Key Takeaways
- Surgical Precision: 2026 supply chain attack news highlights a shift from mass infection to “surgical” targeting, where attackers like Violet Typhoon (APT31) deliver malware only to specific high-value IPs.
- Infrastructure Hijacking: Recent breaches of Notepad++ and EmEditor were not caused by code vulnerabilities but by the compromise of official hosting and distribution infrastructure.
- Extended Dwell Time: Attackers maintained access to trusted update channels for over six months (June–December 2025), bypassing traditional EDR and sandbox environments.
- Identity-Driven Vectors: New reports from February 2026 (e.g., the AgreeToSteal Outlook add-in campaign) show attackers reclaiming abandoned legitimate domains to steal over 4,000 corporate credentials.
- Proactive Defense: Organizations must move beyond static audits to Continuous Dependency Intelligence and external digital risk protection (DRP).
The 2026 Intelligence Update
The latest supply chain attack news for 2026 has sent shockwaves through the DevOps and AppSec communities. We are no longer dealing with broad, noisy “spray-and-pray” campaigns. Instead, the industry is witnessing the rise of the Surgical Strike — an era where your most trusted developer tools are turned against you with frighteningly high precision. These supply chain attack news events are crucial to understand for future prevention.
In just the first two weeks of February 2026, major disclosures have redefined what we consider “safe.” The headline event remains the dual-compromise of Notepad++ and EmEditor, where the “official source” itself became the delivery agent for state-sponsored malware. Simultaneously, researchers have identified a new “AgreeToSteal” campaign (Feb 11, 2026), marking the first major supply chain attack involving a malicious Microsoft Outlook add-in that successfully exfiltrated thousands of credentials via abandoned legitimate domains.
Moreover, these incidents of supply chain attack news highlight the urgency for organizations to reevaluate their security strategies.
This supply chain attack news serves as a stark warning: the traditional perimeter is dead. When an attacker can sit inside your official update server for six months without triggering an alarm, your security strategy must evolve from perimeter defense to continuous external verification.
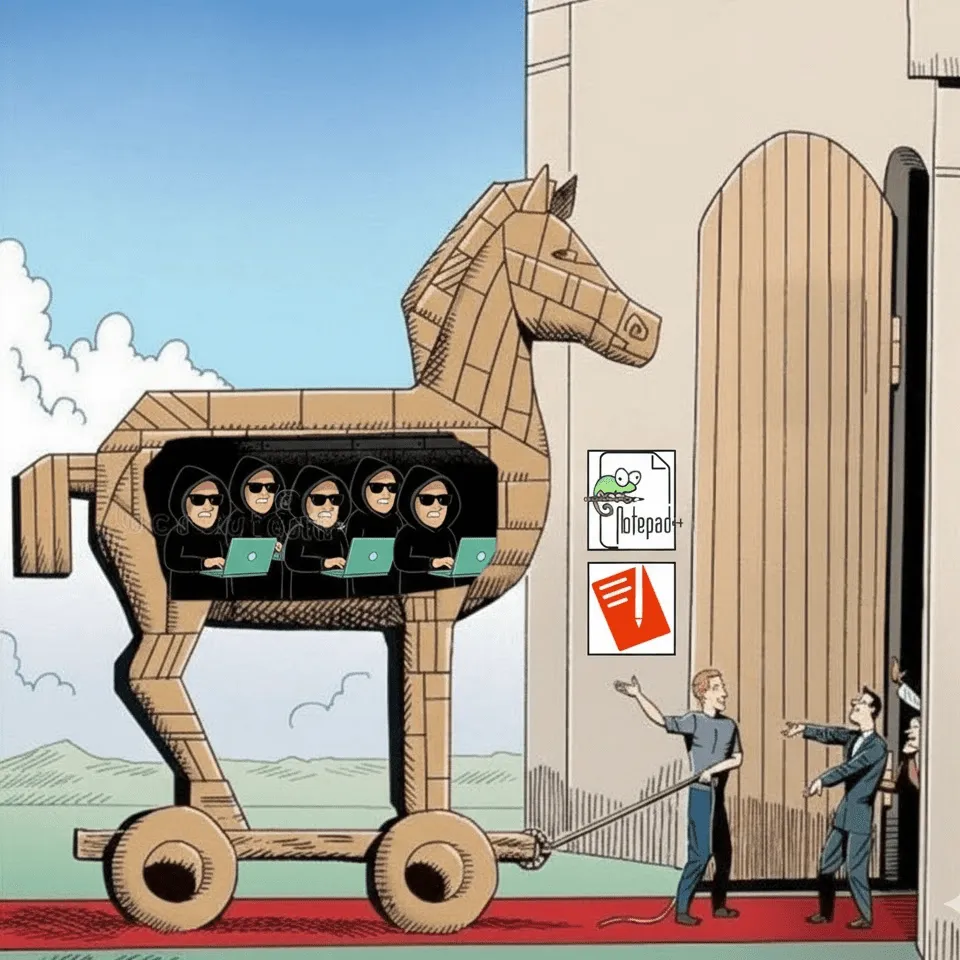
When Trust is the Trojan Horse: Navigating the New Era of Supply Chain Attacks
For years, the golden rule of cybersecurity for end-users has been simple: “Only download software from the official source.” We’ve been told that if we avoid shady third-party sites and stick to official domains, we’re safe.
But what happens when the official source itself is compromised?
Recently, the cybersecurity world was rocked by a series of sophisticated supply chain attacks targeting tools that developers and IT professionals use every single day: Notepad++ and EmEditor. These weren’t “fake” websites; these were the real-deal official platforms delivering malicious payloads.
The Breach of the “Official” Source
In two distinct but equally chilling campaigns, an APT (Advanced Persistent Threat) group proved that even the most cautious users can be compromised through no fault of their own.
1. The Notepad++ Long Game
Between June and December 2025, a highly sophisticated actor managed to infiltrate the hosting provider used by Notepad++. They didn’t just deface a page; they maintained access for months.
The terrifying part? They weren’t giving the malware to everyone. By utilizing a “surgical” approach, the attackers delivered malicious payloads only to specific targets, likely based on IP addresses or geographic locations. This made the breach incredibly hard to detect. Users went to the correct URL, saw the correct branding, and downloaded what they thought was a routine update — only to have a trojanized version of the software installed on their systems.
As detailed in the Notepad++ official incident report, the attackers focused on the getDownloadUrl.php script, which the WinGUp updater relies on. By controlling this endpoint, they could selectively redirect specific update requests to attacker-controlled servers.
2. The EmEditor “Watering Hole”
Almost simultaneously, Emurasoft’s EmEditor was targeted. In this instance, the attackers modified the URL behind the “Download Now” button on the official homepage.
Users who clicked the link were redirected to a malicious .msi file. While the file had the same name and size as the original, it was signed with a certificate from a completely different firm. This allowed an infostealer — disguised as a Google Drive Caching extension — to harvest VPN configurations, browser credentials, and keystrokes from unsuspecting developers. This was confirmed in a security notice by Emurasoft.
Why “Surgical” is the New “Scary”
These incidents represent a pivot in the supply chain attack landscape. Historically, supply chain attacks like SolarWinds aimed for maximum volume. Today, the goal is stealth and high-value persistence.
By targeting tools used by system administrators and developers, attackers gain a “keys to the kingdom” level of access. If you compromise a developer’s machine, you potentially compromise every line of code they write, every server they access, and every secret they manage.
The 2026 Threat Landscape: By the Numbers
According to recent industry data from Group-IB and Intel 471, supply chain vulnerabilities now account for over 40% of all initial access vectors used by ransomware groups.
- Financial Impact: Global losses attributed to supply chain compromises are projected to hit $53.2 billion by the end of 2026.
- Dwell Time: In the Notepad++ case, the attackers remained undetected for over 180 days.
- Targeting: 64% of organizations now list geopolitically motivated supply chain attacks as their top strategic concern.
In light of recent supply chain attack news, it is crucial to reevaluate our current security measures.
Proactive Defense: Beyond Compliance to Continuous Verification
Relying on a “yearly audit” of your vendors is no longer sufficient. In 2026, security teams must treat software updates as a high-risk event.
1. Implement Zero Trust for Software
Never assume a binary is safe just because it came from a *.org or *.com you recognize. Every download should be subjected to automated hash verification. If the hash doesn’t match the one published (and verified) by the vendor, execution must be blocked.
2. Operationalize SBOMs
A Software Bill of Materials (SBOM) should not be a static PDF stored in a drawer. It must be a living artifact integrated into your CI/CD pipeline. Use it to track every dependency in your environment, allowing you to identify within seconds if a new “poisoned package” news alert affects your stack.
3. Monitor the External Footprint
Understanding the implications of supply chain attack news helps organizations prepare for the worst.
Attackers often use “brandjacking” — setting up domains like emeditor-update[.]com — to serve malware. While the Notepad++ attack was an infrastructure compromise, many supply chain attacks start with simple typosquatting. Continuous monitoring of your brand’s digital presence is essential to catch these look-alike domains before your customers do.
How Phishfort Protects the Ecosystem
At Phishfort, we’ve seen how these attacks don’t just hurt the end-user — they devastate a brand’s reputation. When your official download link is used to spread malware, the trust you’ve spent decades building can vanish in a weekend.
This is where Brand Protection becomes a vital necessity rather than a luxury.
- For Brands: Phishfort provides proactive monitoring that goes beyond simple phishing. We help brands identify when their infrastructure is being impersonated or manipulated, ensuring that your customers stay safe and your reputation remains intact.
- For Partners and End Users: Our ecosystem-wide intelligence helps detect these sophisticated campaigns early. By monitoring for unauthorized changes in digital footprints and identifying malicious indicators across the web, we act as an extra layer of defense when the “official” source is compromised.
The supply chain is the new frontline. While attackers are getting more surgical, Phishfort is here to ensure that the bond of trust between a brand and its users remains unbreakable.
Cybersecurity Industry FAQ: Expert Insights
Q: What is the first sign that my software supply chain has been compromised?
A: The most common early indicator is a discrepancy in binary signatures or unexpected network telemetry. For instance, in the Notepad++ incident, the updater process (GUP.exe) began spawning a custom binary (AutoUpdater.exe) that was not part of the standard installation. Monitoring for “parent-child” process anomalies in your developer tools is a critical first step.
Q: If I only use “Big Tech” vendors (Microsoft, AWS, Google), am I safe from supply chain attacks?
A: No. While these giants have massive security budgets, they are also the highest-value targets. Furthermore, your “Big Tech” stack relies on thousands of smaller open-source dependencies. As seen in the recent AgreeToSteal Outlook add-in news, attackers specifically target the “connectors” and “extensions” that bridge these platforms, as they often have lower oversight than the core products.
Conclusion: Staying Ahead of the Next Headline
The recent supply chain attack news serves as a critical reminder of the vulnerabilities inherent in our systems.
The era of “blind trust” in official sources is over. As we navigate the complex supply chain attack news of 2026, the only path forward is a combination of technical vigilance and proactive external monitoring. Whether you are a developer tool provider or an enterprise consumer, your security now depends on how well you can see beyond your own firewall.
Stay vigilant, verify your downloads, and let’s build a safer web together.
By learning from past incidents highlighted in supply chain attack news, companies can strengthen their defenses.
Is your brand’s distribution infrastructure being monitored? Protect your reputation with Phishfort’s Takedown and Brand Protection Services.



