In today’s digital environment, logos represent far more than visual design — they embody customer trust. However, logo infringement has become central to phishing and impersonation schemes. Domain disputes and digital brand abuse reached unprecedented levels in 2025, with a substantial portion of phishing attempts involving brand impersonation where logos serve as the primary tool to override user skepticism. For organizations in 2026, logo protection extends beyond legal departments into essential digital risk management.
What is Logo Infringement in the Cyber Context?
Logo infringement occurs when unauthorized parties deploy trademarked visual identities to deceive, confuse, or defraud users. While traditional infringement appeared on physical locations, digital infringement spreads at internet speed. Three high-risk manifestations include:
- Phishing Clones: High-fidelity replicas of login pages engineered to capture credentials, utilizing high-resolution assets to convince victims they’re on legitimate platforms.
- Social Media Impersonation: Fraudulent profiles mimicking brand visual elements to harvest customer data, orchestrate fake giveaways, or disseminate false information.
- Fake Mobile Apps: Malicious applications in third-party app stores leveraging trusted logos to gain installation confidence, resulting in direct user device data theft.
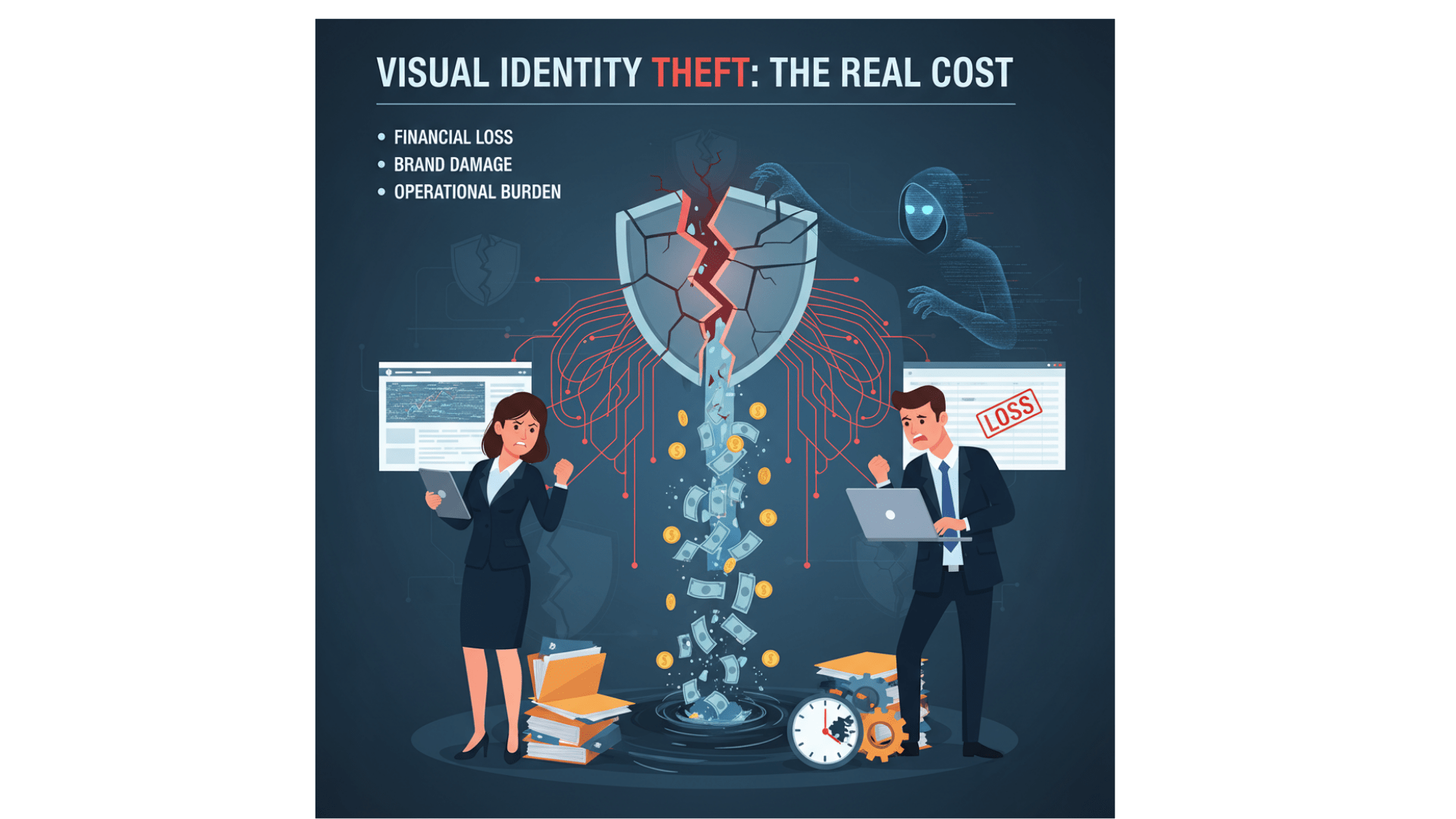
The Real Cost of Visual Identity Theft
When attackers weaponize logos, damage transcends simple confusion. The psychological connection between customers and brands ruptures upon encountering fraudulent materials.
Financial consequences include:
- Direct revenue loss as customers redirect to counterfeit or fraudulent sites
- Reputational deterioration since customers typically blame the legitimate brand rather than perpetrators
- Operational strain from manual takedown efforts that drain resources while providing temporary solutions only
Common Questions About Brand Safety
Reporting logo infringement on social platforms: Platforms including X, LinkedIn, and Meta maintain dedicated intellectual property infringement submission forms. However, enterprise-scale protection demands automation beyond manual reporting. PhishFort streamlines this through automated takedowns , submitting verified evidence directly to platform moderators for rapid removal.
AI and logo infringement detection: Contemporary digital risk protection employs computer vision and convolutional neural networks to identify visual logo matches across the internet. Such technology recognizes brands despite color alterations, resolution changes, or orientation modifications — tactics specifically designed to circumvent text-based filtering.
Logo infringement versus trademark infringement distinction: Logo infringement represents a specific trademark infringement category. While trademarks protect names, slogans, or sounds, logo infringement specifically addresses unauthorized visual graphic mark deployment.
Addressing “Whack-a-Mole” attackers: Threat actors frequently re-upload content immediately post-takedown. PhishFort counters this by monitoring attack-related infrastructure — scanning associated IP addresses and domain registration patterns to block secondary systems before activation.
From Detection to Takedown: A Proactive Framework
Effective logo infringement mitigation requires transitioning from reactive legal action to automated technical enforcement.
1. AI-Powered Visual Monitoring and Computer Vision
Threat actors frequently use typosquatting domains or localized social handles evading standard keyword alerts. Advanced phishing detection engines operate with human-like visual recognition at internet scale. Computer vision technology identifies logos embedded within images, videos, or PDF documents where text-indexed search typically fails.
2. Establishing a Global Blocklist
Once infringing assets are identified, immediate neutralization becomes critical. PhishFort maintains a blocklist protecting over 418 million users globally. Integrating brand-specific threat intelligence into the broader ecosystem prevents infringing content from reaching end-user browsers, neutralizing attacks before victimization occurs.
3. Cross-Platform Enforcement
Logo infringement rarely remains isolated. Attackers might leverage fake Instagram advertisements driving traffic to phishing sites on compromised servers. Comprehensive brand protection requires multifaceted approaches simultaneously targeting advertisements, social profiles, and hosting infrastructure.
4. Streamlined Takedown Orchestration
Takedown success depends on evidence quality and speed as the primary success metric. The platform automates collection of HTML archives, screenshots, and WHOIS data, enabling intellectual property teams to initiate removal procedures within hours. This rapid response minimizes the “window of opportunity” for attackers, making brands less attractive targets.
Final Perspective: Protecting the Eyes of Your Brand
For addressing the vast internet’s blind spots, organizations require comprehensive visibility. Logo infringement frequently initiates larger attack chains encompassing credential theft and financial fraud. Securing visual identity today protects business identity and future viability.
Ready to protect your brand’s visual identity? Contact our team to learn how PhishFort’s digital risk protection platform can secure your logo and brand assets across every digital channel.



