analysis.
What are LNK files, and how does malware work?
LNK files malware works by weaponizing the legitimate Windows shortcut feature. A standard .lnk file is merely a pointer — a set of instructions that tells Windows: “When the user clicks this, open X application.” Attackers manipulate these instructions by modifying the Target field within the shortcut’s properties. By inputting malicious code, such as powershell.exe -WindowStyle Hidden -EncodedCommand..., they ensure that the moment you click the icon, your computer executes that code in the background without showing any visible window.
Why is LNK files malware so dangerous to the average user?
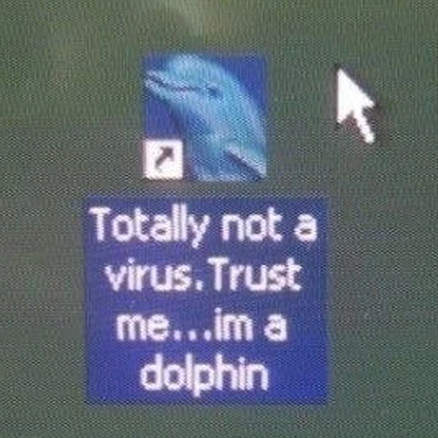
This malware is highly effective because it bypasses the common-sense security checks most users rely on. Users are conditioned to look for suspicious file extensions like .exe or .bat, but they rarely suspect a .lnk file.
- Invisible Execution: The code runs in a hidden window, providing no visual feedback to the user.
- Icon Spoofing: Attackers can change the icon to look like a folder, a PDF, or a system utility, lowering the user’s guard.
- Persistence: Once clicked, the script can install persistence mechanisms, ensuring the malware starts every time you boot your computer.
How does LNK files malware infect your devices?
The most common delivery method for LNK files malware is through physical media, specifically USB drives.
What is the “USB Drive” infection cycle?
- Contamination: An attacker creates a shortcut that points to a malicious script hidden elsewhere on a USB drive.
- Disguise: They hide the original files (your documents or photos) on the drive and create a shortcut that shares the same name and icon.
- The Hook: The victim plugs the drive into a clean computer, sees a folder (which is actually a shortcut), and clicks it.
- Infection: The script runs in the background, infects the computer, and then “opens” the real folder to make the victim believe everything is normal.
How can you spot and identify LNK files malware?
You do not need to be a cybersecurity expert to identify these threats. You only need to know where to look.
How to check for malicious shortcuts?
If you are suspicious of a file, follow these steps to inspect it:
- Right-Click and Select Properties: Do not double-click the file. Right-click it and select “Properties.”
- Examine the “Target” Field: This is the most critical step. A legitimate shortcut will point to an executable file (e.g.,
C:\Program Files\App\app.exe). If the “Target” field contains a long string of garbled text, mentionspowershell.exe,cmd.exe,wscript.exe, ormshta.exe, it is malicious. - Check the “Start In” Path: Malicious LNK files often have an unusual “Start In” directory that points to temporary folders or hidden drives.
- Our Phishing Detection Services proactively scan and neutralize malicious attachments and files before they reach your team, effectively killing the LNK threat at the delivery stage.
What are the best ways to prevent LNK files malware infections?
Preventing LNK files malware requires a multi-layered approach to security that combines technical controls with behavioral changes.
What technical controls can help stop these attacks?
- Disable Autoplay: Prevent USB drives from automatically running programs when inserted into your machine.
- Show File Extensions: By default, Windows hides file extensions. Enable “File name extensions” in File Explorer’s View settings so you can see if a file is actually a .lnk or .pdf.lnk.
- Use Endpoint Detection and Response (EDR): Deploy robust security software that monitors process execution. Most modern EDR tools will flag the behavior of a shortcut trying to launch PowerShell.
- Apply GPO Restrictions: For IT administrators, Group Policy Objects can be used to restrict the execution of specific command-line tools for standard users.
What are the golden rules for users?
| Rule | Why it matters |
|---|---|
| Trust No One | Never open a shortcut sent via email or found on a public USB drive. |
| Use Sidebar Navigation | Always navigate USB drives via the File Explorer sidebar, not by clicking icons in the main window. |
| Verify Source | If you receive a USB drive, confirm with the sender that they intended to send shortcuts before opening. |
| Report Suspicious Items | If you find a rogue shortcut, delete it immediately and scan the drive using reputable antivirus software. |
How to remove LNK files malware if you are already infected?
If you suspect your system has been compromised by LNK files malware, you must act quickly to isolate the threat and prevent further damage.
What is the immediate recovery process?
- Disconnect from the Network: Unplug your Ethernet cable or disable Wi-Fi. This prevents the malware from communicating with the attacker’s server (Command & Control).
- Run a Full System Scan: Use a reputable, updated antivirus or anti-malware scanner to perform a full system scan.
- Remove the Shortcut: If the malware is contained to a USB drive, format the drive (if the data is not critical) or delete all files on it. Note that deleting the shortcut does not remove the malware installed on your PC; the system scan is mandatory.
- Check Startup Items: Check your Task Manager’s Startup tab for any suspicious programs that might have been added by the malware.
Why are LNK files malware a major concern for businesses?
While often dismissed as a home user issue, LNK files malware is a persistent threat to corporate networks. Attackers use these shortcuts to gain a foothold on employee machines. Once inside, they move laterally, accessing servers, stealing credentials, and monitoring internal communications.
For further reading on general safety guidelines regarding removable media, see CISA’s Cybersecurity Guidelines .
How does Digital Risk Protection (DRP) play a role?
Advanced DRP platforms, such as those provided by PhishFort, help organizations identify and mitigate threats that target their digital assets. While LNK files malware is often an endpoint issue, the distribution of these files — often through phishing campaigns or malicious downloads — can be mitigated by monitoring for external brand impersonation and credential-harvesting threats. By detecting the malicious domains or websites that might host these LNK-laden downloads, organizations can stop the threat before it hits the endpoint.
If your organization is preparing for the evolving threat landscape of 2026, now is the time to strengthen your external defenses. Digital Risk Protection is no longer a niche capability; it is a foundational component of modern cybersecurity strategy.
Contact PhishFort today to learn how we can secure your brand and employees from external digital risks.



