Key takeaways
More than 30 WordPress plugins were compromised through a long-term supply chain attack.
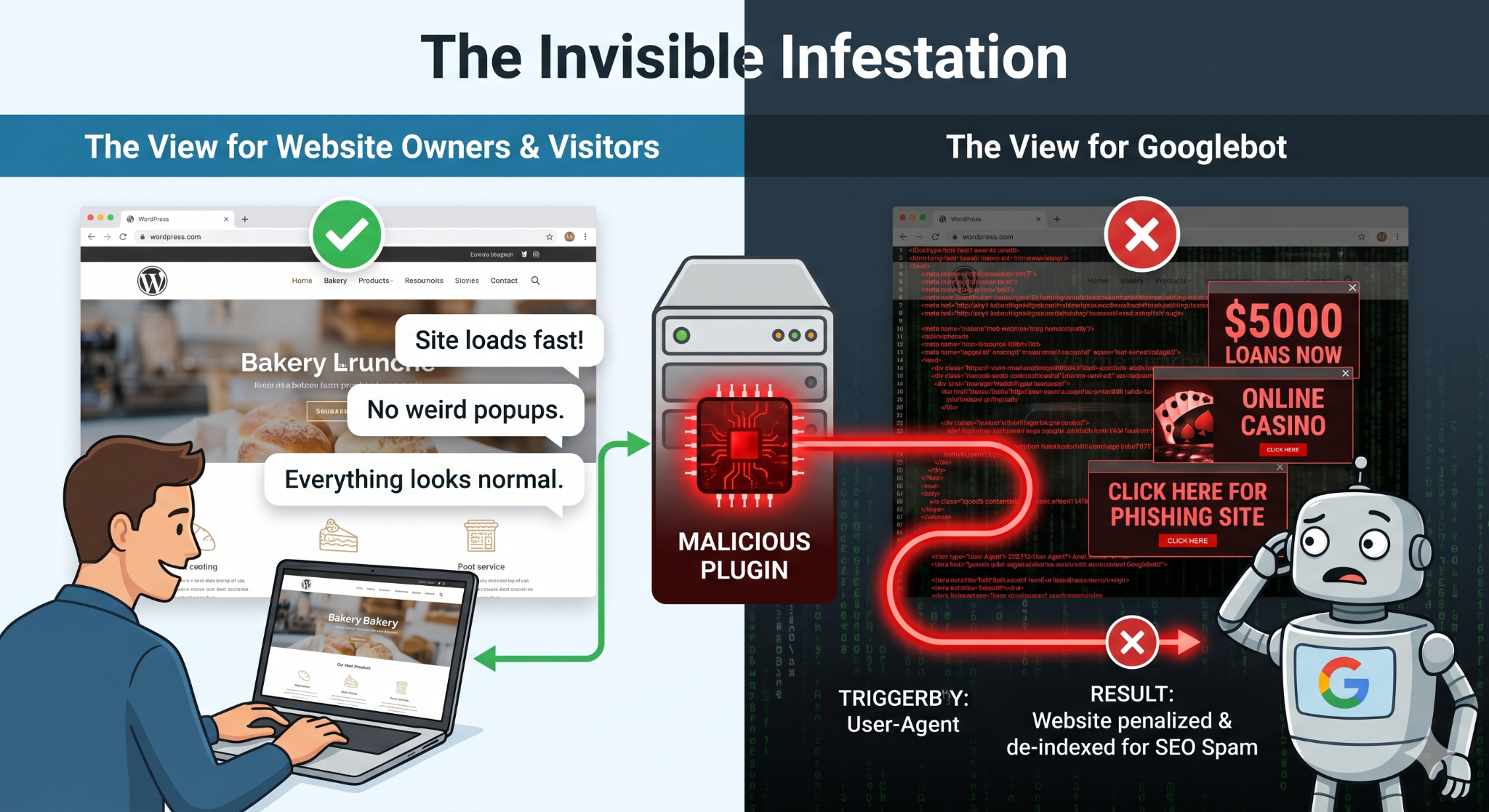
The malware used cloaking techniques to hide spam injections from site owners while targeting Googlebot.
Traditional takedown methods were weakened because the command-and-control infrastructure relied on Ethereum smart contracts.
Imagine locking all your doors and windows, only to realize you gave a copy of your house key to a stranger months ago. That is essentially what happened to website owners running any of the 30+ WordPress plugins recently compromised in a sophisticated supply chain attack.
On Wednesday, reports surfaced that a malicious actor had gained unauthorized access to websites running these plugins by utilizing a backdoor planted nearly a year ago.
The compromise affects plugins with hundreds of thousands of active installations, meaning the scale of potential victim sites is massive.
The Slow-Burn Attack: How It Happened
Unlike hacks that immediately break a site, this attack was a strategic “long con.”
- The Acquisition: The story begins around August 2025. A new owner acquired the “EssentialPlugin” package in a public six-figure deal on Flippa.
- The Plant: Almost immediately after the acquisition, a sophisticated backdoor was injected into the code.
- The Updates: The malicious code lay dormant for months. Then, recently, the attacker began pushing updates to users containing the activated code.
- The Activation: Once updated, the plugins began contacting a command-and-control (C2) server, generating hidden spam pages and forcing unwanted redirects.
The compromise was discovered by Austin Ginder of Anchor Hosting, who investigated one add-on after receiving a tip. He discovered the code was highly sophisticated.
“It only showed the spam to Googlebot, making it invisible to site owners”, Ginder explained.
Why This Attack Is Unique and Dangerous
This wasn’t a standard hack. It employed two tactics that make it incredibly difficult to detect and stop:
1. Invisible “Cloaking”
The malware was designed with SEO (Search Engine Optimization) spam in mind. When you, as the owner, or a regular visitor, load your website, everything looks perfectly normal. However, when Google’s indexing bot (Googlebot) visits the site, the malware serves up hundreds of fake pages, payday loan links, or gambling redirects.
While your site looks fine to you, Google sees a hotbed of spam and may de-index or penalize your domain, destroying your hard-earned rankings.
2. The Unstoppable “Phone Home” Mechanism
This is the wildest part of the report. Traditional malware relies on a static domain or IP address to receive instructions (a C2 server). Authorities can take those domains down to kill the malware.
In this case, the attacker resolved their command-and-control domain through an Ethereum smart contract.
The malware queries the public blockchain to find out where to send the stolen data and where to get the spam content. Traditional domain takedowns will not work here. The attacker could simply update the smart contract to point to a new domain at any time, keeping the botnet alive indefinitely.
The malicious code had been concealed inside wp-config.php.
It originated from the plugin’s wpos‑analytics module, which contacted analytics.essentialplugin.com, downloaded a backdoor named wp-comments-posts.php (intentionally mimicking the legitimate wp-comments-post.php), and used it to inject a large block of PHP into wp-config.php.
The injected payload was highly advanced. It pulled spam links, redirects, and fake pages from a remote command‑and‑control server, but only displayed them to Googlebot — keeping the activity hidden from site owners.
The Systemic Issue
This incident highlights a major “trust problem” in the WordPress ecosystem. WordPress.org currently has no mechanism to flag or review plugin ownership transfers.
When a trusted plugin changes hands, there is no “change of control” notification to users, and no mandatory code review is triggered. In this case, eight months passed between the backdoor being planted and being caught.
What You Must Do Now
Even if you have updated to the latest version of these plugins, you may not be safe.
WordPress.org did release update v2.6.9.1, which neutralized the “phone-home” mechanism. However, Ginder notes that this did not clean the existing infestation.
“The SEO spam injection was still actively serving hidden content to Googlebot,” writes Ginder.
If you believe you may have been using one of the affected plugins from the EssentialPlugin package:
- Auditing is required: Do not assume that an update alone fixed the issue. You must audit your WordPress file structure, specifically checking for malicious injections inside your wp-config.php file.
- Monitor Search Console: Keep a close eye on your Google Search Console for sudden indexing anomalies or reports of malicious content that you cannot see visually on your site.
Stay vigilant. Trust, but verify, every update in your dashboard.



