Key Takeaways
Modern phishing kits have evolved from static templates into sophisticated Phishing-as-a-Service (PaaS) platforms. These tools now utilize dynamic branding, Base64 encoding, and anti-bot layers to bypass traditional security filters.
Relying on signature-based blacklists is no longer sufficient; organizations must shift toward behavioral heuristics and proactive infrastructure monitoring.
PhishFort provides the necessary visibility to detect and neutralize these kits before they reach your user base, turning the tables on threat actors by disrupting their attack lifecycle at the source.
Understanding Polyglot Phishing Kits
The cybersecurity landscape is currently witnessing a paradigm shift. Phishing, once a manual process of creating fraudulent websites, has been revolutionized by the mass production and distribution of phishing kits.
These kits are not merely collections of HTML and CSS files; they are highly engineered, automated platforms that lower the barrier to entry for attackers while simultaneously increasing the complexity of defense for security teams.

In 2026, the term “phishing kits” encompasses a wide range of sophisticated tools that dynamically impersonate brands, bypass multi-factor authentication (MFA), and evade automated crawlers. Among these, polyglot phishing kits represent a sophisticated leap in threat engineering.
Unlike standard kits that are hard-coded to mimic one specific brand, a polyglot kit is brand-agnostic. It is designed to be highly versatile, capable of morphing its appearance in real-time to impersonate dozens — or even hundreds — of different organizations using a single piece of backend infrastructure.
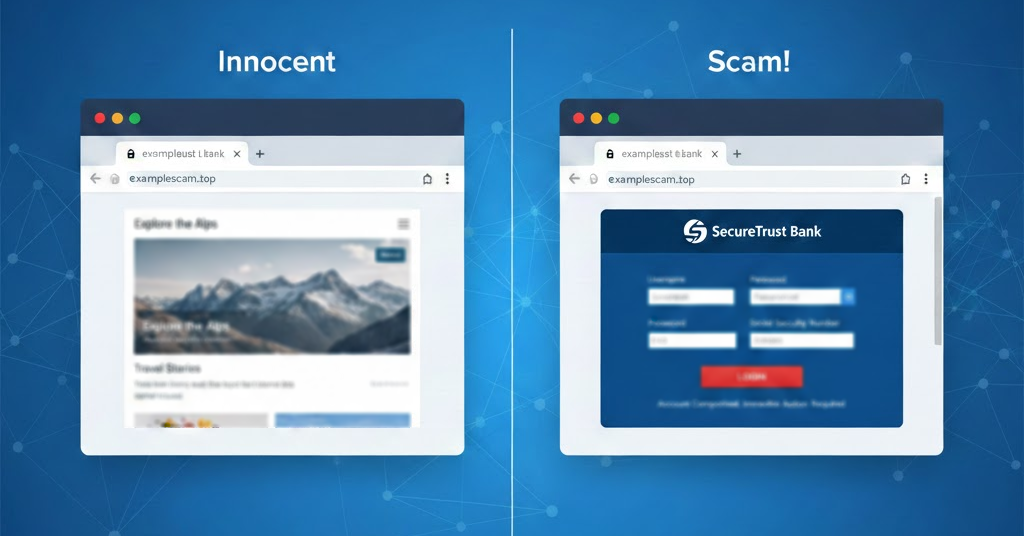
The technical sophistication lies in their ability to detect incoming traffic and adapt instantly. If the visitor is a known security crawler from a major browser or an automated threat detection service, the kit serves a benign page or a 404 error. If the visitor is identified as a legitimate human target, the kit serves the full, malicious credential-harvesting interface.
This one-to-many model allows attackers to use a single deployment to target users of various services simultaneously, significantly expanding the scope of their campaigns.
How the Scam Works
The lifecycle of a modern phishing attack is a study in automation and efficiency. To understand how these kits function, one must look past the visual deception and analyze the backend mechanics.
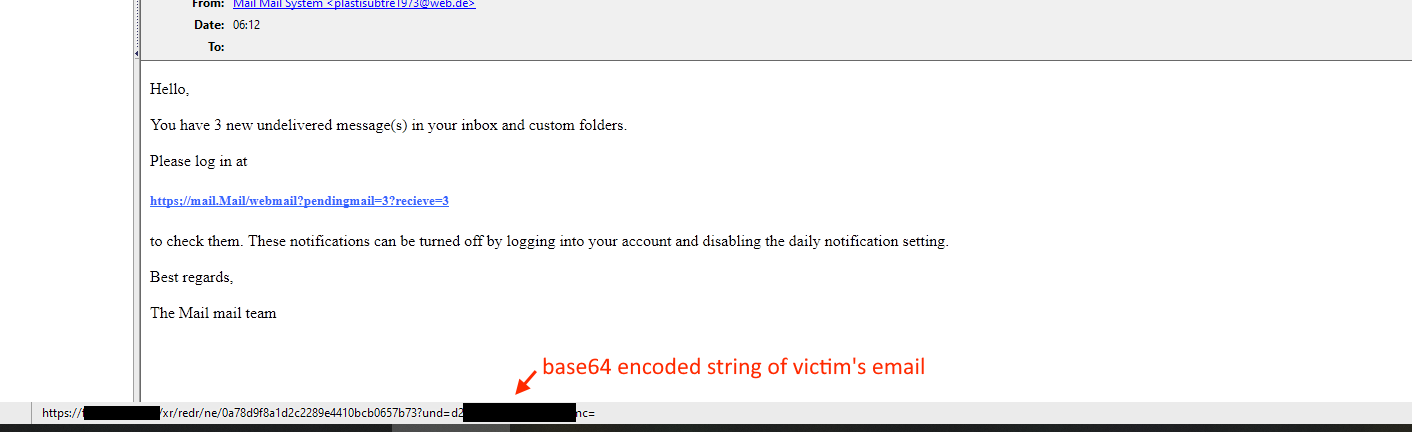
The process typically begins with the distribution of a lure — usually an email, SMS, or direct message — that contains a malicious link. This link is often obfuscated and contains parameters, frequently encoded in Base64 within the URL, which serve as the instructions for the phishing kit.
When the victim clicks the link, the server receives the request, decodes the parameters, and dynamically renders the phishing page. It doesn’t store a library of thousands of static pages; rather, it pulls logos, color schemes, and legitimate CSS assets from the actual brand’s website or a central repository in real-time.
This ensures that the visual fidelity of the fake page is near-perfect, a tactic that dramatically increases user trust. Once the user enters their credentials, the kit does not simply log the username and password to a database.
Many modern kits are Adversary-in-the-Middle (AiTM) enabled. They proxy the connection between the user and the legitimate service. As the user enters their password and the subsequent MFA code, the kit captures these in real-time and passes them to the legitimate service to establish a session.
The kit then steals the active session token, effectively bypassing the MFA protection that organizations rely on as a security safeguard. The attacker is now in possession of an active session, allowing them to bypass subsequent security checks and access the user’s account without needing to repeat the login process.
The kit then logs the data to the attacker’s command-and-control server and typically redirects the victim to the real, legitimate website, leaving the user with the false impression that they simply had a minor login error.
The Mechanisms of Evasion and Deception
1. Email Encoding
The target’s email address is encoded in Base64 and included in the URL. This encoding helps the phishing kit identify the target and determine which brand to mimic. That way the same phishing page can be repurposed to attack users, employees and or partners of different entities on the same scam website. Depending on the email, the kit would then dynamically pull the given brand logo and display it in the fake login page.
2. Dynamic Content Generation
Upon accessing the URL, the phishing kit decodes the email address and identifies the associated brand. It then pulls the relevant logos, color schemes, and other branding elements to create a convincing phishing page.
3. Brand-Specific Phishing Pages
The phishing page is tailored to the identified brand, making it appear legitimate to the target. This increases the likelihood of the target falling for the phishing attempt.
4. Geofencing and Anti Bot Protection
The scam page redirects users to a harmless news website like BBC or CNN, if it detects a crawler, VPN, proxy, or security vendor.
5. User Fingerprinting
Phishing scams use a variety of techniques, such as HTML Canvas fingerprinting , to try and detect emulation, as phishing scams very often target victims with mobile devices only. This technique is peculiar and effective because the rendering of the canvas can vary based on the user’s operating system, browser, device, graphics chip or card, and even installed fonts, making it possible to identify users even without leveraging cookies.
6. Malware
There are also polyglot malware files, which are not necessarily phishing, but usually a Trojan or RAT in disguise, e.g., an archive that is simultaneously a PE32+ DLL and a ZIP container. Since email filters inspect only the ZIP header, the dangerous DLL portion has a chance of going unchecked until the moment of user interaction. Those attacks are often multi-staged.
Evasion Techniques
The primary reason phishing kits have become so difficult to manage is their aggressive implementation of evasion techniques. Threat actors are keenly aware of how security researchers operate; they know that cybersecurity companies use automated crawlers and sandboxes to discover and blacklist malicious domains.
To counter this, developers of phishing kits have integrated “anti-bot” layers directly into the code. These layers inspect every incoming request to determine if it is a human visitor or an automated security tool.
They analyze headers, user-agent strings, IP addresses, and even mouse movements. If the system detects a non-human visitor, it acts as a chameleon, immediately serving clean content — such as a Google search page or a dummy website — to avoid triggering an alert. This creates a cat-and-mouse game where researchers often see a clean site, while the target sees a malicious one.
Furthermore, these kits frequently leverage fast-flux DNS and Domain Generation Algorithms (DGA). Instead of relying on a single domain, which can be easily taken down, the infrastructure constantly rotates through thousands of newly registered domains.
By the time a security filter has identified one malicious URL, the kit has already moved its entire operation to a new domain, rendering the previous blacklist update obsolete. This speed — often referred to as the time-to-live advantage — is the core reason why static, blacklist-based protection strategies are failing in the 2026 threat environment.
Advanced Evasion Tactics of Polyglot Phishing Kits
Polyglot phishing kits employ several evasion techniques to avoid detection:
Cloaking: The ability to display a completely different page unless the victim meets criteria, e.g. came from a decoy website attacker has prepared via referrer or cookie. Often a phishing scam will pretend to be innocent, while hiding the payload in plain sight.
Dynamic Content: By generating content dynamically based on the target’s email address, these kits can evade static detection methods that rely on known phishing page signatures.
URL Obfuscation: Encoding the email address in Base64 or ROT13 within the URL helps obscure the true nature of the phishing attempt, making it harder for automated systems to detect.
Brand Mimicry: The ability to mimic multiple brands increases the effectiveness of the phishing kit, as it can target a wide range of victims with tailored phishing pages.
Implications for Cybersecurity
The rise of polyglot phishing kits has profound implications for corporate cybersecurity. The most immediate impact is the erosion of trust. When a brand is impersonated at scale, the psychological impact on the customer base is devastating.
Users become wary of all communications, leading to lower engagement and long-term brand equity damage. Beyond the reputational risk, the technical implications are severe. Because these kits are sold as Phishing-as-a-Service (PaaS), threat actors with minimal technical skill can now execute highly complex, enterprise-grade attacks.
This democratization of cybercrime means that every organization, regardless of size or industry, is now a potential target. For security teams, the implication is that traditional defenses are being overwhelmed.
Relying on signature-based detection is akin to using a padlock to stop a tank; it provides a false sense of security while the attacker is operating inside the perimeter. Furthermore, the ability of these kits to bypass MFA means that credential theft is no longer a localized event; it is a gateway to account takeover, data exfiltration, and lateral movement within corporate networks.
The cost of a breach, when factoring in incident response, legal fees, customer support, and brand remediation, has skyrocketed. In this environment, the proactive detection of phishing infrastructure is not an optional security layer — it is an operational necessity.
Defensive Measures
Neutralizing the threat posed by modern phishing kits requires a decisive departure from reactive, blacklist-heavy strategies. Security teams must pivot toward a methodology centered on visibility and proactive disruption.
The most effective defensive posture relies on three pillars:
- Advanced Threat Detection: Organizations must utilize heuristic and visual analysis to identify the structural markers of a phishing kit, rather than the specific URL. By analyzing how a page is constructed — identifying the presence of credential-harvesting forms, analyzing CSS structures, and detecting the absence of legitimate business context — security teams can identify phishing activity even on domains that have no prior reputation.
- External Attack Surface Management (EASM): You cannot stop what you cannot see. Proactive defense involves continuous scanning of the internet to detect the deployment of infrastructure that impersonates your brand. This requires a comprehensive phishing detection strategy that monitors for suspicious domain registrations and real-time scanning of web content.
- Rapid, Proactive Takedowns: As global leaders in takedown services , PhishFort emphasizes that the most effective way to break the cycle is to disrupt the attacker’s ROI. If a kit is taken down within minutes of its deployment, the cost-benefit analysis for the attacker shifts, forcing them to either abandon the campaign or invest more resources into evasive techniques, which increases their own detection footprint. If an attacker cannot maintain their infrastructure, their campaign fails.
By integrating these measures, organizations can force attackers to face a consistent, high-friction defense, making your brand a much more difficult and costly target.
Cybersecurity Analyst Insights: Q&A
Q1: What are the primary indicators that a site is utilizing a high-end phishing kit rather than a manual fraud page?
A: Modern kits leave a distinct “fingerprint” that differs from manually coded pages. Look for highly structured folder hierarchies, the presence of obfuscated JavaScript libraries designed for bot-detection, and highly unusual URL parameters (often long Base64 strings). Additionally, these sites often exhibit “latency in rendering” because they are fetching assets from the legitimate brand’s site in real-time, creating a slight lag in page load that manual, static pages do not have.
Q2: Can we effectively block these kits at the network perimeter, or is endpoint visibility required?
A: Blocking at the network perimeter is a necessary first step, but it is insufficient on its own. While you can block known malicious domains, the polyglot nature of modern kits means the threat is often moving too fast for traditional firewalls to keep up. The most effective defense is a hybrid approach: blocking infrastructure at the perimeter using threat intelligence, while employing browser-based or agent-based protections that evaluate the page content in real-time as the user interacts with it, regardless of the URL reputation.
Conclusion
Phishing kits are not going to disappear; they are becoming more automated, more evasive, and more accessible to a wider range of threat actors. The Phishing-as-a-Service economy ensures that innovation in this space will continue at a rapid pace.
For organizations, the only path forward is to stop treating phishing as a minor IT inconvenience and start treating it as a dynamic, high-stakes threat to brand integrity and customer trust.
By focusing on deep visibility, real-time threat intelligence, and a commitment to rapid, proactive takedowns, you can neutralize the threat before it impacts your ecosystem.
At PhishFort, we are dedicated to staying ahead of these kits, providing the intelligence and action needed to keep your brand secure. To learn more about how we can help you monitor and eliminate threats targeting your digital assets, explore our Phishing Detection capabilities and our Takedown services .



