In the modern digital economy, trust is the most valuable currency. However, as we move into 2026, that trust is being systematically undermined by domain spoofing. This sophisticated form of cyber-impersonation allows attackers to hijack a brand’s reputation to deceive customers, steal sensitive data, and disrupt business operations.
For security leaders and brand managers, understanding the mechanics of these attacks is no longer optional; it is a foundational requirement for digital risk protection.
Understanding the Landscape: What is Domain Spoofing?
At its core, domain spoofing occurs when a threat actor uses a fraudulent domain or email address to impersonate a legitimate organization. The goal is to make a communication or a web page appear as if it originated from a trusted source.
By exploiting the inherent “human-in-the-loop” vulnerability, attackers bypass traditional perimeter defenses. Whether it is a pixel-perfect replica of a login portal or an email that appears to come from a C-suite executive, the objective remains the same: deception at scale.
The Mechanics of Deception: How Domain Spoofing Works
Domain spoofing works by exploiting technical loopholes in internet protocols or by using visual trickery to fool the human eye.
Email Header Manipulation: Attackers forge the “From” address in an email header. Without proper authentication protocols like DMARC, most email clients will display the spoofed name, leading the recipient to believe the message is internal or from a verified partner.
DNS Poisoning: This is a more technical approach where attackers corrupt the Domain Name System (DNS) cache to redirect traffic from a legitimate URL to a malicious IP address.
Visual Impersonation: This involves registering domains that are visually nearly identical to the target. For example, using
rnicrosoft.com(with an ‘r’ and ’n’) instead ofmicrosoft.com.
Common Types of Domain Spoofing
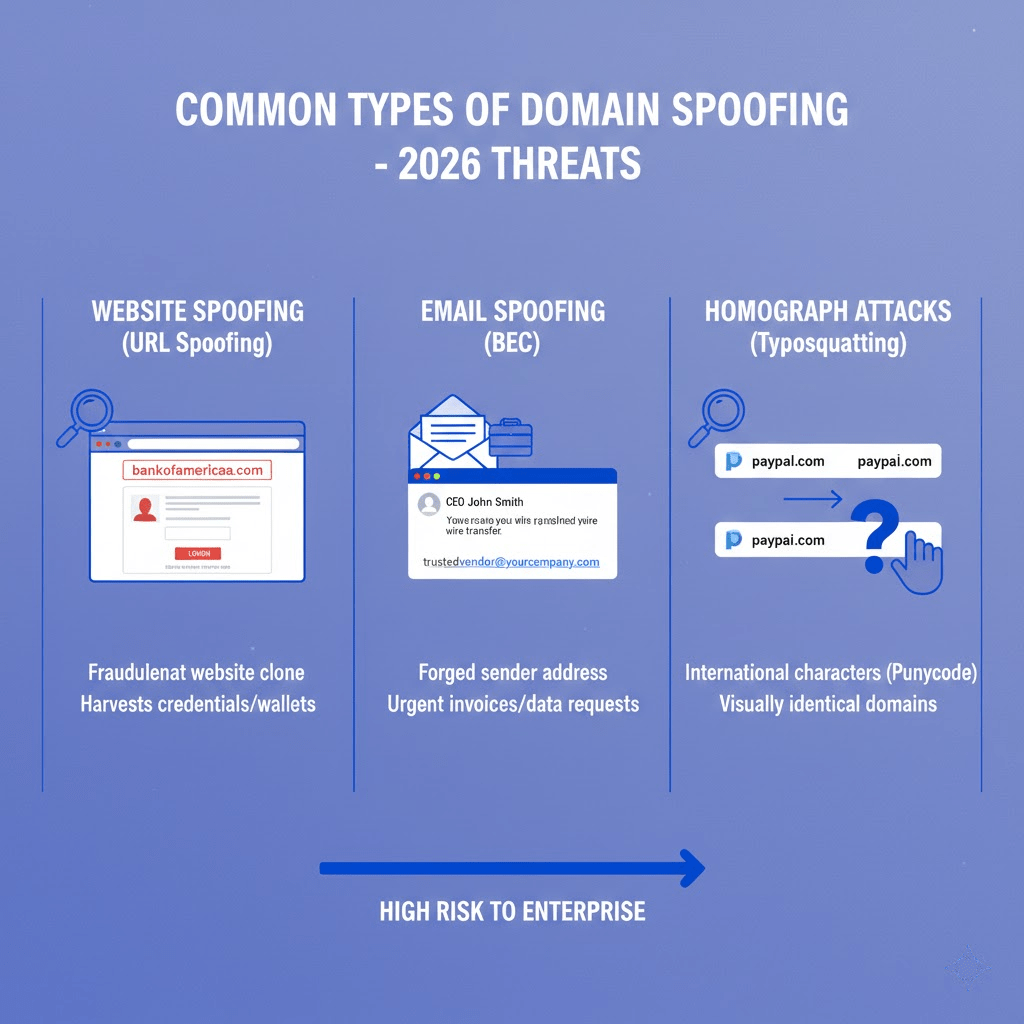
Not all spoofing attacks are created equal. In 2026, we see three primary variations that pose the highest risk to enterprise organizations:
1. Website Spoofing (URL Spoofing)
Attackers create a fraudulent website that mirrors the look and feel of a legitimate site. These are often used in tandem with fake login pages to harvest credentials or banking information. In the Web3 space, these “clones” are frequently used to drain crypto wallets.
2. Email Spoofing
This is the cornerstone of Business Email Compromise (BEC). By spoofing a domain, an attacker can send “urgent” invoices or requests for data that appear to come from a trusted vendor. According to recent FBI IC3 reports , BEC remains one of the most financially damaging categories of cybercrime.
3. Homograph Attacks (Typosquatting)
Using international characters (Punycode) or slight misspellings, attackers register domains that look identical to yours. To a user on a mobile device, paypaI.com (with a capital ‘I’) is indistinguishable from paypal.com.
The Triple Threat of Email Authentication: SPF, DKIM, and DMARC
To combat domain spoofing, organizations must implement a “Trinity” of authentication standards. These protocols are no longer just “best practices” — major providers like Google and Yahoo now require them for bulk senders to prevent domain-related takedowns .
SPF (Sender Policy Framework): A DNS record that lists which mail servers are authorized to send email on your behalf.
DKIM (DomainKeys Identified Mail): Adds a digital signature to emails, ensuring the content hasn’t been tampered with in transit.
DMARC (Domain-based Message Authentication, Reporting, and Conformance): Tells receiving servers what to do if an email fails SPF or DKIM (e.g., “reject it” or “quarantine it”).
Moving Toward Proactive Defense with PhishFort
Relying on reactive measures is no longer sufficient. Threat actors can spin up spoofed domains in minutes. To maintain a secure posture, brands need a partner that combines automated detection with human-led intelligence.
PhishFort provides 24/7 monitoring across the open web, social media, and app stores. When a spoofed domain is detected, our Takedown engine works at the registrar and host level to neutralize the threat before it can impact your users.
Expert Insights: Domain Spoofing FAQ
What is the difference between domain spoofing and phishing?
While often used together, they are distinct. Phishing is a broad category of a fraudulent attempt to obtain sensitive information. Domain spoofing is the specific technique used to make that attempt look legitimate by faking a domain or email address. You can have phishing without spoofing (using a random Gmail address), but spoofing is what makes phishing highly effective.
How can I tell if a website is spoofed?
High-level spoofing is difficult to spot. However, signs include slight misspellings in the URL, a lack of a padlock icon (though many spoofed sites now use SSL), and “off” branding or low-resolution logos. For enterprises, the only reliable way to protect users is through Brand Monitoring that identifies these sites the moment they are registered.
Can SSL certificates prevent domain spoofing?
No. An SSL certificate only encrypts the connection between the user and the server; it does not verify that the server itself is legitimate. An attacker can easily obtain a free SSL certificate for a spoofed domain (like g00gle.com), making the site appear “secure” to the average user.
Final Perspective
Domain spoofing is a direct assault on your brand’s integrity. As attackers utilize AI to generate more convincing fraudulent content, the window for detection and response is shrinking. By combining robust email authentication with proactive Digital Risk Protection, organizations can turn the tide against impersonation.
Is your brand being impersonated? Contact our team today to run a domain audit and secure your digital perimeter.



