Key Takeaways
- Open source supply chain attacks target developers to compromise entire downstream ecosystems.
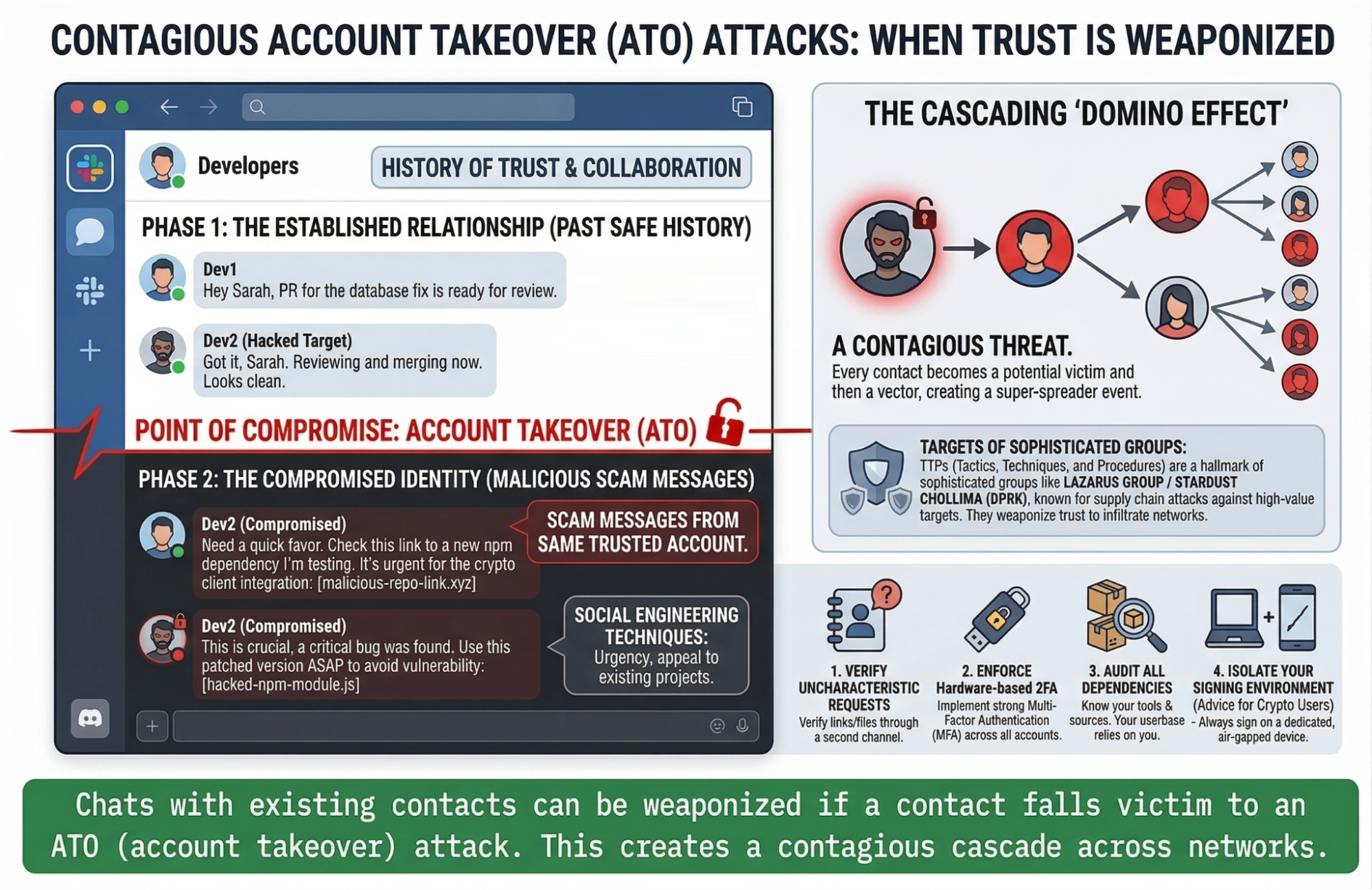
- Trust relationships and CI/CD pipelines are being weaponized to spread malicious code.
- A single compromised maintainer can trigger a cascading “domino effect” across thousands of applications.
What Is an Open Source Supply Chain Attack?
An open source supply chain attack occurs when attackers compromise a trusted dependency, maintainer, or development workflow to inject malicious code into widely used software.
Instead of attacking applications directly, attackers target the components and people that build them.
The Domino Effect: Why Open-Source Maintainers Are Now Prime Targets
The modern software ecosystem is built on a foundation of trust and shared resources. Countless applications rely on the exact same open-source libraries to function. But this interconnectedness has created a lucrative new attack vector for bad actors: the supply chain. Today, hackers are no longer just attacking the front doors of applications; they are going after the developers who maintain the foundational building blocks. Even if a developer has absolutely no involvement with cryptocurrencies or high-finance sectors, they are now a prime target.
The Downstream Ripple: Why Ordinary Libraries Matter
You might maintain a simple data-parsing tool or a popular network request library, but your code might be running under the hood of enterprise software, banking applications, and cryptocurrency platforms.
The crypto sector, in particular, is an incredibly juicy target for bad actors. The risk-to-reward ratio is highly skewed in the attacker’s favor due to the pseudonymous and largely irreversible nature of blockchain transactions. While a few major players can occasionally freeze stolen funds, the process is incredibly cumbersome and rarely works in the end user’s favor.
Because of this, hackers know that compromising a widely used, seemingly innocuous library is the easiest way to infiltrate a high-value crypto application downstream.
The Contagion of Trust & Weaponized Pipelines
These attacks rarely rely on brute-force hacking; they rely on social engineering and exploiting established trust. Modern cyberattacks are highly contagious.
When a bad actor takes over a developer’s account (like their GitHub, NPM, Telegram or Discord), they don’t just stop there. They use that compromised identity to spam the developer’s network of existing, trusted contacts with malicious links or compromised code updates.
Beyond chat applications, attackers also target GitHub CI/CD flows, abusing these automated pipelines to quietly modify and distribute malicious code. For instance, while a project’s initial Pull Requests may have been safely authored by honest_developer@example.com, an account takeover at the GitHub level allows bad actors to slip in compromised updates under addresses like badactor@malicious_example.com within the very same trusted repository.
The Super-Spreader Effect: A high-profile developer with a massive network of contacts is incredibly dangerous when compromised. Every trusted peer, co-maintainer, and friend becomes a potential victim, creating a cascading domino effect of account takeovers.
Actionable Advice for Developers and Maintainers of Popular Open Source Projects
If you are a maintainer of a popular project, you must operate under the assumption that you are a target. Your userbase — crypto developers included — relies on your operational security.
- Question your contacts: Be incredibly wary of sudden, urgent, or out-of-character requests, even if they come from a long-time contributor or a trusted friend. If a known contact sends you an unexpected link or file, verify it through a secondary channel before clicking.
- Lock down your identity: Enforce strict Two-Factor Authentication (2FA) across all your developer accounts, ideally using hardware security keys rather than SMS or standard authenticator apps.
- Audit your dependencies & commits: Keep a close eye on the tools and packages you use, and regularly audit PR authorship and CI/CD configurations for unauthorized changes. The attack might not start with you, but rather with a smaller library you rely on.
Actionable Advice for Cryptocurrency Users
For those operating in the crypto space, protecting your assets requires going beyond the standard advice of simply keeping funds in cold storage. When the very software you are using to interact with your wallets or smart contracts might be compromised, cold storage alone isn’t a silver bullet.
- The Isolated Device Approach: To truly insulate yourself from supply chain vulnerabilities, always sign your transactions on a completely separate device.
- Zero Multitasking: Dedicate this secondary device exclusively to signing transactions and absolutely nothing else. No web browsing, gaming, no casual communication nor downloading any apps.
By keeping your signing environment strictly isolated from your day-to-day digital life, you drastically reduce the risk of a compromised library or a socially engineered phishing link granting attackers access to your funds.
How Users Can Reduce Risk
Supply chain attacks don’t stop at developers.
End users — especially in high-risk environments like crypto — are also exposed.
Using isolated environments for sensitive operations can reduce the impact of compromised software.
For broader guidance on securing software supply chains, refer to CISA supply chain security.
Final Thoughts
The security of the digital ecosystem is no longer just about guarding the vault; it is about protecting the supply lines that build it. Whether you are a developer maintaining a side project that exploded in popularity or a user navigating the high-stakes world of digital assets, vigilance is paramount. Trust in the open-source world is essential, but in today’s threat landscape, that trust must always be verified.
Learn how to detect and disrupt malicious infrastructure and impersonation campaigns with PhishFort.